Following the Money: From AML Compliance to Financial Intelligence


Financial institutions face a constant challenge: detecting criminal funds hidden among billions of legitimate transactions. Anti-money laundering (AML) programs exist to identify these illicit flows before they circulate freely through the global financial system. Yet many organizations still treat AML as a compliance exercise rather than an intelligence capability—and that distinction matters.
In this article, we examine how modern AML programs operate, the regulatory frameworks shaping financial crime prevention worldwide, and how institutions move beyond checkbox compliance toward intelligence-driven detection. We also explore the AML investigation process and how effective programs integrate customer due diligence, transaction monitoring, and investigative response into a coordinated defense against financial crime.
Money laundering is the process of disguising illegally obtained funds so they appear legitimate. Criminal organizations depend on laundering schemes to move profits from fraud, corruption, drug trafficking, cybercrime, and other offenses into the formal financial system.
Although laundering techniques vary widely, most schemes follow a similar progression designed to distance illicit funds from their criminal origin.
Placement. Illicit funds are introduced into the financial system through deposits, purchases, wire transfers, or other financial transactions. At this stage criminals attempt to move cash or other proceeds into accounts or financial instruments that allow the funds to circulate more freely.
Layering. Funds move through complex transaction chains intended to obscure their origin. Transfers across multiple accounts, financial institutions, shell companies, or jurisdictions create layers that make the money trail difficult to follow.
Integration. Once the origin of funds is sufficiently obscured, the money is reintroduced into the legitimate economy. Criminal proceeds may appear as investments, business revenue, real estate purchases, or other seemingly lawful activity.
Anti-money laundering controls are designed to disrupt this process at each stage. Through customer verification, transaction monitoring, and investigative analysis, AML programs aim to uncover suspicious financial patterns before illicit funds circulate freely through the financial system.
Most financial institutions operate AML programs, but those programs do not all function at the same level of effectiveness. In practice, AML capabilities evolve over time. Organizations typically begin with compliance-driven controls, gradually introduce risk-based monitoring, and eventually develop intelligence-led approaches focused on identifying criminal networks rather than simply meeting reporting requirements.
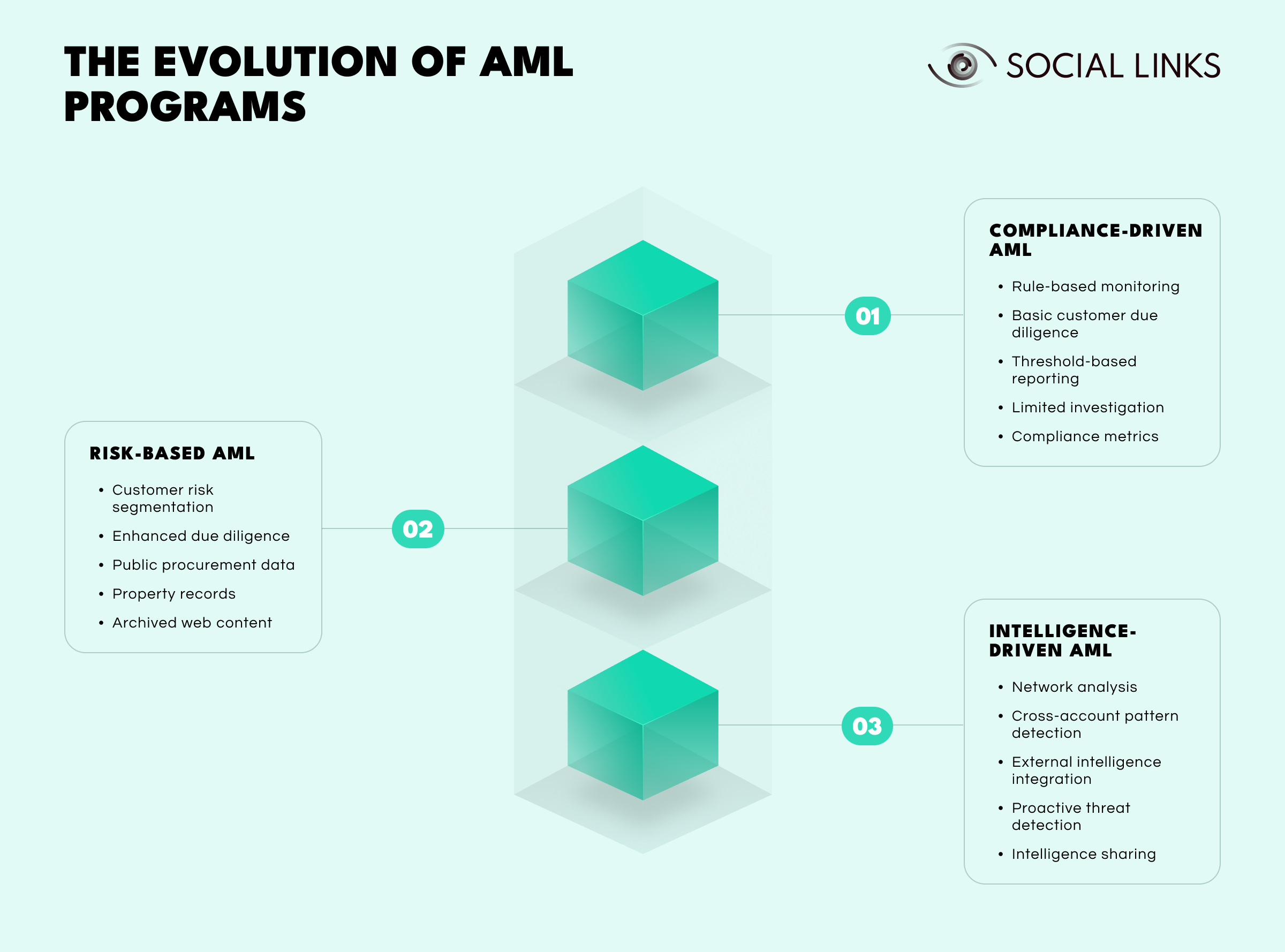
At the most basic level, AML programs are designed primarily to satisfy regulatory obligations. Monitoring systems generate alerts when predefined thresholds are triggered, analysts review those alerts, and suspicious activity reports are filed when required.
Typical characteristics include:
This approach ensures institutions meet legal requirements, but it also produces large volumes of alerts investigators must review manually. Because monitoring rules are generic and threshold-driven, false positives are common and analysts spend significant time reviewing legitimate activity.
At the same time, sophisticated laundering schemes may pass through unnoticed if they do not match predefined monitoring scenarios. AML at this stage functions largely as a compliance obligation rather than a financial crime detection capability.
As AML programs mature, institutions begin calibrating their controls based on customer risk. Monitoring rules and due diligence procedures are adjusted according to factors such as industry exposure, geographic risk, and transaction behavior.
Programs at this stage typically introduce:
This approach allows institutions to allocate investigative resources more efficiently. Alerts generated by monitoring systems are more likely to represent genuinely unusual activity because monitoring rules consider customer profiles and expected behavior.
However, detection remains largely reactive. Monitoring still relies heavily on predefined rules, meaning sophisticated actors can structure transactions in ways that avoid triggering alert scenarios.
At the most advanced level, institutions treat AML as an intelligence capability rather than simply a monitoring function. Investigators analyze patterns across accounts, transactions, and entities to identify coordinated financial activity.
Organizations operating at this level introduce capabilities such as:
Instead of reviewing alerts individually, analysts examine relationships across accounts and entities. Shared identifiers, transaction flows, and beneficial ownership links can reveal coordinated laundering activity invisible in traditional monitoring systems.
Developing intelligence-driven AML capabilities requires investment in data infrastructure, analytics, and investigative expertise. Institutions operating at this level understand that the purpose of AML is not simply filing reports—it is identifying and disrupting financial crime networks.
Consider two banks detecting the same suspicious wire transfer pattern.
Transaction monitoring flags the activity. An analyst confirms the threshold is exceeded, a suspicious activity report is filed, and the case is closed.
The same alert triggers network analysis revealing multiple related accounts showing similar patterns. Investigators uncover shell company structures and beneficial ownership connections. Intelligence is shared with authorities, related accounts are closed, and monitoring rules are updated based on the scheme.
The initial alert is identical. The outcome is not.
What matters is the kind of AML program behind the response.
Anti-money laundering regulations exist worldwide, with most jurisdictions aligning their frameworks to international standards.
The Financial Action Task Force (FATF) establishes global standards for anti-money laundering and counter-terrorism financing. Its 40 Recommendations form the foundation of AML regulation in more than 200 jurisdictions.
These standards require countries to:
Countries are periodically evaluated to determine whether these standards are effectively implemented.
While principles are globally aligned, implementation varies.
EU Anti-Money Laundering Directives (AMLD) establish common rules across member states and strengthen cooperation between national financial intelligence units.
AML obligations are governed by the Money Laundering Regulations and the Proceeds of Crime Act, with suspicious activity reports submitted to the National Crime Agency.
The Bank Secrecy Act and the USA PATRIOT Act form the core of US AML regulation. FinCEN collects suspicious activity reports and coordinates financial intelligence with law enforcement.
Financial centers such as Singapore, Australia, Hong Kong, and Japan maintain AML frameworks aligned with FATF standards and supported by national financial intelligence units.
Effective monitoring depends on understanding who customers are and what their expected activity looks like.
KYC procedures verify customer identity and assess risk before financial relationships begin.
Basic onboarding checks typically include:
Enhanced due diligence applies to higher-risk customers such as politically exposed persons or businesses operating in high-risk jurisdictions.
Identifying beneficial ownership is particularly important. Shell companies and layered corporate structures often conceal the individuals controlling financial accounts.
After identity verification, institutions assign risk ratings based on factors such as:
These profiles determine monitoring intensity. Without accurate profiling, monitoring systems generate alerts on routine activity while overlooking genuinely suspicious transactions.
After onboarding, institutions monitor activity for behavior inconsistent with expected patterns or indicative of money laundering. Monitoring systems typically combine rules-based detection with behavioral anomaly analysis.
Rules-based monitoring identifies red flags such as:
Anomaly detection models identify deviations from typical customer behavior—even when activity does not match predefined rules.
Effective monitoring is a balancing act. Systems that are too sensitive overwhelm investigators with alerts, while narrow monitoring allows genuine threats to slip through.
When suspicious activity is flagged, analysts must determine whether it requires regulatory reporting. The investigation process typically unfolds in several stages.
The first step is validating the alert. Many alerts reflect legitimate activity that simply matches monitoring scenarios.
Analysts review transaction details, account history, and customer profiles to determine whether the activity has a reasonable explanation.
If activity remains unexplained, investigators conduct deeper analysis.
They may:
Mapping relationships between individuals, accounts, and entities often reveals whether transactions form part of a broader laundering scheme.
If analysts conclude the activity may indicate financial crime, institutions file reports with their jurisdiction’s financial intelligence unit.
These reports—known as SARs, STRs, or SMRs depending on the jurisdiction—alert authorities to potentially illicit financial activity.
Importantly, filing a report does not confirm a crime. It signals activity that warrants further investigation.
Institutions may also take actions such as:
The goal is managing risk while meeting regulatory obligations.
Technology allows institutions to analyze massive volumes of financial activity and surface suspicious behavior at scale through monitoring systems, investigation platforms, and network analysis tools.
Transaction monitoring systems continuously analyze transaction data and generate alerts when patterns match laundering indicators.
Case management platforms help investigators organize alerts, track investigations, document findings, and manage reporting workflows.
Network analysis and analytics tools reveal relationships between accounts, customers, and transactions, exposing coordinated activity that may not be visible in individual alerts.
These systems are only as effective as the data behind them. Poor data quality or fragmented systems can significantly limit detection capabilities.
Even well-resourced institutions face persistent obstacles.
Monitoring systems often generate more alerts than investigators can realistically review. False-positive rates above 90 percent are common.
Criminal networks constantly adapt, structuring activity to evade monitoring thresholds or exploiting new financial technologies.
Investigations require skilled analysts and time. Many institutions struggle to maintain sufficient investigative capacity.
Financial crime frequently spans multiple jurisdictions, but each institution sees only a fragment of the transaction network.
Several technological and regulatory developments are reshaping financial crime prevention.
Artificial intelligence and machine learning are improving detection accuracy while reducing false positives.
Public-private intelligence sharing initiatives are expanding, helping institutions identify coordinated financial crime networks.
Regulators increasingly focus on effectiveness—evaluating whether AML programs genuinely detect illicit activity rather than simply producing reports.
At the same time, digital assets and new payment technologies introduce additional laundering channels that institutions must learn to monitor.
Institutions that treat AML as an evolving intelligence capability rather than a compliance checklist will be better positioned to respond.
Effective anti-money laundering programs require more than regulatory compliance. They require the ability to identify patterns, investigate suspicious activity, and expose financial crime networks.
Institutions may operate compliance-focused programs, risk-based monitoring systems, or intelligence-driven detection capabilities. The difference lies in how well customer due diligence, transaction monitoring, investigative workflows, and analytics are integrated.
The strongest AML programs treat financial crime prevention not simply as a regulatory obligation, but as a core component of institutional security.
Anti-money laundering refers to laws and procedures designed to detect and prevent criminals from disguising illegally obtained funds as legitimate assets. AML programs help financial institutions identify suspicious activity, comply with regulatory requirements, and protect the integrity of the financial system.
The three levels are compliance-driven (focused on meeting regulatory minimums), risk-based (calibrated to actual customer risk), and intelligence-driven (proactively identifying financial crime networks). Organizations typically progress through these levels as their capabilities mature.
AML investigations begin when transaction monitoring systems flag suspicious activity. Analysts review the alert against customer profiles, gather additional data through internal records and external intelligence sources, and determine whether the activity warrants filing a suspicious activity report with regulatory authorities.
Know Your Customer procedures establish a baseline understanding of who customers are and what their expected activity looks like. This foundation is essential for effective transaction monitoring, as suspicious activity can only be identified relative to normal behavior for that customer.
Financial institutions use transaction monitoring systems to detect suspicious patterns, case management platforms to track investigations, and analytics tools for network analysis and pattern recognition. Effectiveness depends heavily on data quality and system integration.
Want to see how unified intelligence platforms support anti-money laundering investigations and financial crime detection? Book a personalized demo with one of our specialists and discover how SL Crimewall helps financial institutions correlate transaction data, investigate suspicious activity, and support AML compliance through structured analytical workflows.