Due Diligence Tools: Verification and Investigation


Due diligence tools are often treated as simple lookup systems: search a name, check a database, move on. In practice, effective due diligence is much closer to investigation than verification. A strong research tool can confirm that a company exists, but it cannot explain whether that company is legitimate, connected to risk, or part of a larger pattern that should affect your decision. The difference between checking and understanding is what separates surface-level compliance from genuine risk assessment.
In this article, we examine what due diligence actually involves, why tools alone break down, which capabilities matter most, and how organizations move from basic verification to deeper investigation when risk, complexity, or inconsistency demand more.
Due diligence is the process organizations use to verify identities, assess risk, and investigate entities before making decisions that create exposure.
In practice, that means confirming identities during onboarding, screening individuals and companies against sanctions and watchlists, assessing financial and legal risk before partnerships or transactions, investigating ownership structures and beneficial owners, and validating that entities are what they claim to be rather than shells, fronts, or vehicles for hidden risk.
The goal is not just collecting information. It is determining whether that information supports trust, reveals risk, or requires deeper investigation before proceeding.
Organizations make decisions constantly: onboarding vendors, entering partnerships, executing transactions, acquiring companies. Each decision creates exposure. Without effective due diligence, that exposure often remains invisible until something goes wrong.
Strong research and verification systems help organizations validate identities and entities before engagement, detect inconsistencies and red flags early, assess risk while decisions can still be influenced, and support compliance with regulatory requirements that carry real penalties.
But the central challenge is not access to data. Most organizations already have databases, screening systems, and software platforms. The challenge is interpretation. A corporate registry confirms that a company is registered. It does not explain whether that company operates legitimately, who really controls it, or whether its relationships raise concerns. That requires investigation, not just lookup.
Modern due diligence rarely depends on a single platform. Most organizations use a mix of capabilities depending on the decision they are making and the level of risk involved.
The main categories usually include identity verification systems, sanctions and watchlist screening platforms, corporate registry and ownership databases, adverse media screening tools, financial and legal review systems, and broader investigation platforms that help analysts correlate findings across sources.
At a practical level, the most useful distinction is between tools that verify, tools that screen, and tools that investigate. Basic platforms may help confirm legal existence or ownership on paper. Deeper systems help analysts understand whether that structure is legitimate, misleading, or intentionally obscured.
Not all due diligence approaches are the same. The difference is not just thoroughness. It is what the organization is trying to accomplish.
Tools focus on verification. They check identities against databases, screen names against sanctions lists, pull corporate records from registries, validate addresses and documentation, and generate compliance reports. The goal is confirming basic facts quickly and at scale.
Investigation focuses on understanding. It asks different questions. Who really owns this entity? Are the stated business activities consistent with available evidence? Do relationships or patterns raise concerns that documents alone do not reveal? What does external intelligence show about legitimacy, risk, or intent?
Tools answer: "Does this match our criteria?" Investigation answers: "What does this actually represent, and should we trust it?"
Organizations that rely only on tools may satisfy minimum compliance requirements, but they are more likely to miss hidden ownership, undisclosed relationships, and inconsistencies that only become visible through correlation and analysis.
Basic due diligence handles straightforward cases. An individual has clean identity documents, passes sanctions screening, and shows no adverse media. A company has proper registration, transparent ownership, and legitimate business activity. Verification is sufficient.
Investigation becomes necessary when surface checks raise questions rather than answering them. Ownership structures become complex or deliberately opaque. Business activities do not match stated purposes or financial profiles. Entities operate across multiple jurisdictions in ways that suggest structuring rather than operations. Digital footprints contradict official records. Relationships connect to higher-risk entities or sanctioned individuals.
At that point, due diligence shifts from verification to analysis. Investigators examine corporate structures to identify beneficial owners hidden behind nominees, layers, or offshore vehicles. They cross-reference outside sources to validate business legitimacy beyond registry confirmation. They map relationships across entities, individuals, and infrastructure to identify connections that internal data misses. They analyze digital footprints to determine whether stated activities match observable reality.
This is where verification platforms provide raw material, but investigation provides understanding.
Effective due diligence relies on several capabilities working together. Identity verification confirms that individuals are who they claim to be. Background checks and adverse media surface past issues. Compliance screening identifies regulatory risk. Corporate registries provide formal ownership and structure, while financial and legal analysis help determine whether an entity operates as it claims.
Each capability answers a different question, but none of them explains risk on its own. That only emerges when findings are interpreted together.
Automated systems excel at certain tasks. They screen thousands of names against sanctions lists in seconds. They validate identity documents through image analysis and database checks. They pull corporate records from registries automatically. They generate compliance reports consistently.
But automation has hard limits in due diligence.
An automated system sees that a company is registered. It cannot determine whether that registration reflects operational reality or simply paperwork masking a shell. It confirms ownership based on filed documents, but it cannot reliably identify beneficial owners hidden behind nominees or offshore structures.
Automation works well on structured and documented information. It becomes far less reliable when risk is obscured, inconsistent, or deliberately concealed. The more sophisticated the case, the more human-led analysis matters.
Internal databases and commercial systems show what is documented and structured. OSINT reveals what is public but unstructured: the context that explains whether documented information should be trusted.
When due diligence encounters suspicious entities, corporate structures, or individuals, open source intelligence helps answer questions that databases cannot. Is this company operationally active or just registered? Do digital footprints match stated business activities, or is the online presence minimal, inconsistent, or fabricated? What relationships exist that official records do not show? Does adverse media reveal issues that screening databases missed?
OSINT enables investigators to validate business legitimacy through websites, public records, media reporting, and digital footprint analysis that show actual operations rather than just legal existence. It identifies hidden relationships by mapping connections across entities, individuals, domains, and infrastructure that internal tools cannot see. It detects inconsistencies when stated addresses lead to virtual offices, declared industries do not match public presence, or ownership claims contradict available evidence.
This is where investigation platforms become genuinely useful. They do not just retrieve records. They help analysts correlate what is visible across multiple sources into a workable risk picture.
Corporate due diligence involves more complexity than individual verification because companies are legal constructs that can be layered, restructured, and obscured across jurisdictions.
Effective corporate analysis supports examination of ownership structures, subsidiary and affiliate relationships, financial statements, regulatory actions, litigation history, and beneficial ownership. These capabilities are especially important when decisions involve investment, acquisition, partnership, vendor onboarding, or long-term exposure.
The central challenge is beneficial ownership. Many structures are deliberately designed to obscure ultimate control. Nominees appear as directors. Shell companies hold stakes. Offshore entities add opacity. Trusts and foundations create further layers. Following these structures requires investigation that goes beyond what corporate registries provide.
A database may show that Entity A owns Entity B. It does not show that Entity B is controlled through a trust in another jurisdiction and ultimately linked to a sanctioned or high-risk individual. Uncovering that chain requires cross-referencing jurisdictions, identifying patterns, and validating what official records claim against what relationships actually exist.
Some risks only become visible when due diligence moves beyond identity and ownership checks.
Financial analysis helps organizations examine financial reporting, transaction patterns, accounting inconsistencies, and indicators of economic substance. These capabilities are especially important when evaluating investment targets, strategic partners, or high-value vendors.
Legal review focuses on litigation history, regulatory actions, compliance failures, contractual obligations, and disputes that may affect exposure. These systems support the broader legal process, where risk may be less visible but far more consequential.
This is where software becomes most valuable when it can pull together financial, legal, and corporate data into a single investigative workflow rather than forcing analysts to switch constantly between disconnected systems.
Modern software is not defined by data access alone. It is defined by how well it structures and connects that data.
The strongest systems typically include data aggregation across multiple sources, entity resolution to unify fragmented identities, link analysis to map relationships, workflow management to document findings and escalation, and risk scoring to help analysts prioritize what deserves deeper review.
The point is not automation for its own sake. It is reducing manual friction while preserving the analytical judgment needed for complex cases.
In practice, due diligence moves along a spectrum rather than following a rigid checklist. Most cases begin with basic verification, progress through enhanced screening and structured analysis, and only escalate into deep investigation when risk, inconsistency, or complexity demands it.
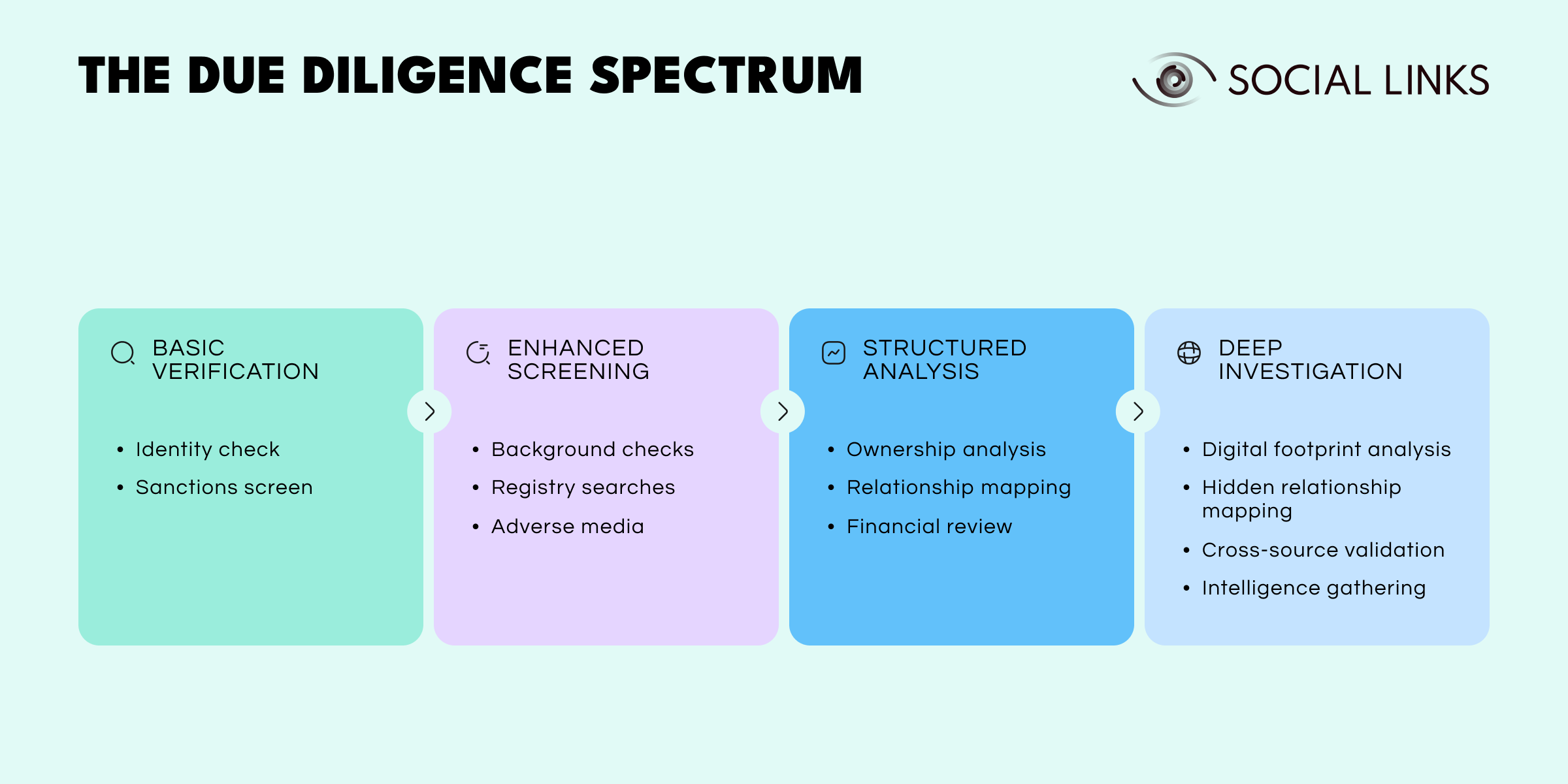
Basic verification handles straightforward, low-risk cases. Identity checks confirm individuals are who they claim to be. Sanctions screening flags immediate regulatory concerns. For many routine decisions, this baseline level is sufficient.
Enhanced screening applies when initial checks flag potential concerns or when the relationship carries moderate risk. Background checks surface historical issues. Registry searches pull corporate structures and ownership. Adverse media screening identifies public-facing problems that databases might miss. This level catches most risks without requiring full investigation.
Structured analysis becomes necessary when complexity or inconsistency appears. Ownership analysis traces beneficial owners through layered structures. Relationship mapping identifies connections that raise questions. Financial review validates that reported activity matches stated business. This level requires more time and expertise, but it reveals risks that screening alone cannot detect.
Deep investigation applies to high-risk cases where standard methods are insufficient. Digital footprint analysis validates that entities operate as claimed. Hidden relationship mapping uncovers connections designed to stay invisible. Cross-source validation reconciles conflicting information. Intelligence gathering through OSINT adds context that internal systems cannot provide. This is the most resource-intensive level, reserved for cases where exposure justifies the investment.
Each level builds on the previous one. Organizations escalate through the spectrum based on what earlier stages reveal. Weak verification misses red flags that screening would catch. Superficial screening hides patterns that structured analysis would identify. Limited analysis overlooks risks that deep investigation would expose.
Even well-resourced organizations face recurring obstacles, such as:
Data fragmentation. Relevant information is scattered across corporate registries, sanctions databases, financial platforms, legal records, and external sources that do not integrate well.
False positives. Automated screening generates noise that requires manual review, with common names, location flags, and incomplete records creating alerts that are not truly relevant.
Complex ownership structures. Beneficial ownership is deliberately obscured through nominees, layered entities, and multiple jurisdictions.
Time pressure. Decisions are made before analysis is complete, especially in competitive transactions or urgent onboarding scenarios.
Limited external visibility. Organizations depend on what entities disclose and what databases happen to capture, leaving gaps in understanding.
These challenges explain why due diligence cannot be just a checklist. It requires combining automated systems for efficiency with investigation for depth, and scalable platforms with human judgment for interpretation.
Due diligence is moving toward more integrated, intelligence-driven workflows.
That includes stronger entity resolution, better use of open source intelligence, more automation in lower-risk checks, and improved correlation across corporate, legal, financial, and digital sources. Real-time monitoring of entities, ownership changes, and public reporting is also becoming more common.
The challenge will be keeping speed and scale without losing the analytical judgment that complex cases still require. The most effective systems will not simply retrieve more data. They will help analysts understand what that data actually means.
Due diligence is not a checklist. It becomes an investigation as soon as the available facts stop being self-explanatory.
Tools provide data. Investigation provides understanding. Organizations that rely only on verification may meet baseline requirements, but they often miss the risks that matter most: hidden ownership, undisclosed relationships, and entities designed to appear legitimate while concealing exposure.
The strongest programs know when verification is enough and when deeper analysis is required. They combine automated checks with investigative capacity, internal data with external intelligence, and speed with proportional rigor.
That is what turns due diligence from a compliance task into real risk management.
Due diligence verifies identities, assesses risk, and investigates entities before making decisions that create exposure. It combines identity verification, compliance screening, background checks, and investigation to determine whether individuals or companies should be trusted.
Tools help collect and analyze information from multiple sources, enabling analysts to validate identities, screen against sanctions lists, check corporate registries, and identify red flags that may not be visible in one database alone.
Corporate due diligence focuses on company structures, ownership chains, legal history, financial exposure, and beneficial ownership analysis. It is used in vendor reviews, mergers and acquisitions, partnerships, and other high-risk decisions involving companies rather than individuals.
Effective software supports investigations by aggregating data across sources, resolving entities across fragmented records, mapping relationships, and documenting findings in consistent workflows. The best systems reduce manual work without replacing analytical judgment.
OSINT adds external context through public records, digital footprints, media reporting, and relationship mapping. It helps investigators detect inconsistencies, hidden connections, and risks that structured databases may miss.
Want to see how external intelligence supports due diligence investigations? Book a personalized demo and discover how SL Crimewall helps due diligence teams validate entities, map hidden ownership, analyze digital footprints, and understand risk through integrated OSINT workflows.