Corporate Investigations: From Case Handling to Risk Management


Corporate investigations are no longer limited to physical security, background checks, or post-incident response. For most organizations, the harder problem is broader: fraud, insider risk, misconduct, data leaks, third-party exposure, and reputational harm now cut across internal systems, financial records, employee behavior, and public-facing information at the same time. The challenge is not just identifying suspicious activity. It is establishing what happened, preserving evidence, and understanding how internal signals connect to outside people, entities, and risks.
In this article, we look at what corporate investigations actually involve, when businesses need formal investigations, which case types are most common, and how effective programs move from reactive case handling to proactive risk management. We also examine where forensic work, intelligence gathering, and OSINT fit into the process, and why modern investigation teams need more than isolated internal evidence.
Corporate investigations are the internal or external functions used to identify, assess, investigate, and reduce risks that could harm a business. These risks can include employee misconduct, fraud, insider threats, vendor risk, data theft, compliance failures, reputational exposure, and financial crime.
In practice, investigation programs usually draw on several capabilities at once. Depending on the case, that may include internal investigations, security services, risk and compliance work, due diligence, digital forensics, intelligence gathering, or fraud analysis. The structure varies by organization.
In some companies, investigations sit under the legal department. In others, they fall under corporate security, compliance, ethics, internal audit, or a dedicated investigations function. The reporting line matters less than the objective: protect the business, establish facts, and support defensible action.
A mature program usually serves three purposes. It helps prevent incidents by identifying weak points early. It investigates issues when risk becomes real. And it strengthens protection by reducing the chance that the same issue happens again.
Most organizations do not need a formal investigation every week. But when risk becomes sensitive, ambiguous, or potentially damaging, informal fact-finding stops being enough.
Common triggers include:
The reason is simple. Once the legal, financial, operational, or reputational stakes rise, assumptions become dangerous. A business may suspect wrongdoing, but suspicion is not enough to support discipline, litigation, disclosure, escalation, or remediation. At that point, the organization needs a structured way to preserve evidence, verify facts, and reach a defensible conclusion.
Many companies can detect that something looks wrong. Fewer can explain what it means.
An access anomaly may show up in logs. A suspicious payment may appear in finance records. A concerning communication may surface in email or chat. But those internal signals often do not answer the most important questions. Who is behind the outside company involved? Is a vendor connected to an employee? Does a personal account link to a competitor, a shell entity, or an undisclosed relationship? Is the event isolated, negligent, or deliberate?
This is where many investigations stall. The issue is not always a lack of data. It is a lack of context.
A strong investigation function closes that gap by combining internal evidence with forensic discipline, intelligence gathering, and external context. That is what turns a suspicious event into a clear picture of exposure.
Not all organizations handle investigations the same way. Some respond only after an incident becomes visible and focus on resolving the immediate problem. Others build more structured workflows, preserve evidence more carefully, and use what they learn from one case to reduce future risk. Over time, the difference is not just procedural. It changes what the investigation function is actually capable of seeing and doing.
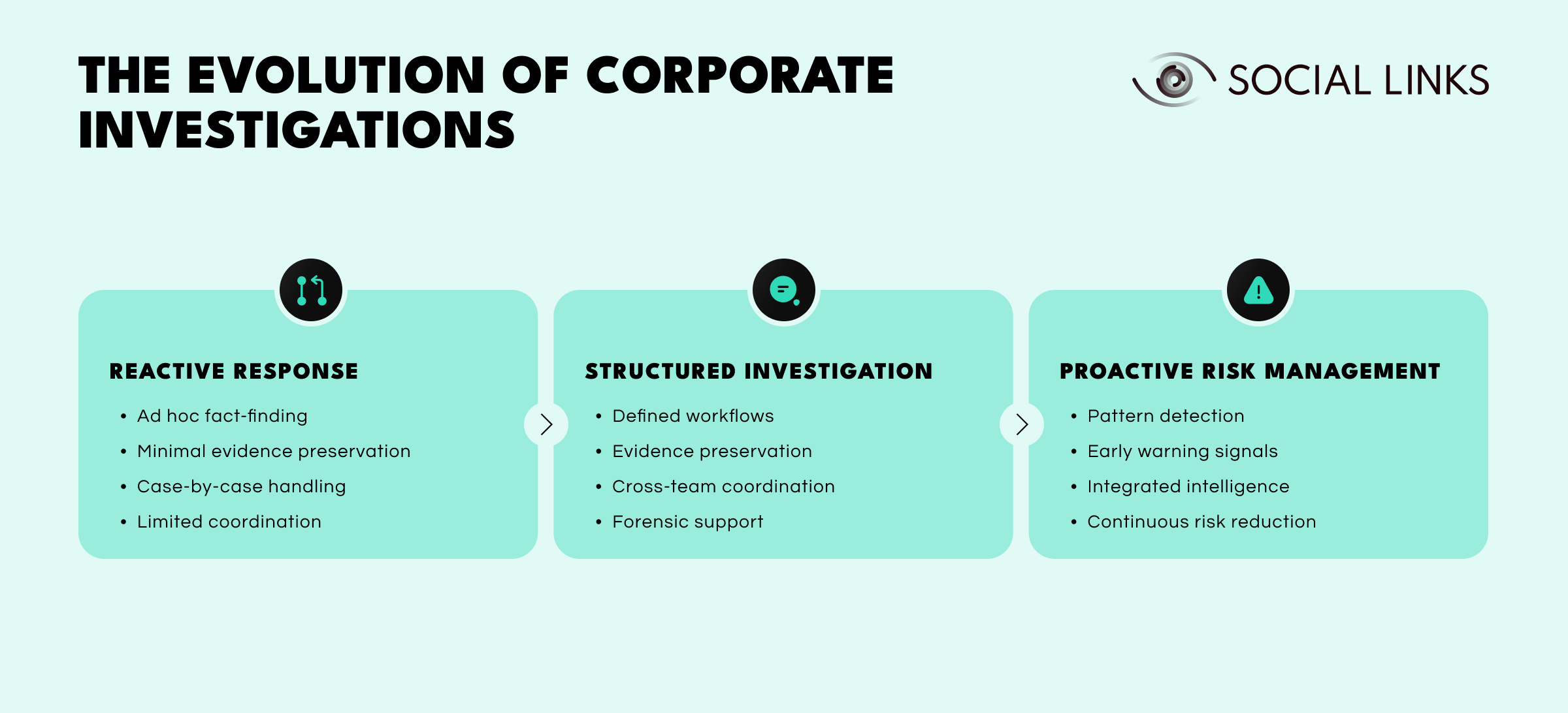
At the most basic level, companies investigate only after an allegation surfaces or damage becomes visible. The work is usually ad hoc and centered on resolving the immediate issue in front of the team.
This approach often includes:
That may be enough for simple matters, especially when the facts are obvious and the exposure is limited. But it creates avoidable risk when a case becomes complex, sensitive, or legally significant. Important evidence may be missed, timelines may remain incomplete, and the organization may never get beyond a surface-level explanation of what happened.
As investigation functions become more capable, organizations introduce clearer workflows, stronger evidence handling, and better coordination between legal, HR, IT, compliance, and security.
This usually includes:
At this stage, investigations become more defensible. The organization is better able to scope the matter, preserve what matters, review records systematically, and document findings in a way that can support internal action or outside scrutiny. But even here, many cases are still treated as isolated events. The organization may understand one incident well without asking whether the same conditions, controls, or relationships exist elsewhere.
The strongest programs use investigations not just to resolve cases, but to identify patterns, improve controls, and reduce future exposure.
At this level, teams begin introducing capabilities such as:
This is where the investigation function stops acting only as a response mechanism and starts contributing directly to broader risk management. Findings from one matter may trigger a review of similar vendors, repeated employee behaviors, weak approval chains, or overlooked third-party connections. Instead of closing the case and moving on, the organization uses the case to test whether the same exposure exists somewhere else.
The difference becomes clear in practice. A reactive program may handle a vendor fraud case, identify the immediate misconduct, and close the matter once the people involved are addressed. A more developed function will go further. It will ask whether similar vendor relationships exist elsewhere, whether the same procurement controls failed in other business units, and whether the case points to a broader pattern of weak oversight. What begins as one investigation becomes a source of insight about how the organization itself needs to change.
That shift matters. It turns investigations from a case-handling function into part of a broader risk management strategy.
Investigative maturity matters because corporate investigations rarely deal with just one type of problem. In practice, most cases fall into a handful of recurring categories, each with its own evidence profile and risk implications.
These cases often involve policy violations, harassment, retaliation, conflicts of interest, unauthorized access, or misuse of company systems. They usually require careful coordination with HR and legal because both evidence handling and employee rights matter.
Fraud cases may involve false invoicing, kickbacks, expense fraud, procurement abuse, embezzlement, payment diversion, or misuse of company funds. These often require financial review, document analysis, and digital evidence collection.
Insider risk is not limited to malicious actors. It may involve negligence, unusual access patterns, pre-departure file movement, risky behavior, or coordination with outside parties. Some cases turn out to be benign. Others reveal theft, sabotage, or data exfiltration.
Due diligence helps organizations assess counterparties, vendors, acquisition targets, key hires, and partners before risk becomes harder to control. In many cases, this is preventive investigation work rather than reactive response.
These cases may involve bribery, corruption, sanctions issues, procurement collusion, document falsification, theft, or coordinated misconduct affecting the business. They often require legal oversight from the beginning because exposure may extend to regulators, courts, or law enforcement.
Forensic investigation is used when evidence needs to be preserved, analyzed, and documented in a way that can support legal, regulatory, HR, or executive decisions. It is not just an IT review. Its purpose is to reconstruct events and produce a record strong enough to withstand scrutiny.
That work can include reviewing laptops and devices, analyzing mailboxes and cloud audit logs, tracing file access and transfer history, examining communication records, identifying USB activity, recovering deleted artifacts where possible, and reconstructing timelines across systems.
The difference is evidence quality. A routine review may suggest that something suspicious happened. Forensic work is designed to show what happened, when, how, and what can be proven.
That matters in cases involving data theft, litigation, insider risk, financial misconduct, regulatory review, or executive allegations. Without forensic discipline, evidence can be lost, altered, or challenged later.
A company notices unusual file transfers from an employee who recently resigned. Internal logs show large downloads from shared folders and activity outside normal working hours. On its own, that may look suspicious, but still ambiguous.
A structured investigation starts by preserving the employee’s devices, mailbox, cloud activity, and access history. Review shows that the employee forwarded business documents to a personal account and accessed files unrelated to their role. That is already serious.
But the full picture becomes clearer only when external context is added. Public records and open-source research show that the employee is linked to a newly formed company operating in the same market. Registry information, digital footprint analysis, and related business records suggest the new entity may be connected to a competitor or intended to operate as a vendor. What first appeared to be unusual file activity now looks like a possible theft and conflict-of-interest matter with outside exposure.
That is how investigations move from an internal signal to a defensible finding. Internal evidence starts the case. External context explains the risk.
Good investigations are not defined by one tool or one department. They are defined by process and discipline.
Most investigations follow a recognizable sequence:
Scoping the matter. Investigators define which people, systems, entities, accounts, and time periods matter, along with any legal, HR, and compliance constraints.
Preserving evidence. Before accounts are disabled, devices are changed, or logs expire, relevant evidence must be preserved.
Collecting relevant data. Collection should match the allegation, likely sources of evidence, and the risk of data loss.
Reviewing records and activity. Investigators analyze communications, documents, access history, financial records, and other relevant artifacts.
Adding external context. Internal evidence often becomes more meaningful when connected to public records, company affiliations, digital footprints, domains, business registrations, and outside activity.
Testing findings. Teams compare timelines, evidence, and explanations to determine what is confirmed, what remains uncertain, and where contradictions exist.
Reporting and action. Findings support remediation, HR decisions, legal action, regulatory response, escalation, or further review.
This process is straightforward on paper. In practice, the hard part is maintaining discipline when facts are incomplete and pressure is high.
Open-source intelligence does not replace internal evidence. It extends it.
In many corporate investigations, the hardest part is not spotting the internal signal. It is understanding what that signal connects to outside the company. A suspicious company name, unfamiliar domain, personal account, new vendor, or external relationship may matter just as much as an internal artifact.
Used properly, OSINT can help investigators identify beneficial ownership, review public records and business registrations, surface undisclosed affiliations or relationships, map digital footprints tied to people or entities, examine domains and infrastructure, and add context to counterparties, vendors, and third parties.
This is especially useful in due diligence, insider threat cases, fraud investigations, and matters involving outside entities. It helps teams move from internal suspicion to a broader understanding of exposure.
Even capable teams run into the same recurring problems.
Fragmented evidence. The facts rarely sit in one place. Communications, HR records, financial data, access logs, public records, and cloud activity may all live in separate systems.
Timing. Logs expire. Devices are reset. Accounts change. People leave. Delay destroys evidence.
Sensitivity. Many matters involve executives, whistleblowers, HR risk, legal privilege, or live regulatory exposure. That raises the standard for investigative discipline.
Ambiguity. Not every suspicious event is misconduct. Some cases only make sense once the surrounding context is understood.
Scale. Internal teams may not have the bandwidth or specialist capability to manage complex, overlapping, or high-risk matters on their own.
Not all investigation providers are built for the same type of work. Some are strongest in physical security. Others focus on fraud, digital evidence, due diligence, or intelligence.
When evaluating support, organizations should ask:
The right partner should do more than gather facts. They should help the organization make defensible decisions under pressure.
One of the hardest parts of corporate investigations is that risk rarely stays inside one system. A suspicious employee relationship, vendor connection, domain, account, or corporate entity may matter just as much as internal logs, emails, or file activity.
This is where Social Links adds value. When internal evidence points to an outside name, company, domain, or contact trail, investigators need to move quickly from isolated signals to a broader picture of affiliations, public records, digital footprints, and related infrastructure. Social Links helps teams bring open-source intelligence into the investigation workflow so they can connect internal evidence to outside entities faster and with more structure.
That is especially useful in cases involving:
Social Links does not replace evidence preservation or internal review. It helps investigators understand what internal evidence may actually mean beyond the company perimeter.
Corporate investigations are not just about reacting after damage is done. At their best, they help organizations establish facts, reduce uncertainty, and act before risk becomes harder to contain.
The strongest programs combine structured process, forensic discipline, intelligence gathering, and outside context. That matters because modern business risk rarely fits neatly into one category. Fraud, misconduct, insider risk, third-party exposure, and reputational harm often overlap.
Organizations that move from reactive response to structured investigation to proactive risk management are in a much stronger position to handle sensitive matters, improve controls, support legal decisions, and respond with confidence when the facts are unclear.
Corporate investigation services help organizations identify, investigate, and reduce risks involving misconduct, fraud, insider threats, vendor issues, data theft, and compliance failures. They combine investigative process, forensic work, and intelligence gathering to establish facts and support defensible action.
A business should conduct a formal investigation when a matter involves meaningful legal, financial, operational, or reputational risk. Common triggers include fraud, internal misconduct, data theft, suspicious third-party relationships, and compliance concerns.
Forensic investigation is a structured evidence-preservation and analysis process used when digital or financial facts need to be documented in a defensible way. It is especially important in cases involving litigation, insider risk, data theft, or regulatory review.
Compliance reviews may detect potential issues. Investigations go further. They are designed to establish facts in sensitive or high-risk matters and produce a basis for action.
An effective program moves beyond isolated case handling. It uses investigation findings to improve controls, identify patterns, reduce future exposure, and integrate investigation work into broader risk management.
Want to see how investigators connect internal signals to outside entities before risk spreads? Book a personalized demo and see how SL Crimewall helps teams map business relationships, examine digital footprints, and turn fragmented evidence into defensible findings through integrated OSINT workflows.