Cyber Crime and Digital Forensics: Investigating Beyond the Alert


A cyber crime investigation rarely starts with a dramatic reveal. More often, it begins with fragments: an unusual login, a suspicious process on an endpoint, unexpected outbound traffic, a deleted file, a phishing email, or a malware alert that does not yet make sense. The challenge is not just spotting that something is wrong. It is preserving evidence, reconstructing what happened, and connecting technical artifacts to a clear investigative narrative. That is where cyber crime and digital forensics become inseparable.
In this article, we examine how cyber investigation and forensics work together, what types of cases investigators handle, how digital evidence is collected and analyzed, which techniques matter most, and how OSINT strengthens modern investigations. We also look at the investigation process, common obstacles, and how organizations move from basic alert response to intelligence-led operations.
Cyber crime and digital forensics sit on the same continuum, but they serve different functions.
Cyber crime refers to malicious or unauthorized activity targeting systems, data, users, networks, or digital assets. This includes ransomware, phishing, credential theft, financial fraud, unauthorized access, malware deployment, business email compromise, insider misuse, and attacks on infrastructure or services.
Digital forensics is the discipline used to identify, preserve, analyze, and report digital evidence. In practice, investigation and forensics work together because one defines the incident and the other establishes the facts.
The distinction is straightforward:
Detection raises the alarm. Forensics turns that alarm into a case.
Most investigations fall into a few recurring categories.
These cases often begin with endpoint alerts, encryption activity, suspicious binaries, or network communication tied to known infrastructure. Investigators reconstruct how access was gained, how malware spread, and what was affected.
Credential theft, account takeover, and suspicious remote access typically rely on authentication logs, endpoint artifacts, mailbox activity, and network traces to determine scope and intent.
What looks like a single compromised mailbox is often part of a wider pattern involving impersonation, forwarding rules, and external infrastructure. These cases combine technical, financial, and behavioral analysis.
These investigations focus on file access, data movement, and outbound activity. Endpoint forensics, cloud logs, and network analysis are key to establishing what left the environment and how.
Insider cases often involve intellectual property theft, policy violations, or unauthorized transfers. These require coordination across forensics, legal, HR, and internal security.
Some cyber investigations overlap with fraud. Payment diversion, compromised accounts, and coordinated activity often require both forensic analysis and financial investigation.
Not all security teams investigate the same way. The difference is not just resources or tooling. It is what the team is actually trying to accomplish.
Alert response focuses on containment. A phishing email is blocked. A suspicious process is killed. A compromised account is disabled. The goal is speed and closure.
Investigation focuses on understanding. What happened before the alert fired? What happened after? Are there related events the detection missed? What does this incident reveal about gaps in visibility, controls, or assumptions?
The shift happens when teams stop treating alerts as isolated events and start treating them as potential indicators of broader activity. That requires different capabilities: evidence preservation before containment, correlation across systems and time periods, pattern recognition across incidents, and integration with threat intelligence.
It also requires a different question. Alert response asks: "Can we close this ticket?" Investigation asks: "What else don't we know?"
Digital forensics turns suspicion into evidence.
It allows investigators to preserve volatile data, reconstruct activity across systems, recover deleted artifacts, build timelines, and support decisions with defensible findings. Without it, investigations remain incomplete or open to challenge.
A strong investigation begins with detection, but detection alone is not enough. Alerts provide signals, not answers.
Common sources include endpoint alerts, authentication anomalies, email security events, network traffic irregularities, DNS and proxy logs, cloud audit trails, and user reports. These signals help contain activity quickly, but they rarely explain the full picture.
What matters is how those signals are developed into a case.
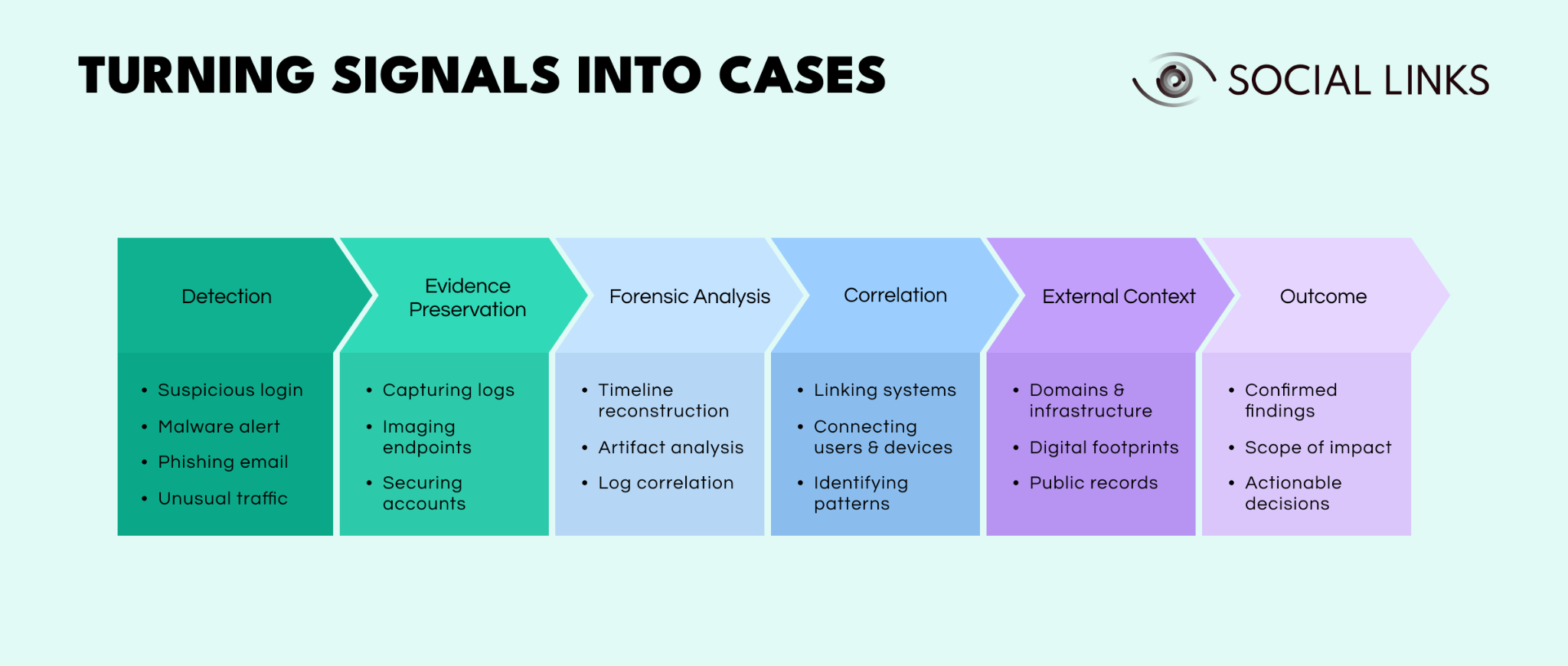
At a high level, investigations follow a consistent path.
They begin with detection, where a signal surfaces but its meaning is unclear. That signal only becomes useful if evidence is preserved early, before logs expire, systems change, or accounts are reset.
From there, forensic analysis reconstructs what happened. Investigators build timelines, examine artifacts, and correlate logs across systems to understand the sequence of events.
The case expands during correlation, when activity is linked across users, devices, and systems. What looked like an isolated alert often turns out to be part of a wider pattern.
Adding external context then connects internal findings to domains, infrastructure, entities, and digital footprints outside the organization. This is often where intent and relationships become clearer.
The outcome is not just alert resolution. It is confirmed findings, a defined scope of impact, and decisions the organization can act on.
A cyber crime scene is not a single device or alert. It is a distributed environment of evidence.
It may include endpoints, servers, email accounts, cloud platforms, network logs, authentication records, file systems, messaging tools, mobile devices, and external infrastructure. One of the most common mistakes is narrowing the scope too early.
A proper investigation expands until the activity can be explained coherently, then narrows based on evidence.
Digital evidence is only useful when it is preserved, interpreted, and connected.
Relevant sources include endpoint artifacts, memory data, logs, mailboxes, browser history, cloud activity, authentication records, and network traces. Individually, these may be ambiguous. Together, they form a narrative.
A deleted file alone may mean little. Combined with USB activity, cloud uploads, and external logins, it becomes evidence of deliberate action.
Effective investigations rely on combining methods.
Tools vary, but the goal is consistent: preserve evidence, correlate data, and explain findings clearly.
OSINT extends investigations beyond internal systems.
Internal evidence often points outward—to domains, infrastructure, or identities. OSINT helps connect these to broader patterns, including infrastructure clusters, aliases, prior activity, and public records.
This is especially useful in phishing, fraud, and attribution scenarios, where internal data alone cannot explain the full picture.
A strong investigation follows a structured sequence. The steps themselves are straightforward. The difficulty comes from executing them under time pressure, incomplete information, and changing risk.
Scoping the case. Investigators define what actually matters: which users, systems, accounts, and timeframes are in scope, and which decisions the investigation supports. Poor scoping leads to missed evidence or wasted effort.
Preserving evidence. Before systems are reimaged, accounts are reset, or logs expire, relevant evidence must be secured. This is often the point where weak investigations fail.
Collecting relevant data. Teams gather the data that supports the allegation, including logs, endpoints, cloud records, and network activity, without over-collecting or losing focus.
Analyzing artifacts. Investigators examine what happened at a technical level, including user activity, process execution, file movement, and communication patterns.
Correlating internal and external context. Artifacts only become meaningful when they are connected across systems, users, timelines, and external infrastructure. This is where investigators determine whether events are isolated or part of a broader pattern.
Reporting findings. Teams translate technical evidence into a clear narrative: what happened, what is confirmed, what remains uncertain, and what it means for the organization.
Supporting action. Findings inform containment, remediation, legal action, disclosure, or further investigation.
Each step builds on the previous one. When teams skip or rush a stage, the outcome weakens, even if the initial signal was correctly identified.
Cyber investigations are difficult for reasons that go beyond tooling or process. The problem is not just volume. It is the nature of the environment investigators work in.
Evidence disappears quickly. Logs rotate, memory clears, cloud sessions expire, and systems are rebuilt for operational reasons. Investigators often work against the clock, trying to preserve data before it is lost.
Evidence is fragmented across systems. Relevant data lives across endpoints, email systems, identity platforms, cloud services, and network tools. Each system stores different pieces of the same story, and investigators piece them together under pressure.
Signals overlap and are ambiguous. A suspicious login might be a user traveling, a misconfigured system, or an active compromise. A process execution might be legitimate software or malware. Investigators constantly interpret signals that do not carry meaning on their own.
Attribution requires caution. Organizations often push for fast answers, but attribution is one of the easiest places to get it wrong. Infrastructure is reused, shared, or deliberately manipulated. Investigators separate strong indicators from assumptions.
Scale increases noise. Modern environments generate large volumes of alerts and telemetry. Investigators do not lack data. They filter it, prioritize it, and decide what actually matters.
These challenges stack on top of each other. Investigators work with incomplete data, across fragmented systems, against time pressure, while adversaries actively try to avoid detection.
The challenge is not finding signals. It is making sense of them before they disappear.
Suspicious activity rarely stays within one system. Alerts often point to external domains, infrastructure, or identities.
This is where Social Links adds value. It helps investigators connect internal artifacts to external context—domains, entities, digital footprints, and relationships—so they can understand what those signals represent.
This is particularly useful in phishing, fraud, and infrastructure mapping cases, where internal evidence alone is not enough.
Cyber crime and digital forensics belong together because detection alone is not enough. A signal only becomes actionable when it is developed into a defensible case.
The strongest programs combine detection, forensics, intelligence, and OSINT. That is what separates resolving alerts from understanding what actually happened.
Cyber crime investigation examines suspicious or malicious activity by collecting and analyzing evidence from systems, accounts, and networks. The goal is to establish what happened and what can be proven.
Detection identifies potential incidents. Forensics preserves and analyzes the evidence needed to explain them and support action.
Investigators use endpoint, network, log, and malware analysis tools, along with intelligence platforms and investigation software.
OSINT provides external context, helping investigators connect internal evidence to domains, infrastructure, entities, and broader activity.
Evidence is volatile, data is fragmented, and many cases involve both technical and human factors. The challenge is building a clear, defensible narrative from incomplete signals.
Want to see how intelligence platforms support cyber investigations? Book a personalized demo with one of our specialists and discover how SL Crimewall helps investigators connect internal artifacts to outside entities, map infrastructure, and examine digital footprints through integrated OSINT workflows.