Threat Intelligence and Incident Response: Building a Unified Defense


Most security teams today operate both threat intelligence and incident response functions. Yet having both capabilities does not automatically translate into stronger security outcomes. In many organizations, intelligence and response still operate separately—one focused on understanding threats, the other on containing incidents. The result is a familiar gap: response teams act quickly but often lack full adversary context, while intelligence insights arrive too late to influence operational decisions.
In this article, we examine how threat intelligence and incident response can move from parallel activities to a unified defensive capability, and how operational integration helps teams detect threats earlier, respond with greater precision, and continuously strengthen security through lessons learned from every incident.
Threat intelligence is the structured analysis of adversary behavior, attack patterns, and risk indicators used to guide defensive decisions. It transforms logs, alerts, malware samples, and external threat feeds into operational context.
Effective intelligence helps answer practical questions:
Intelligence creates value only when it influences action—when it shapes monitoring priorities, investigation focus, or defensive controls. Without that connection to operations, intelligence remains descriptive rather than operational.
Incident response is the structured process used to detect, contain, investigate, and recover from security incidents.
A typical response lifecycle includes:
Frameworks such as NIST SP 800-61 and ISO 27035 provide guidance for organizing these activities. Frameworks alone, however, do not guarantee integration. Without intelligence context, response teams may treat each incident as an isolated technical event rather than part of a broader adversary campaign.
When intelligence informs response, investigators can quickly distinguish between opportunistic attacks, reconnaissance activity, or coordinated intrusion efforts—and adjust priorities accordingly.
Most security programs operate at one of three integration stages.
Threat intelligence and incident response function independently.
Intelligence teams produce reports and track indicators. Response teams investigate alerts using predefined playbooks. Information exchange is limited, and findings rarely move consistently between teams.
As a result, the same adversary may appear across multiple incidents without anyone recognizing the pattern. Capabilities exist, but organizational learning remains limited.
At this stage, coordination improves.
Information moves between teams, but usually on request. Intelligence supports investigations as an additional input rather than an embedded capability, and response findings often require manual effort before becoming usable intelligence.
Progress is visible, but collaboration still feels procedural rather than natural.
Operational integration emerges when intelligence and incident response function as a single defensive system.
Intelligence directly shapes investigation priorities. Incident findings immediately refine detection rules and threat models. Metrics and objectives span both functions rather than optimizing them separately.
Security operations begin shifting from reacting to incidents toward continuously adapting to adversary behavior.
Many teams recognize the value of integration but struggle to achieve it in practice.
Threat intelligence teams may report through risk or strategy functions, while incident response sits within IT or operations. Each group optimizes for different outcomes, making collaboration inconsistent without shared ownership.
Modern security environments rely on numerous platforms—SIEM, EDR, threat intelligence systems, and case management tools. Without integrated workflows between them, analysts must manually transfer findings, creating friction that slows collaboration.
Strategic threat reporting often provides useful awareness but may lack direct relevance to monitoring or response decisions. Effective integration requires intelligence that answers operational questions: what to monitor, where attackers may move next, and how compromise typically unfolds.
Teams focused solely on restoring operations may close incidents quickly without extracting adversary insight. When lessons learned do not update detection or intelligence models, similar incidents tend to repeat.
If intelligence teams are measured by reports produced and response teams by containment speed, collaboration becomes secondary. Shared metrics—such as reduced attacker dwell time or fewer repeat incidents—encourage genuine integration.
Operational integration becomes visible in practice when threat intelligence and incident response form a continuous defensive cycle rather than separate activities. This cycle typically moves through four reinforcing stages: intelligence, detection, investigation, and hardening.
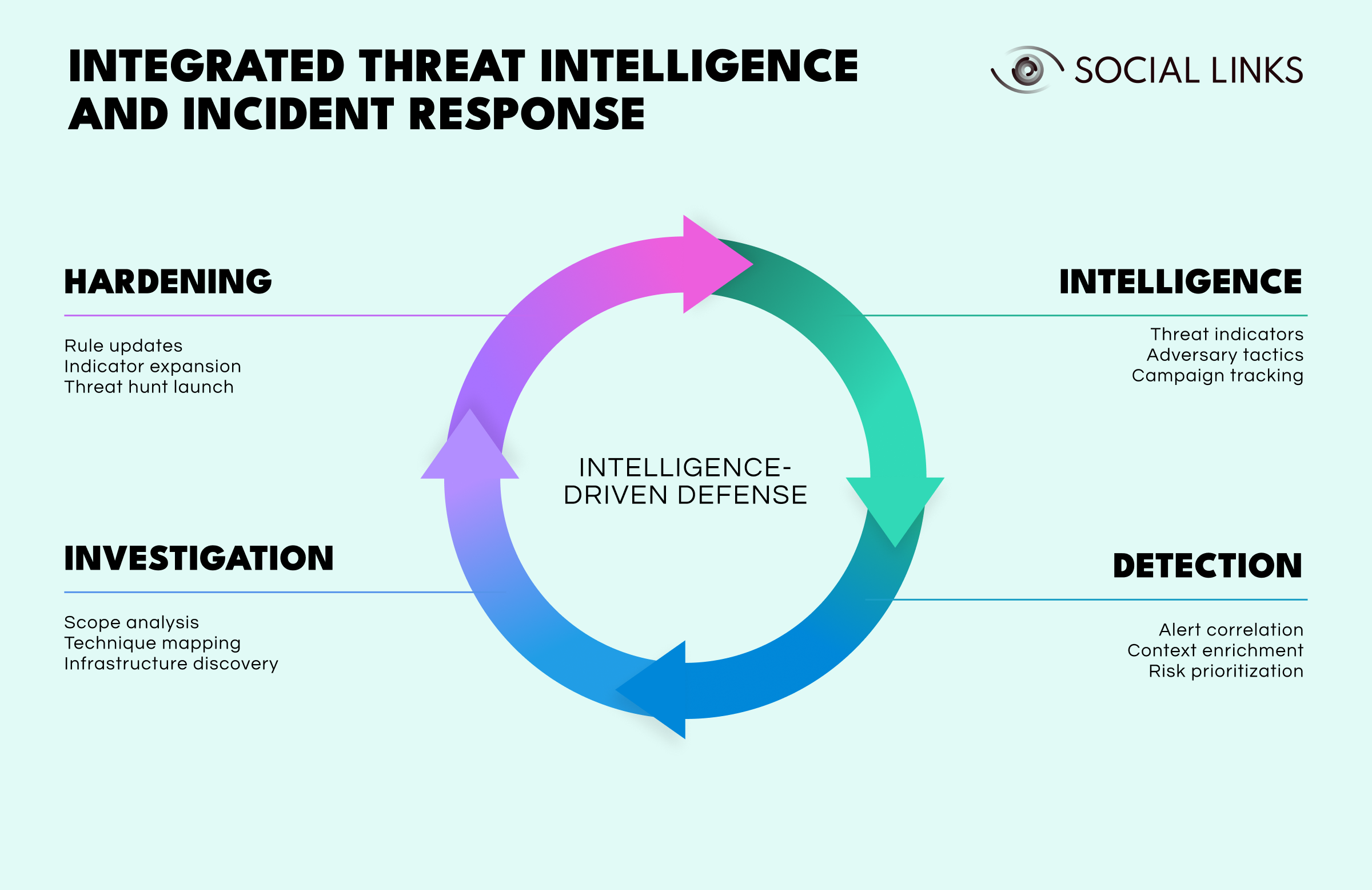
Intelligence provides visibility into threat indicators, adversary tactics, and active campaigns. This context shapes monitoring priorities and helps analysts understand emerging risks before alerts appear.
Detection applies that intelligence operationally. Alerts are correlated, enriched with context, and prioritized according to real organizational risk rather than technical severity alone.
Investigation determines scope and intent. Analysts map attacker techniques, uncover infrastructure, and understand how access was gained or expanded within the environment.
Hardening closes the loop. Detection rules are updated, indicators expanded, and threat hunts launched to identify similar activity earlier in the future.
Each incident therefore strengthens future defense. Intelligence informs detection and investigation, while investigation and hardening generate new intelligence for the next cycle. Security posture evolves continuously rather than resetting after containment.
Operational integration usually begins with deliberate workflow changes.
Tracking outcomes that require collaboration:
Embedding intelligence analysts directly within the Security Operations Center ensures that context is available during active incidents rather than after investigations conclude.
Automation reduces manual handoffs by enabling:
These integrations must remain reliable even during workload spikes or staffing changes.
Response playbooks should reference adversary behavior, while intelligence workflows should trigger proactive hunting and monitoring activities.
Technology enables integration but does not create it.
Tools are valuable only when they reduce friction between teams. Otherwise, silos simply migrate into software.
Several established frameworks support integrated operations:
ATT&CK is particularly valuable because intelligence and response teams can reference the same behavioral framework, improving coordination and analytical consistency.
Threat intelligence and incident response do not become integrated simply because both capabilities exist. Most security programs progress gradually—from siloed operations to coordination and eventually toward operational integration.
The difference lies in continuity. When intelligence actively shapes response decisions and incidents consistently improve future detection, security operations begin to learn and adapt over time.
Integrated defense reduces attacker dwell time, prevents repeat compromise, and turns incidents into opportunities for improvement rather than isolated disruptions. In practice, integration depends less on tools and more on workflows that connect intelligence, detection, investigation, and hardening into a continuous cycle.
Threat intelligence analyzes adversary behavior and risk indicators to inform defensive strategy, while incident response manages detection, containment, investigation, and recovery during active incidents. Integration ensures intelligence guides action and investigative findings improve future intelligence.
Integration provides context during incidents and ensures lessons learned strengthen detection capabilities over time. Without integration, teams respond effectively but fail to improve long-term defensive posture.
Organizations typically move through three stages: siloed operations, procedural coordination, and operational integration where intelligence and response function as a unified defensive cycle.
SIEM, SOAR, threat intelligence platforms, and unified case management systems can enable integration. However, workflow design and shared objectives remain more important than specific technologies.
Want to see how unified intelligence platforms support integrated threat detection and incident response? Book a personalized demo with one of our specialists and discover how SL Crimewall helps security teams correlate threat intelligence, accelerate response workflows, and continuously strengthen defensive capabilities.