Financial Fraud Detection: When Alerts Aren't Enough


Financial fraud detection is no longer just about flagging suspicious transactions. The challenge now is not spotting anomalies. It is understanding which anomalies matter, why they happened, and whether they point to something bigger. Organizations are facing increasingly sophisticated schemes that combine technical manipulation, social engineering, and coordinated financial activity across multiple systems. Detection has to move faster, but it also has to get smarter.
In this article, we look at what financial fraud detection actually involves, why detection alone breaks down, which methods matter most, how real-time systems work, and where OSINT adds the context that internal monitoring often cannot provide.
Financial fraud detection is the process of identifying suspicious or fraudulent activity within financial systems before losses scale.
In practice, that means detecting unauthorized transactions, account takeovers, payment fraud, insider manipulation, and financial statement fraud across multiple channels at once. Detection may rely on transaction monitoring, behavioral analytics, risk scoring, pattern recognition, or investigation workflows, depending on the fraud type and the organization’s capabilities.
The goal is not just flagging anomalies. It is determining whether those anomalies represent real risk, understanding the pattern behind them, and responding before damage spreads.
The scale and speed of modern financial systems make fraud detection a core operational function, not just a compliance exercise.
Without effective detection, fraud can spread rapidly across accounts and systems before anyone recognizes the pattern. Losses compound, regulatory exposure increases, customer trust erodes, and remediation becomes more expensive. The central challenge is timing. Detection must operate fast enough to prevent damage, but accurately enough to avoid unnecessary disruption.
False positives waste time and frustrate customers. Missed fraud costs money and reputation. That balance is what defines effective fraud detection.
Fraud takes multiple forms, often overlapping across systems and channels.
Payment fraud involves unauthorized or manipulated transactions, including card fraud, wire transfer fraud, and invoice manipulation.
Account takeover occurs when attackers gain control of accounts using stolen credentials, social engineering, or identity theft.
Identity fraud covers cases in which fraudsters create or use false identities to access financial services or open accounts.
Insider fraud involves employees or trusted parties manipulating systems for financial gain, often exploiting access and knowledge that outside attackers do not have.
Financial statement fraud manipulates records to misrepresent performance, conceal losses, or mislead investors and regulators.
Each type requires different detection methods and different investigative depth.
Modern fraud detection systems are excellent at finding anomalies. They flag unusual transaction amounts, unexpected geographic activity, rapid behavioral changes, repeated failed attempts followed by success, and deviations from historical patterns. The problem is not detection volume. It is signal interpretation.
An automated system sees a transaction from a new location and flags it. A human investigator asks different questions. Is this fraud, or did the customer travel? Is this the first anomaly, or part of a pattern that has been developing for weeks? Does the account show other indicators of compromise, or is this isolated?
This is where many fraud programs struggle. Detection systems generate thousands of alerts every day. Fraud teams have to decide which ones represent real threats, which ones are false positives, and which ones require deeper investigation. The more sophisticated the fraud, the less obvious the answer.
That is why effective fraud detection is not just about better models. It is about pairing automated detection with investigative capacity, external context, and the ability to connect signals across systems and time.
Not all fraud programs approach this the same way. The difference is not just resources. It is what the team is trying to accomplish.
Detection focuses on speed and coverage. Systems monitor transactions continuously, apply risk scoring in real time, trigger automated actions when thresholds are crossed, and alert analysts when manual review is needed. The goal is to prevent loss before it happens.
Investigation focuses on understanding. What happened before the alert fired? Are there related accounts, transactions, or entities involved? Does this fit a known fraud pattern, or is it something new? What does external evidence reveal about the people or companies involved?
Detection answers: “Is this suspicious?” Investigation answers: “What actually happened, and what does it mean?”
The strongest programs do both. They detect quickly, but they also investigate deeply when the fraud is complex, coordinated, or part of a larger scheme.
Fraud detection works best when multiple methods are used together.
Each method has limits. Rules miss novel fraud. Anomaly detection creates noise. Behavioral models need time to learn. Risk scores depend on data quality. The value comes from combining them and adding human judgment where automation falls short.
Transaction monitoring is the most visible layer of fraud prevention. It analyzes transactions continuously as they move through payment systems, looking for indicators of fraud in the moment.
Real-time detection operates in seconds or milliseconds. A transaction is initiated, risk scoring is applied instantly, automated decisions are made, and alerts are generated for high-risk cases. Speed is critical, especially in payment systems where transactions settle quickly.
But speed creates trade-offs. Real-time systems have limited context at the moment of detection. They cannot wait for investigation or external validation. They must decide based on the signals available right then.
That raises false positive rates and increases reliance on automation. Block too aggressively, and legitimate customers are disrupted. Block too conservatively, and fraud gets through. The best systems layer real-time detection with post-transaction analysis and investigative workflows that catch what automation misses.
Financial statement fraud differs from transactional fraud. It is not one suspicious event. It is deliberate manipulation hidden inside legitimate processes over time.
Detection relies less on real-time monitoring and more on analytical investigation. That may include anomaly detection across reporting periods, pattern analysis against historical results, cross-checking outside data sources, and deeper review of inconsistencies, timing patterns, and suspicious adjustments.
This is where fraud detection moves beyond automation and into human-led analysis. Investigators look for financial results that do not match operational reality, revenue recognition patterns that appear engineered, expense timing that suggests manipulation, and relationships between entities that raise questions about independence.
Internal systems may show the numbers. External intelligence often reveals the context that explains why those numbers do not make sense.
Fraud detection does not fail because of a lack of data. It fails because data is disconnected, outdated, or interpreted without enough context.
Organizations are working with transaction histories, behavioral patterns, device and session information, historical fraud cases, and outside intelligence. When those sources are aligned, they support stronger risk scoring, better anomaly detection, earlier recognition of emerging fraud patterns, and clearer links across accounts and entities that might otherwise appear unrelated.
But volume alone does not help. Fragmented systems reduce visibility. Weak models miss new schemes. And even the best internal data cannot explain intent, relationships, or outside behavior without investigation.
Data makes fraud visible. Context makes it understandable.
Internal fraud detection systems show what is happening inside the organization’s perimeter. OSINT helps explain what is happening outside it.
When an account, transaction, or entity looks suspicious, internal monitoring may show the anomaly but not explain it. OSINT helps investigators understand who is behind the activity, whether entities are legitimate or shell companies, what digital footprints reveal about identity and behavior, how infrastructure and accounts connect across cases, and whether public records, adverse media, or breach data add relevant context.
This matters most in complex fraud schemes that extend beyond internal systems. A suspicious vendor may appear legitimate in internal records but have concerning ownership links, adverse media exposure, or digital footprints that suggest fraud risk. A compromised account may connect to infrastructure used in earlier fraud campaigns. A financial relationship may involve entities with undisclosed affiliations.
OSINT turns isolated signals into connected intelligence. It does not replace transaction monitoring. It extends detection into investigation by adding the context that explains what internal alerts actually mean.
Effective fraud detection follows a structured workflow. Each stage answers a different question, and skipping one weakens the whole chain.
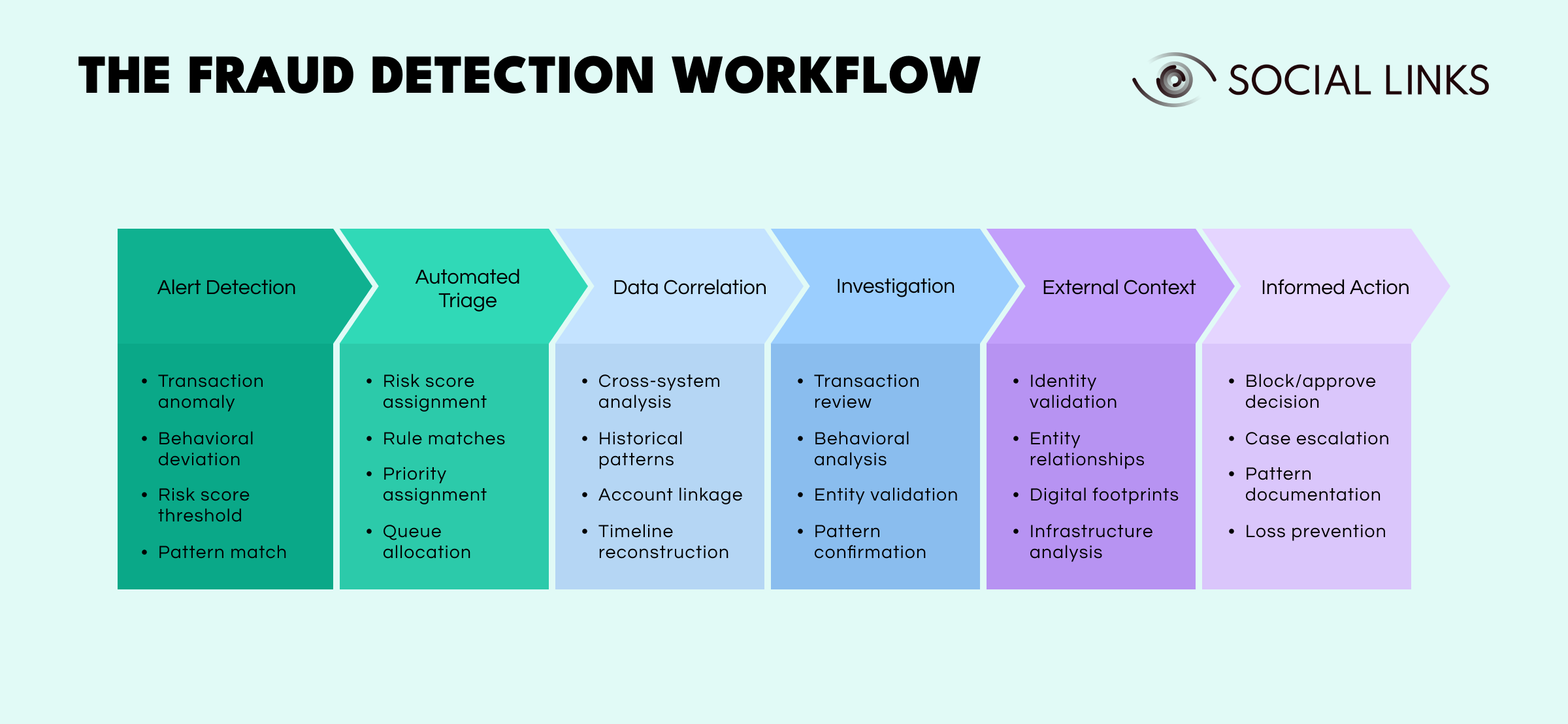
Alert detection comes first. Systems flag suspicious activity based on transaction anomalies, behavioral deviation, risk score thresholds, or known fraud patterns.
Automated triage follows. Risk scores are assigned, rule matches are evaluated, and alerts are prioritized and routed. At this stage, systems determine what deserves immediate attention and what can wait.
Data correlation builds the initial context. Activity is analyzed across systems, historical patterns are reviewed, linked accounts are identified, and timelines begin to take shape. This is where isolated alerts start to form a pattern.
Investigation deepens the analysis. Analysts review transactions, examine behavior, validate entities, and confirm whether the pattern represents fraud or a false positive.
External context adds what internal systems cannot provide. Identity validation, entity relationships, digital footprints, and infrastructure analysis help explain who is behind the activity and whether it connects to broader fraud patterns.
Informed action follows. Teams make decisions based on combined internal and external context, including blocking or approving transactions, escalating cases, documenting patterns, and preventing further loss.
Weak detection generates noise. Poor triage wastes time. Missing correlation hides patterns. Shallow investigation misses intent. Lack of external context creates blind spots. And delayed decisions allow fraud to scale.
Even advanced systems face the same recurring challenges.
False positives overwhelm teams. Too many alerts reduce efficiency, slow response times, and increase the chance that real fraud gets buried in the noise.
Data fragmentation weakens visibility. Relevant information sits across payment systems, account platforms, compliance databases, and outside sources that do not integrate well.
Fraud tactics keep evolving. Detection models built for yesterday’s schemes often struggle with today’s.
Scale and complexity keep growing. Transaction volumes rise while fraud becomes more coordinated and more adaptive.
Limited external visibility creates blind spots. Internal systems alone cannot explain fraud that extends across entities, infrastructure, and public-facing activity.
These challenges explain why fraud detection cannot rely on automation alone. Tools identify signals. Investigators interpret them. External intelligence adds the missing context.
Improving fraud detection requires more than adding tools.
Effective programs combine detection methods instead of relying on one approach, integrate transaction monitoring with investigation workflows so alerts lead to understanding, use risk-based approaches rather than static thresholds that generate excessive false positives, incorporate OSINT and external intelligence to validate internal signals, continuously update models as fraud tactics evolve, and ensure collaboration between fraud, compliance, and investigation teams.
Consistency and adaptability matter more than complexity. The strongest fraud detection programs are not the most automated. They are the ones that balance speed with accuracy, detection with investigation, and internal monitoring with outside context.
Modern fraud detection often requires moving beyond internal transaction data to understand entities, relationships, and broader patterns.
Social Links helps fraud teams analyze digital footprints, identify relationships between accounts, entities, and infrastructure, map fraud networks across cases, and conduct OSINT investigations at scale when fraud extends beyond internal visibility. It adds external context to internal alerts before action is taken.
This is especially useful in complex fraud cases involving multiple entities, coordinated activity, or schemes where internal data alone does not explain the full picture. Social Links extends detection into investigation by helping teams understand what suspicious signals actually represent.
Financial fraud detection is not just about identifying suspicious transactions. It is about understanding patterns, connecting signals across systems and entities, and responding with enough context to separate real fraud from noise.
Organizations that combine real-time detection with investigative capacity and external intelligence are better positioned to identify complex fraud schemes, reduce false positives, and act before losses scale.
Detection starts the process. Investigation and intelligence complete it.
Financial fraud detection identifies suspicious activity within financial systems using transaction monitoring, analytics, and investigation techniques. The goal is to determine which alerts represent real fraud and respond before losses occur.
Real-time fraud detection analyzes transactions as they occur, applies risk scoring instantly, and triggers automated responses or alerts for investigation. It prioritizes speed but requires careful tuning to balance fraud prevention with customer experience.
Transaction monitoring continuously analyzes financial transactions for suspicious patterns, unusual behavior, or deviations from normal activity. It combines rules, anomalies, and risk scoring to flag potential fraud.
Common tools include transaction monitoring platforms, behavioral analytics systems, machine learning models for anomaly detection, case management software, and investigation tools that integrate internal and external data.
OSINT provides external context that helps investigators validate identities, identify entity relationships, map fraud infrastructure, and connect internal alerts to broader patterns that internal systems cannot see.
Want to see how external intelligence supports fraud detection? Book a personalized demo and discover how SL Crimewall helps fraud teams connect suspicious signals to outside entities, validate identities, map fraud networks, and add investigative context through integrated OSINT workflows.