Employee Background Verification: Beyond Checkbox Compliance
Employee background verification is a standard part of modern hiring. Nearly every organization conducts some form of background check before making employment decisions. Yet in many cases, the process is treated as a procedural safeguard rather than a strategic tool. Screening depth is applied uniformly, findings are reduced to simple “pass” or “fail” outcomes, and the broader hiring risk picture remains underexplored.
In this article, we examine what employee background verification should accomplish beyond basic compliance and how organizations can design programs that align screening depth with role risk, interpret findings in context, and use results to strengthen hiring decisions over time while remaining legally compliant.
Employee background verification is the structured process of validating a candidate’s identity, credentials, work history, and relevant risk indicators before finalizing employment decisions.
Typically, this includes:
The purpose is not to produce a simple approval or rejection. It is to provide meaningful context. A 15-year-old misdemeanor does not carry the same weight as falsified credentials. A brief employment gap differs from a fabricated job title.
Verification informs professional judgment; it does not replace it.
Organizations generally operate in one of two modes.
This model applies standardized screening across all roles, regardless of exposure or responsibility. The focus is procedural: complete the checks, document consent, avoid liability.
It does serve a purpose. It detects major fraud and supports regulatory compliance. However, it treats background verification as administrative overhead rather than a decision-making tool. As a result, resources are distributed evenly across low-risk and high-risk roles, and findings are interpreted mechanically.
More mature programs calibrate screening depth to role risk.
Positions with financial authority, executive responsibility, regulatory oversight, or access to sensitive systems receive proportionately deeper review. Lower-risk roles are screened appropriately, but not excessively.
Findings are evaluated against clear criteria:
Effective programs also track outcomes. If certain discrepancies correlate with performance issues or compliance problems, protocols are adjusted. Over time, verification becomes more precise and more relevant to actual hiring risk.
A well-designed employee background verification process looks at multiple signals together rather than relying on a single check. Each component helps employers confirm not only whether information is accurate, but whether it makes sense in the context of the role.
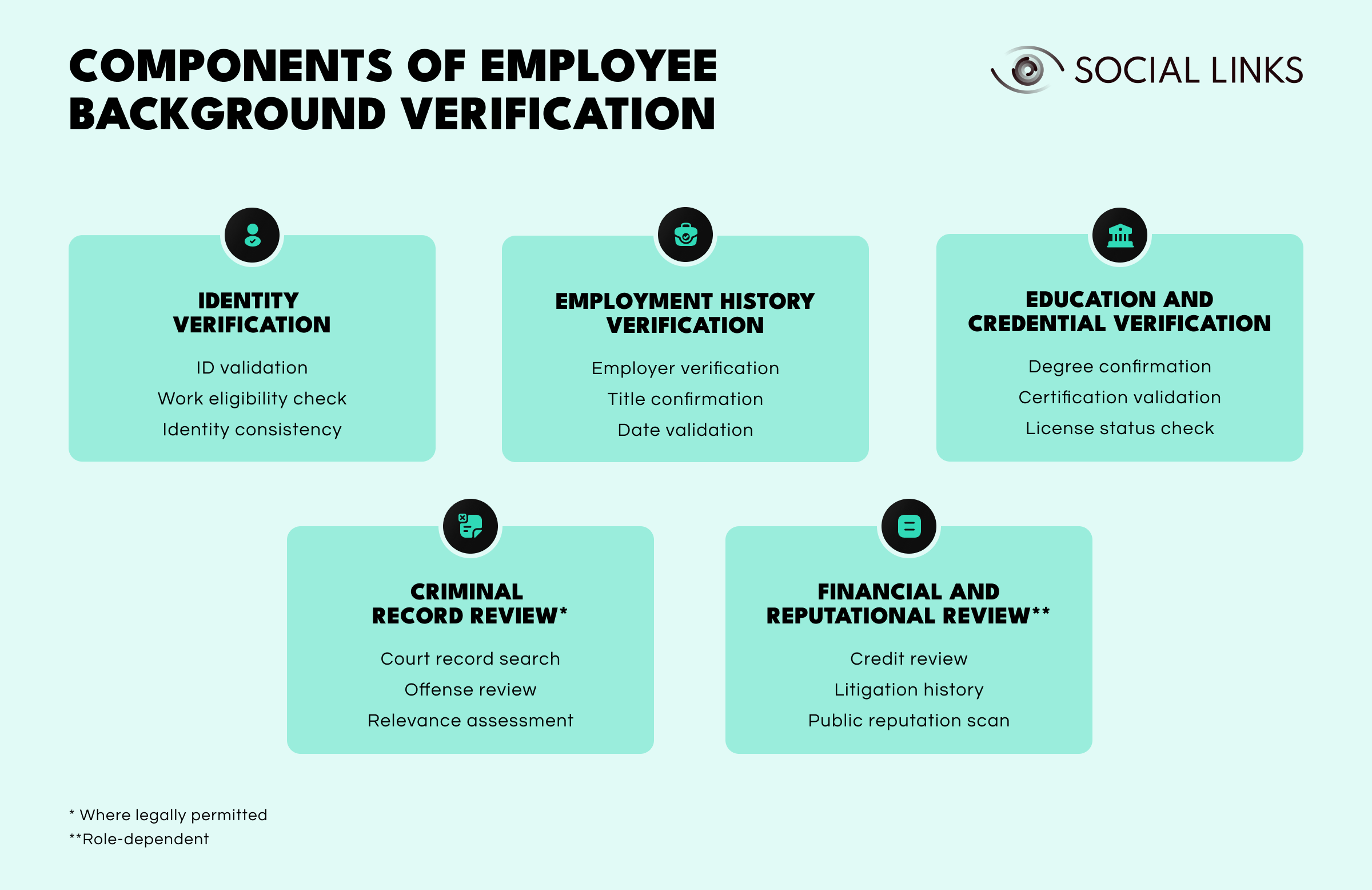
The process begins by confirming that the candidate is who they claim to be and legally eligible to work. Establishing identity consistency ensures that every other verification step is built on reliable information.
Previous employers, roles, and employment dates are reviewed to confirm that professional experience aligns with what was presented during hiring. Most discrepancies are minor, but recurring inconsistencies can signal areas that deserve closer attention or clarification.
Degrees, certifications, and professional licenses are validated to ensure qualifications are legitimate and current. This becomes especially important in technical, regulated, or client-facing roles where credentials directly influence responsibility and trust.
Where permitted by law, criminal background checks provide additional context related to workplace safety or fiduciary exposure. Effective programs focus on relevance and timing rather than treating findings as automatic disqualifiers.
For roles involving financial authority, leadership responsibility, or public visibility, organizations may also review financial history or publicly available reputation signals to identify risks that could affect organizational integrity.
Taken together, these components turn background verification into a clearer picture of candidate reliability. Instead of functioning as a checklist, verification becomes a structured way to support informed hiring decisions.
A strong background screening process balances thoroughness with legal safeguards and procedural clarity.
In the United States, employers must:
Consent must be explicit and separate from general employment documentation.
Verification may be conducted internally or through Consumer Reporting Agencies (CRAs). Most mid-sized and large organizations rely on third-party providers to ensure FCRA compliance and multi-jurisdictional coverage.
Timing is critical. Screening too early wastes resources; screening too late complicates hiring decisions. Most organizations conduct checks after narrowing candidates but before issuing formal offers.
If findings may negatively affect employment decisions, FCRA requires:
Procedural errors, even when findings are accurate, create legal exposure.
Background reports contain sensitive personal information. Responsible handling includes restricted access, secure storage, defined retention schedules, and documented destruction protocols. Poor data hygiene can create both compliance and reputational risk.
Employee background verification extends beyond initial hiring decisions.
Senior hires often warrant deeper review, including litigation history, regulatory actions, prior board affiliations, and public statements. At leadership levels, individual risk becomes organizational risk.
Organizations increasingly conduct business background checks on contractors, joint venture partners, third-party vendors, and acquisition targets. Third-party risk is a significant exposure vector, and verification reduces inherited liability.
In regulated industries such as financial services, healthcare, and government contracting, periodic re-verification is standard practice. Risk profiles evolve over time, and screening frameworks should reflect that reality.
When choosing a background screening provider, it is important to prioritize:
Informal data aggregators and consumer-focused search tools are not appropriate for employment screening. Many lack compliance safeguards and may contain inaccurate or outdated information.
Applying different standards to similar roles increases discrimination risk. Screening protocols should be tied to job requirements rather than individual manager preference.
Criminal history alone is rarely predictive. Relevance and proportionality must guide interpretation.
Findings should initiate clarification, not immediate disqualification. Many discrepancies have reasonable explanations.
Most FCRA violations stem from procedural missteps. Documented workflows and staff training significantly reduce exposure.
Unsecured storage or indefinite retention of reports creates avoidable compliance and security risks.
Employee background verification can function as basic compliance — or as structured risk management embedded in hiring strategy.
Compliance-driven programs focus on documentation and liability reduction. Risk-aligned programs match screening depth to role exposure, interpret findings thoughtfully, and refine processes over time based on outcomes.
When background verification informs decisions rather than merely documenting them, it becomes part of intelligent hiring rather than administrative procedure.
Employee background verification validates identity, work history, credentials, and relevant risk indicators before hiring. It supports informed employment decisions, reduces negligent hiring liability, and protects organizational reputation.
A background check for employment may include identity confirmation, employment history, education verification, criminal records (where permitted), credit history for financial roles, and professional licenses. The scope depends on the type of role and applicable regulations.
Responsible background screening requires written consent, compliance with FCRA and local laws, consistent application across comparable roles, and secure handling of sensitive data. Individualized assessment is essential when reviewing findings.
Background verification typically refers to confirming specific claims such as employment or education. Background screening often includes broader checks such as criminal records or credit history. In practice, most employers combine both within a structured employee background verification program.
Good background check sites for employment must comply with federal, state, and local regulations, provide accurate reports, support adverse action workflows, and maintain strong data security standards. Consumer search tools are not appropriate for employment screening.
Want to see how unified intelligence platforms support comprehensive background verification and risk assessment? Book a personalized demo with one of our specialists and discover how SL Crimewall helps organizations conduct multi-source verification, identify risk patterns, and support compliant hiring decisions through structured analytical workflows.