Cybersecurity Investigations: OSINT in Incident Response


Cybersecurity investigations begin when digital systems show signs that something is wrong. A login appears from an unusual location, network traffic behaves unexpectedly, or sensitive data moves outside normal workflows. These signals rarely explain themselves. Security teams must determine whether they represent harmless anomalies or indicators of compromise, and then reconstruct what actually happened inside the environment.
In this article, we examine how cybersecurity investigations operate within modern incident response workflows. We explore how security teams combine containment actions, digital forensics, and open-source intelligence to understand incidents, attribute attacker activity, and guide remediation decisions. We also examine three investigation approaches—containment-focused, forensic, and intelligence-driven—and how organizations move from initial detection to evidence-based understanding during active incident response.
A cybersecurity investigation is a structured inquiry conducted after suspicious activity or a confirmed incident. Its goal is not only to stop the attack but also to establish a clear understanding of what happened.
A well-executed investigation answers several key questions:
Security alerts highlight anomalies. Investigations explain them. The result should be a defensible understanding of the incident that supports recovery, compliance obligations, and improved defenses.
Not every incident requires the same investigative depth. Organizations typically conduct investigations using one of three approaches, depending on urgency and objectives.
Containment investigations focus on stopping active threats as quickly as possible. Speed matters more than completeness.
This approach is common when:
Analysts isolate affected systems, suspend compromised accounts, and block attacker infrastructure. Evidence collection is limited to what is needed to disrupt the attack.
The downside is incomplete visibility. Attackers often maintain backup access methods that survive initial response. Without deeper analysis, organizations risk repeated compromise.
Forensic investigations focus on reconstructing the incident with legally defensible evidence. The goal is not only containment but proof.
This approach is necessary when:
Investigators preserve evidence through forensic imaging before remediation begins. They analyze artifacts such as filesystem timestamps, memory captures, registry changes, and network logs to reconstruct the timeline of attacker activity.
This process produces detailed explanations of how the breach occurred and what data was accessed. However, it requires time and specialized expertise, which can delay immediate remediation.
Intelligence-driven investigations treat incidents as opportunities to understand adversary behavior.
Instead of focusing only on the individual incident, analysts examine how the activity fits into broader threat patterns. Internal findings are correlated with external threat intelligence to identify campaigns, infrastructure reuse, or known threat actors.
For example, a phishing investigation may reveal that the same malicious domain targeted multiple organizations in the same sector. This context can reveal that an apparently isolated incident is part of a larger campaign, which may shift defensive priorities.
This approach helps organizations strengthen detection capabilities and anticipate future attacks. However, it requires mature threat intelligence capabilities and experienced analysts.
Effective security teams rarely rely on a single investigation type. Instead, they move between approaches as the situation evolves.
A ransomware outbreak may begin with rapid containment to stop encryption. Once systems are stabilized, investigators conduct forensic analysis to determine how the attacker gained access. Intelligence analysis then examines whether the attack is part of a broader campaign.
The goal is not choosing one investigation model but applying the right level of analysis at the right time.
In most organizations, cybersecurity investigations take place inside the broader incident response process. Once suspicious activity is detected, response teams must both contain the threat and investigate its cause. While containment focuses on stopping damage quickly, investigation focuses on understanding how the compromise occurred and whether attacker access still exists. These two activities evolve together throughout the incident response lifecycle.
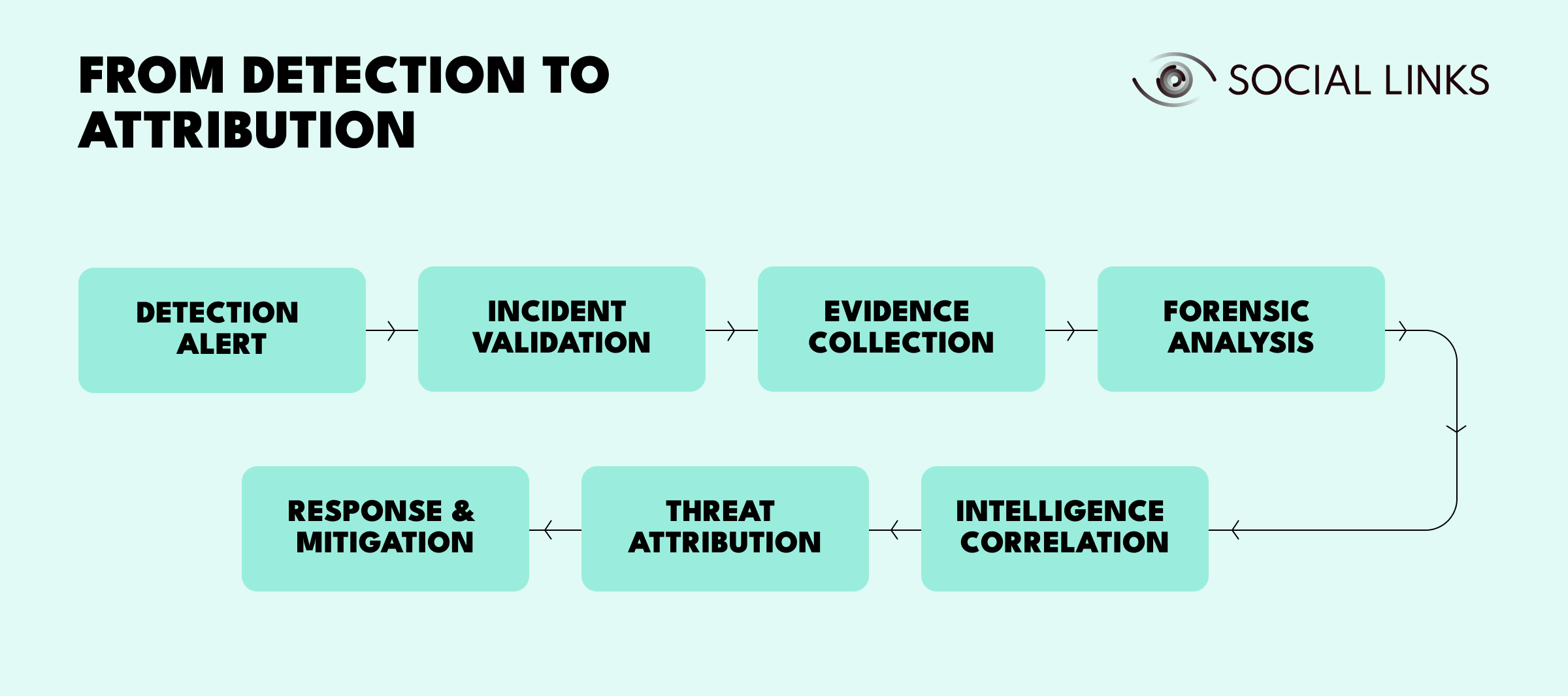
Investigations start when monitoring systems detect suspicious activity, such as unusual authentication behavior, abnormal network traffic, or malware execution on endpoints.
At this stage, the alert simply indicates that something may be wrong.
Analysts determine whether the alert represents a real security incident or a benign anomaly. They review telemetry, correlate logs, and compare indicators against known attack patterns.
This step filters false positives and confirms whether a full investigation is required.
Once an incident is confirmed, investigators collect relevant evidence before remediation alters system artifacts.
Evidence may include system logs, network traffic records, authentication events, and forensic images of affected devices.
Capturing this information early is critical for reconstructing attacker activity later.
Forensic analysis turns raw evidence into a timeline of events. Investigators analyze system artifacts, command histories, and network connections to determine how the attacker gained access and what actions were performed.
By correlating logs, system artifacts, and persistence mechanisms, analysts can reconstruct the sequence of attacker activity and determine the scope of the compromise.
Internal findings are enriched with external intelligence sources. Analysts compare indicators with known threat campaigns, investigate malicious infrastructure, and map techniques to frameworks such as MITRE ATT&CK.
This context helps determine whether the incident is isolated or part of a larger attack pattern.
Attribution attempts to identify the likely actor behind the attack. While definitive attribution is rare, investigators can often link activity to known threat groups based on infrastructure, tactics, and historical behavior.
Even partial attribution provides valuable insight into attacker motivations and likely next steps.
The final stage removes attacker access and prevents similar incidents from recurring.
Typical mitigation actions include:
Investigation findings should feed back into security controls to reduce future risk.
Digital forensics provides the technical foundation for understanding security incidents. Forensic analysis preserves and examines evidence without altering original data, working from verified copies rather than live systems.
Core forensic activities include:
This discipline transforms technical artifacts into legally defensible evidence that reconstructs attacker activity with precision. For instance, filesystem timestamps might show files accessed at 2:47 AM, while authentication logs reveal the account was compromised three days earlier. This timeline transforms fragmented evidence into a coherent narrative of the breach.
Digital forensics supports not only technical remediation but also regulatory breach notifications, insurance claims, and law enforcement cooperation when criminal activity is involved.
Technical evidence rarely tells the entire story. Attackers frequently reuse infrastructure, malware, and tactics across multiple targets. During incident response investigations, open-source intelligence helps analysts connect internal findings with external threat activity. Indicators discovered during forensic analysis—such as malicious IP addresses, domains, or malware samples—can be correlated with public intelligence sources to identify known threat actors or active campaigns.
Analysts may examine threat intelligence feeds, public malware databases, leaked credential sources, or open reporting on attacker infrastructure.
For example, identifying a malicious IP during an investigation may reveal that the same infrastructure has been used in attacks against other companies in the same industry. This context immediately changes investigative priorities and defensive strategy.
Without external intelligence, investigations remain limited to a single incident. With it, security teams gain insight into the broader threat landscape.
Cybersecurity investigations are now a central component of modern incident response. They are structured analytical processes that combine incident response, digital forensics, and intelligence analysis to understand adversary behavior and reduce future risk.
The most effective organizations treat investigations as learning opportunities. Each incident strengthens detection capabilities, improves response procedures, and expands understanding of emerging threats.
Security teams that investigate thoroughly move faster from detection to remediation and are far less likely to repeat the same compromises.
Cybersecurity investigations are structured inquiries analyzing suspicious activity or confirmed incidents to determine cause, scope, and impact. They are required after security breaches, malware infections, insider threats, or events triggering regulatory reporting obligations.
The three types are containment investigations (stopping active threats quickly), forensic investigations (establishing comprehensive evidence for legal or regulatory purposes), and intelligence-driven investigations (understanding adversary behavior to improve long-term defenses).
Open-source intelligence enriches internal findings by correlating indicators with known threat actors, infrastructure, or campaigns observed outside the organization. This external context improves attribution, prioritization, and response decisions.
Digital forensics preserves and analyzes technical evidence such as system artifacts, logs, and malware samples. It reconstructs detailed timelines and provides defensible proof of incident activity, supporting both technical remediation and regulatory or legal requirements.
Post-incident review identifies detection gaps, response procedure failures, and needed security control improvements. Without this phase, organizations repeat the same vulnerabilities and compromises. Investigation becomes organizational learning rather than isolated response.
Want to see how unified intelligence platforms support cybersecurity investigations and multi-source analysis? Book a personalized demo with one of our specialists and discover how SL Crimewall helps security teams correlate threat intelligence, accelerate forensic analysis, and support investigation workflows through structured analytical capabilities.