880,000 Leaked Credentials Tied to 50 of the World’s Leading Companies in Q2 2025


NEW YORK, NY, November 3, 2025—Social Links, a global leader in open-source intelligence (OSINT) solutions, in partnership with ParanoidLab, releases the Report on Data Leaks among 50 of the World’s Leading Companies.
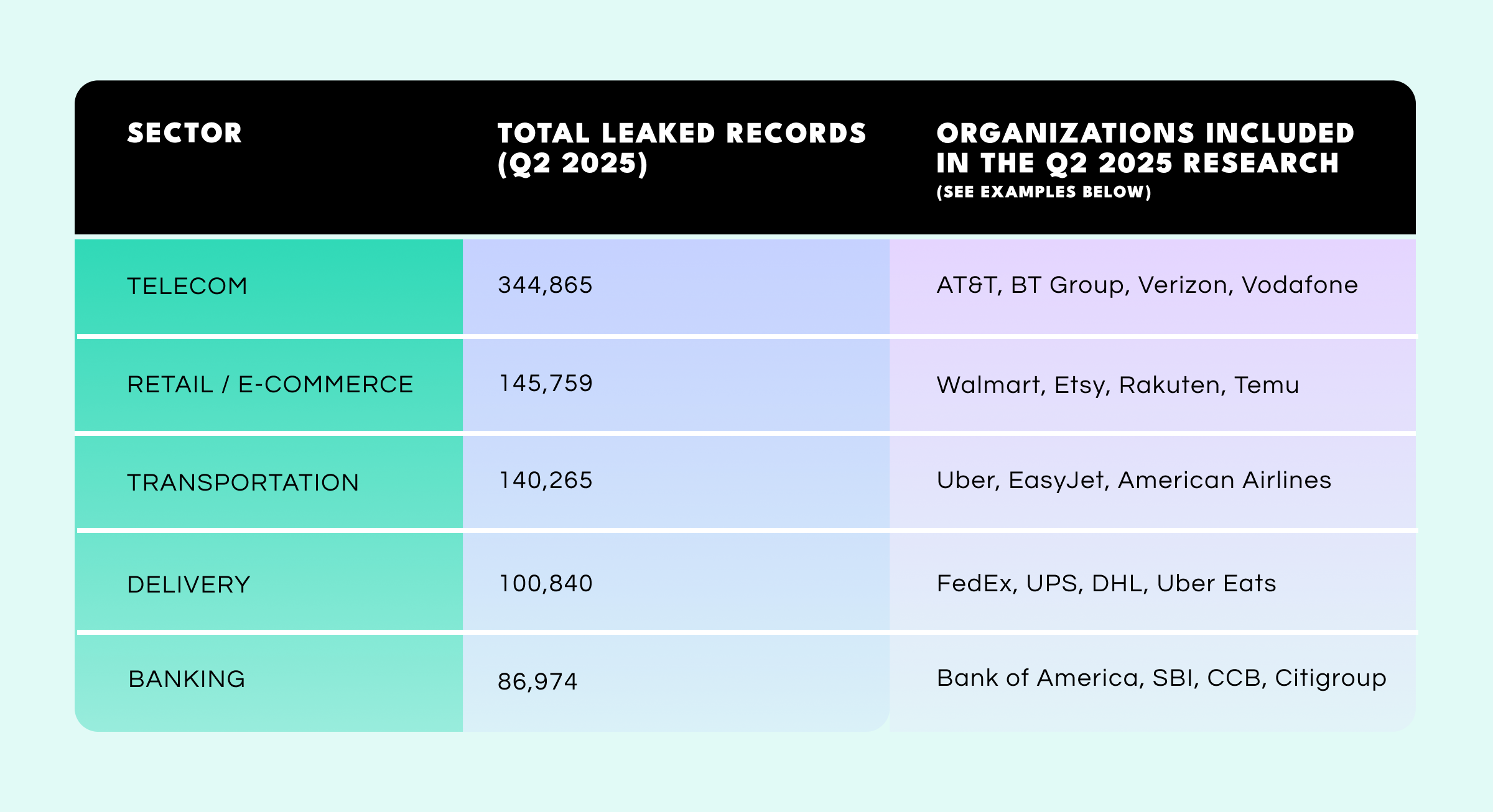
Analyzing 879,654 leaked user credentials (both corporate and external),* collected in Q2 2025, the report highlights companies on whom there is publicly available data about their user base. The analysis spans high-risk sectors such as telecommunications, banking and finance, mobility and delivery platforms, e-commerce and retail, and transportation.

Among the leaked credentials collected, 263,669 records contained corporate domain addresses (e.g., name@company.com), indicating corporate accounts, while 615,986 were linked to external user accounts.
The report found that the total number of leaked records varied significantly by sector. Telecom companies faced the largest overall exposure with over 344,000 leaked credentials in Q2 2025—a situation driven by major breaches at AT&T, BT Group, and Verizon.
Retail and e-commerce companies followed with 145,000 leaked records, led by platforms like Walmart, Etsy, and Rakuten. The transportation sector also saw heavy exposure (140,000+), particularly among ride-hailing and airline operators such as Uber and EasyJet.
While banks showed a lower total breach volume (86,000 leaked credentials), institutions like SBI and China Construction Bank reported alarmingly poor password hygiene, compounding their risk. The delivery sector—including FedEx, UPS, and Uber Eats—accounted for over 100,000 leaked records, highlighting the vulnerability of logistics and address-sensitive platforms.
Sectors with the highest volume of leaked external accounts (e.g. user accounts) in Q2 2025:
Only 26.5% of all passwords in the report met high-security criteria,** with most still relying on basic entries such as “password”, “123456”, or “admin”. Among internal credentials (including corporate accounts), the proportion of weak passwords ranged from 71% to 92% depending on the industry, emphasizing that human-factor risk is not just a theoretical concern but a daily entry point for attackers.
This surge in leaked credentials reflects the growing capabilities of AI tools in breaching systems through human vulnerabilities. AI has driven a massive 1,265% increase in phishing attacks, with AI-generated phishing emails now making up over 80% of such attacks. And such trends show no sign of abating with the cost of Generative AI-related fraud projected to rise from $12.3 billion in 2023 to $40 billion by 2027. These AI-powered attacks are becoming increasingly sophisticated, often automating personalization at scale, allowing cybercriminals to exploit weak access points and bypass traditional defenses more effectively than ever before.
“The most important turning point I want the industry to recognize is this—we’re no longer protecting machines; we’re protecting people,” said Ivan Shkvarun, CEO & Co-founder Social Links, and Author of Darkside AI Initiative. “As digital attack tools evolve from automated phishing kits to scalable impersonation tactics, it’s easier than ever to exploit human behavior at scale. It’s not your infrastructure that’s being hacked—it’s your employees, your users, your customers. And the uncomfortable truth is that right now, no one is truly protected. The scale of these attacks will only grow—unless we adapt. That’s why we need to rethink cybersecurity from the ground up and build modern digital risk protection around the individual.”
The full report on Data Leaks Among the World’s Leading Companies (Q2 2025) is available upon request.* The leaked credential records analyzed in the report were obtained from infostealer logs and combo lists sourced via public and private Telegram channels, darknet forums, and private intelligence feeds. All analysis is based solely on publicly available and leaked datasets.
** “High-security” password classification in the report is based on technical strength criteria only. A password is classified as high-security if it meets all of the following conditions. It must: (1) be at least 12 characters in length; (2) include at least three of four character types (lowercase letters, uppercase letters, digits, symbols); (3) not be composed solely of digits or solely of letters; and (4) not contain commonly known weak patterns. This classification does not assess password reuse, MFA usage, or behavioral risk.
About Social Links
Social Links is a global provider of open-source intelligence (OSINT) solutions, recognized as an industry leader by Frost & Sullivan. The company is headquartered in the United States and has an office in the Netherlands.
Bringing together data from 500+ open sources covering social media, messengers, blockchains, and the Dark Web, Social Links helps users visualize and analyze a holistic informational picture and streamline investigations. Their solutions facilitate essential processes across various sectors including law enforcement, national security, cybersecurity, due diligence, banking, and more.
Companies from the S&P 500 and public organizations from more than 80 countries rely daily on Social Links products.
About ParanoidLab
ParanoidLab is a cybersecurity data provider specializing in the collection, verification, and analysis of leaked credentials and threat intelligence. The company supports enterprises, researchers, and security professionals with reliable datasets that help identify vulnerabilities, monitor digital risks, and strengthen protection against cyberattacks.