Corporate Digital Forensics: When Evidence Determines the Outcome
When a data breach, insider threat, or employee misconduct incident occurs, companies face a choice. They can restore operations quickly and move on, or they can preserve evidence, reconstruct what happened, and build a record that will stand up to scrutiny. That choice often determines whether the organization can support legal action, defend itself in litigation, or even understand what actually took place.
In this article, we examine how forensic investigations support corporate decision-making, when businesses need them, and how investigation depth affects what can ultimately be proven. We also look at the technologies involved, how open-source intelligence strengthens internal cases, and what organizations should look for in a forensic provider.
Corporate digital forensics is the process of identifying, preserving, analyzing, and reporting digital evidence in a business context. The goal is not just to detect that something happened, but to reconstruct events, establish timelines, recover relevant data, and produce findings that support legal, regulatory, operational, or disciplinary action.
That makes forensic work different from routine IT troubleshooting. A forensic team does not simply restore access or fix a compromised device. It works to answer questions such as what happened, when it happened, which systems or accounts were involved, what data was accessed or moved, and what evidence can still be preserved. A single matter may require incident response, email analysis, insider threat investigation, and litigation support at the same time.
Forensics is not just for major cyberattacks. Businesses need forensic support whenever there is a serious dispute about digital activity and the facts need to be preserved rather than guessed at.
Common triggers include:
In each case, the risk is the same: if the company responds too casually, evidence may be lost. If it responds too aggressively without preserving context, it may weaken its own legal position.
Not all forensic investigations go equally far. Some focus on rapid containment with minimal evidence collection. Others expand into broader analysis across systems, accounts, and timelines. The strongest investigations produce records that can stand up to legal, regulatory, and executive scrutiny.
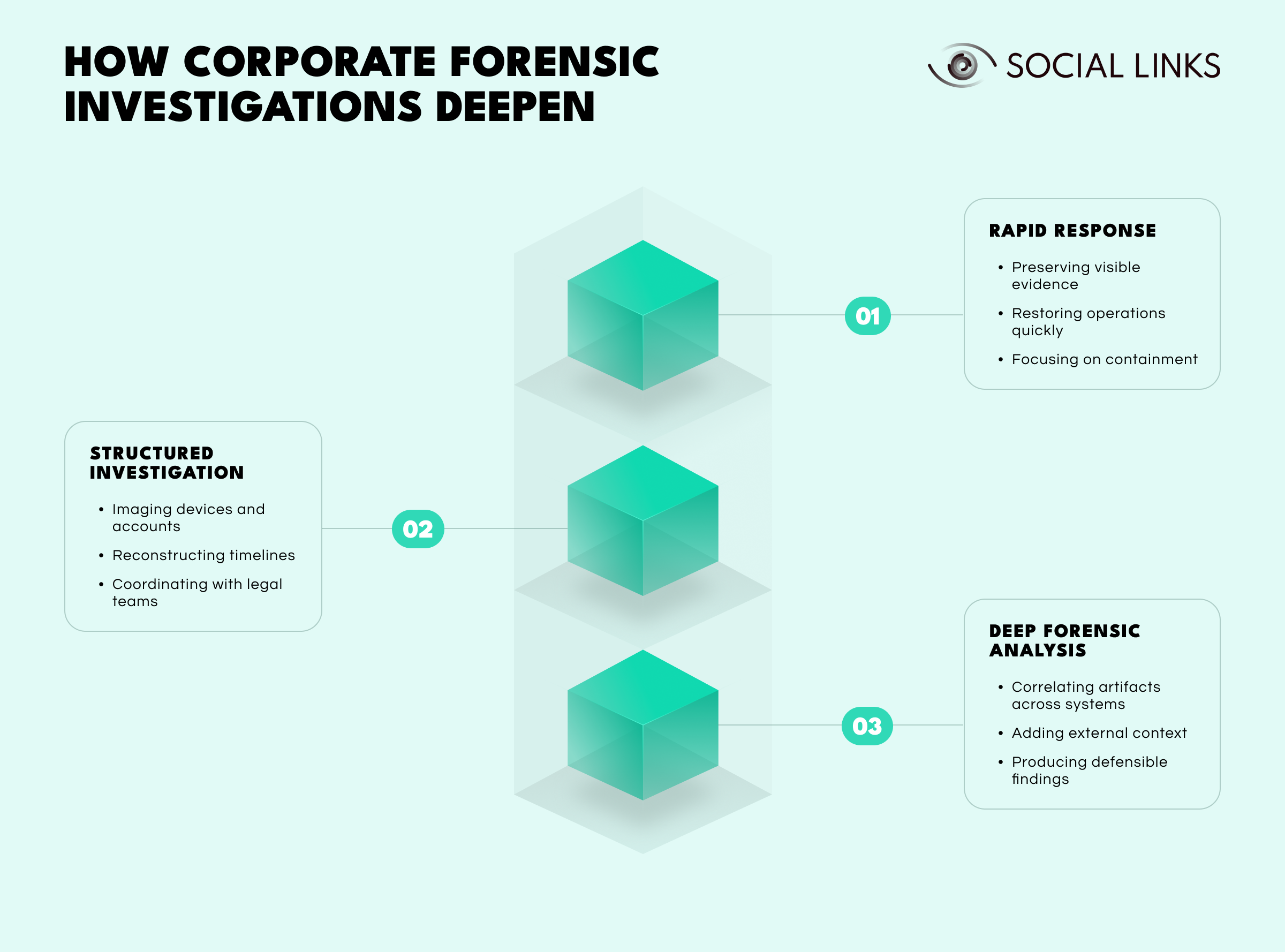
At the most basic level, organizations preserve immediately visible evidence and restore operations quickly.
This usually involves:
This works when the priority is operational recovery and legal exposure is limited. But it often leaves gaps. Volatile evidence may disappear, relationships between events may go unexamined, and the organization may not have enough documentation if the matter escalates.
As cases deepen, investigators conduct broader evidence collection and analysis.
This level often includes:
This level helps organizations understand not just what happened, but how events unfolded. Its main limit is that evidence may still be examined too narrowly rather than correlated across the wider environment.
At the most advanced level, investigators treat the case as a complex system requiring correlation across multiple data sources, timelines, and external context.
This level often includes:
Instead of examining each device or account separately, investigators map how artifacts connect. Communication patterns, file movements, authentication events, and external relationships often reveal coordinated activity or concealment that isolated analysis would miss.
Consider a company facing suspected intellectual property theft by a departing employee.
IT preserves the employee’s laptop and mailbox after departure. A review finds several technical documents in a personal folder. The files are flagged, but the organization has limited documentation of when they were accessed, whether they were transferred, or what happened next. When litigation begins, opposing counsel challenges the evidence handling and the company struggles to prove the timeline.
The same laptop and mailbox are forensically imaged before the employee departs. Investigators recover deleted emails showing discussions with a competitor. File system artifacts show the documents were copied to USB drives on three occasions. Cloud logs show uploads to a personal account. Mobile analysis, within policy limits, reveals coordination with the new employer. By the time the case reaches court, the organization has a defensible chain of evidence that can withstand scrutiny.
The suspicion is the same. What changes is the depth of investigation and the quality of evidence available when decisions have to be made.
Most work falls into a few recurring categories.
Incident and breach investigations. A company detects unusual activity, unauthorized access, suspicious downloads, or data exfiltration indicators. The forensic task is to determine scope, timeline, affected systems, and likely attacker behavior.
Internal misconduct and insider threats. These cases may involve unauthorized access to sensitive files, attempts to conceal activity, transfer of business data before resignation, or policy violations involving company devices.
Email and communication analysis. These are among the most common corporate needs and may involve fraudulent approvals, deleted messages, mailbox forwarding rules, suspicious attachments, impersonation, or disputes over who knew what and when.
Mobile device and endpoint analysis. Many corporate events now unfold partly on phones, laptops, tablets, and removable media. Investigators may need to examine device activity, app usage, messages, file movement, or location-linked evidence, depending on policy and legal scope.
Litigation and regulatory support. In these cases, the issue is not only whether evidence exists, but whether it was collected and handled in a way that can survive scrutiny from regulators, courts, auditors, or opposing counsel.
Strong corporate investigations usually follow a recognizable process.
Scoping the matter. The investigation begins by defining which users, devices, systems, and time periods matter, along with the legal, HR, and compliance constraints.
Preserving evidence. Before devices are wiped or accounts changed, relevant evidence must be preserved.
Collecting relevant data. Collection should be proportional to the allegation, the likely sources of evidence, and the risk of data loss.
Analyzing artifacts and timelines. Investigators review user actions, file movement, communications, device activity, and timestamps to build a coherent sequence of events.
Correlating internal and external context. Internal evidence becomes more meaningful when it is connected to public records, infrastructure signals, and outside activity.
Reporting findings. A strong report explains what happened in plain language, ties conclusions to evidence, distinguishes confirmed findings from informed judgments, and identifies the limits of the analysis.
Supporting action. Findings can support remediation, legal action, employee discipline, regulatory response, litigation, or negotiation.
The technology stack varies by case, but several categories appear repeatedly.
Endpoint and disk imaging tools preserve the contents of laptops, desktops, and storage devices without altering original data, supporting timeline reconstruction, deleted file analysis, and data recovery.
Email and collaboration analysis tools help investigators review mailbox structures, deleted items, metadata, attachments, forwarding rules, and communication patterns.
Cloud and log analysis is increasingly central because access logs, audit logs, admin actions, authentication events, and shared-drive activity often reveal more than local endpoints do.
Mobile and application forensics can reveal communications, app use, media artifacts, and synchronization behavior where policy and legal basis allow.
Link analysis and correlation platforms help investigators connect users, devices, timestamps, network indicators, and communications across datasets.
Data is not evidence merely because it exists. It becomes evidence when it is relevant, preserved properly, and interpreted in context. A corporate investigation may include system logs, email metadata and content, file access records, authentication events, web history, USB usage artifacts, chat messages, device activity records, cloud audit logs, geolocation-linked artifacts, and backup records.
The hard part is not just collecting those sources. It is understanding how they fit together. A deleted file may mean very little on its own. But if it appears alongside mailbox forwarding, login anomalies, and USB activity just before resignation, it becomes part of a coherent narrative.
Open-source intelligence does not replace internal evidence. It extends it. In a corporate case, OSINT may help investigators understand whether a suspicious domain is tied to known malicious infrastructure, whether a departing employee’s new company relationship was publicly visible, whether leaked credentials are circulating, or whether external accounts, aliases, or public posts align with internal events.
Open-source analysis can surface:
Its value is context. Internal evidence shows what happened inside the environment. OSINT helps explain the outside relationships, infrastructure, and timing that make those findings more meaningful. In some matters it can also validate or challenge assumptions, such as when a suspicious login looks external until public records suggest it maps to a third-party partner.
Even well-run companies encounter recurring problems.
Evidence volatility. Logs roll over, cloud artifacts disappear, devices are reset, and mailboxes change. Waiting too long can destroy the most valuable data.
Overcollection and undercollection. Some companies collect too much and create privacy or review problems. Others collect too little and lose critical evidence.
Internal sensitivity. Employee misconduct and insider threat investigations often involve HR, privacy, legal privilege, and employment law concerns.
Mixed environments. Evidence now lives across laptops, phones, cloud suites, chat tools, and third-party apps.
Interpretation risk. Artifacts do not interpret themselves. A forwarding rule, deleted file, or USB event may be suspicious, innocent, or ambiguous depending on timing and surrounding facts.
Choosing a forensic provider is not just about toolkits. It is about judgment, defensibility, and business awareness. A strong provider should be able to explain its collection methodology, preserve chain of custody, work comfortably with legal, HR, and compliance teams, handle cloud and endpoint evidence, and communicate clearly to non-technical stakeholders.
Ask practical questions. Have they handled employee misconduct cases? Can they support breach response and litigation support? Do they understand both incident response and internal fact-finding? A provider that is technically strong but blind to business realities will create friction fast.
One of the hardest parts of a corporate investigation is not preserving internal evidence. It is understanding what that evidence points to outside the company. A suspicious domain, an unfamiliar business relationship, a personal account, or a public-facing digital footprint may matter just as much as the laptop image or mailbox export, but those connections are often fragmented and time-consuming to map.
This is where Social Links adds value. When a forensic investigation surfaces an outside name, company, domain, account, or contact trail, investigators often need to move quickly from isolated artifacts to a broader picture of affiliations, public records, digital footprints, and related infrastructure. That kind of context can clarify whether an internal event is isolated, coordinated, or connected to wider external activity.
In practice, that matters in cases involving insider risk, corporate theft, data leaks, suspicious counterparties, or uncertainty about how an internal event connects to outside actors. Social Links helps investigators bring that outside layer into the case more quickly, so legal, HR, compliance, and security teams are not working from internal evidence alone.
Corporate digital forensics is not just about collecting artifacts. It is about producing evidence strong enough to support action when the stakes rise. The difference between a quick review and a deeper investigation is often the difference between suspicion and proof.
The strongest investigations do three things well: they preserve evidence early, reconstruct events clearly, and add enough context to explain what the technical record actually means. When organizations get that right, they are in a far better position to respond to incidents, investigate misconduct, support litigation, and make defensible decisions under pressure.
Corporate digital forensics is the process of preserving, analyzing, and reporting digital evidence in business investigations. It helps organizations understand what happened across devices, accounts, email, cloud systems, and other environments to support legal, HR, security, and executive decisions.
Businesses need forensic support when there is a serious dispute or incident involving digital activity—such as a breach, insider threat, fraud, employee misconduct, or litigation—and evidence must be preserved properly before it changes or disappears.
Forensic providers collect and analyze evidence from endpoints, email, cloud systems, mobile devices, and logs. They reconstruct events, recover relevant artifacts, and produce findings that can support legal, security, HR, and regulatory decisions while maintaining defensible evidence handling.
Open-source intelligence adds external context to internal evidence. It can help investigators connect aliases, domains, breach exposure, affiliations, and public records to the artifacts found inside a company investigation, providing context that makes internal findings more meaningful.
Companies should look for providers that combine technical capability with legal awareness, strong evidence handling, and the ability to communicate clearly. The best providers can support both urgent cyber incidents and sensitive internal investigations while maintaining evidentiary discipline.
Want to see how intelligence platforms support corporate investigations? Book a personalized demo with one of our specialists and discover how SL Crimewall helps investigators correlate digital evidence, analyze forensic artifacts, connect internal and external intelligence, and support incident response through integrated analytical workflows.