Fraud Prevention: Detecting Organized Schemes


Financial institutions face a constant dilemma. They can deploy generic rules that flag obvious suspicious activity and hope they catch most fraud, or they can invest in deeper analysis that understands behavior, identifies patterns, and connects seemingly unrelated events. That choice shapes not just how much fraud gets through, but how quickly an organization can adapt when attackers change tactics.
In this article, we examine how fraud prevention in financial services evolves from basic transaction rules to intelligence-led detection, why some institutions catch far more sophisticated threats than others, and how detection depth affects what can ultimately be stopped. We also look at common fraud types, the technologies used, and how open-source intelligence strengthens internal cases.
Fraud prevention in financial services refers to the systems, controls, and investigative methods used to identify, block, and respond to fraudulent activity targeting institutions and their customers. That includes stopping unauthorized transactions, detecting identity abuse, recognizing account compromise, and identifying coordinated fraud patterns.
At a practical level, effective programs pursue three connected goals:
This is why fraud prevention cannot be reduced to a single rule engine or alert queue. Strong programs combine transaction monitoring, behavioral analysis, identity verification, risk scoring, and investigative review.
Financial institutions face threats across multiple channels, and the mix changes by product type and customer base.
Payment schemes remain a major focus for banks, card issuers, processors, and fintechs. Fraudsters target wire transfers, card-not-present transactions, instant payments, ACH flows, and merchant channels. The goal is usually speed: once money moves, recovery becomes much harder.
Identity threats appear during onboarding and account access. Attackers may use stolen credentials, synthetic identities, forged documents, or account recovery abuse to gain access to services or open new accounts.
Account compromise has become more sophisticated because attackers increasingly rely on breached credentials, phishing, malware, and social engineering rather than brute-force tactics. Even when the login looks technically valid, the surrounding behavior may tell a different story.
Fintech platforms and digital banks often face high exposure here. Fraudsters create accounts to cash out quickly, exploit promotions, test stolen cards, or embed mule activity into what looks like normal onboarding.
Not every case involves a lone actor. Some schemes involve coordinated rings using multiple accounts, payment hops, devices, or identities. These are harder to detect because no single event looks extreme on its own.
The impact goes beyond direct financial loss. Weak controls erode customer trust, increase operational costs, create compliance exposure, and expose gaps in onboarding, authentication, and payment systems.
For institutions operating at scale, anti-fraud programs affect:
The tradeoff is constant. Controls that are too weak let fraud through. Controls that are too aggressive block legitimate behavior and create friction. That is why modern fraud prevention has to balance security, speed, and customer experience.
Fraud work also overlaps with anti-money laundering and broader financial crime detection. A suspicious transaction may be the first sign of laundering, mule activity, insider collusion, or organized abuse of payment infrastructure.
Not all anti-fraud programs operate at the same level of sophistication. Some rely heavily on simple transaction rules. Others analyze behavior and patterns. The strongest programs connect activity across accounts, devices, and external context to identify organized schemes rather than isolated incidents.
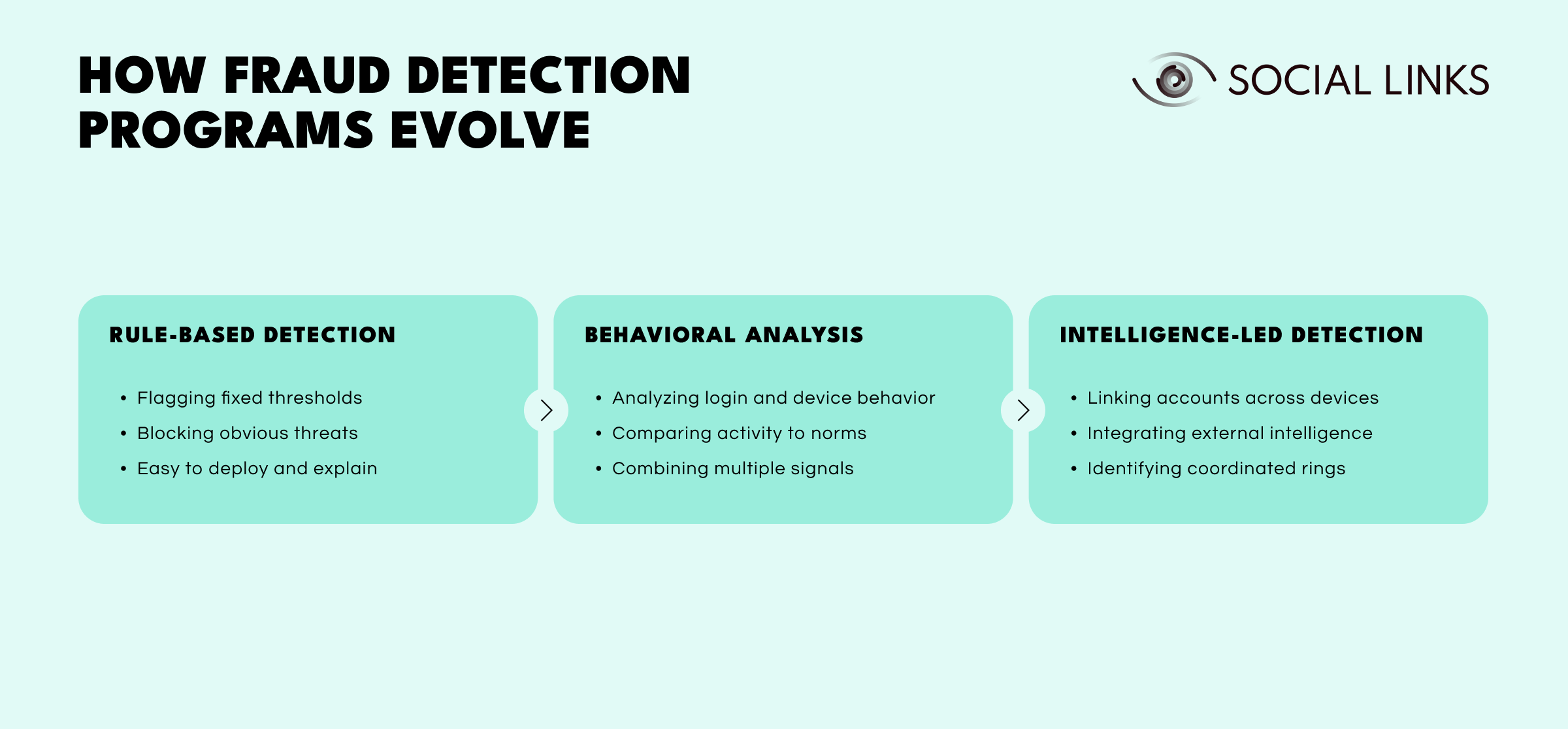
At the most basic level, institutions use predefined rules to flag known fraud patterns.
This level usually focuses on:
In practice, that may include large transfers after profile changes, repeated onboarding attempts using shared details, or transactions from high-risk geographies. This approach works well for obvious threats, but it is also easy for fraudsters to test and work around. Attackers probe thresholds, rotate tactics, and exploit gaps between controls.
The limitation is straightforward: rule-based systems catch what they are programmed to catch. They struggle with novel patterns, adaptive behavior, and schemes designed to stay just under detection thresholds.
As programs mature, institutions add behavioral analysis that compares activity to expected patterns rather than simply checking fixed thresholds.
This level often includes:
That may involve login timing, transaction cadence, destination patterns, typing behavior, account navigation, and risk scoring. This approach reveals what credentials alone cannot. A legitimate login does not always mean a legitimate user.
Its limitation is scope. Behavioral analysis still tends to examine individual accounts or sessions more than wider coordinated activity. It may miss schemes involving multiple accounts, shared infrastructure, or actors deliberately trying to look unrelated.
At the most advanced level, institutions treat suspicious activity as part of a broader system rather than a string of isolated events.
This level often includes:
Instead of reviewing each alert on its own, analysts examine relationships across accounts, devices, identities, and payment flows. Shared devices, repeated intermediaries, common payment destinations, coordinated timing, and external affiliations often reveal organized activity that transaction-level monitoring alone would never surface.
Developing this capability requires investment in data infrastructure, analytical tools, and skilled investigators. But it is also where institutions stop reacting to individual fraud attempts and start identifying the systems behind them.
In practice, the difference shows up quickly. A rule-based system may block a suspicious transfer and stop the immediate loss. A more mature program can go further, linking that transfer to shared devices, coordinated onboarding patterns, common payment destinations, and external fraud signals. What starts as one flagged transaction can turn out to be part of a coordinated ring involving many accounts. That is the value of deeper detection: it helps institutions see the structure behind the alert, not just the alert itself.
Data is the foundation of anti-fraud work, but more data does not automatically mean better decisions. What matters is how well the institution connects signals across identity, behavior, transactions, devices, and external context.
Useful data sources often include:
The challenge is correlation. A single suspicious transfer may not justify action. But that same transfer paired with a new device, recent password reset, unusual login path, and links to previously flagged entities tells a very different story.
That is why strong programs focus on connecting behavior rather than evaluating events in isolation.
Strong programs combine layered controls rather than relying on one method alone.
Basic monitoring systems track payment amounts, destinations, frequencies, and patterns against known fraud indicators. This remains useful for obvious threats but struggles with more sophisticated schemes.
Behavioral systems examine how activity compares to expected patterns, including login timing, device consistency, transaction cadence, and navigation habits. Behavior often reveals what credentials alone cannot.
Risk scoring combines multiple signals into unified decision layers. Rather than blocking based on one trigger, systems evaluate combinations of factors and decide whether to allow, challenge, delay, or escalate.
Instant payments and digital wallets leave little room for delayed review. Systems must assess risk while actions are happening, not hours later.
Some events cannot be resolved automatically. Analysts still need to review edge cases, identify linked entities, and distinguish genuine fraud from legitimate but unusual customer behavior.
Open-source intelligence adds valuable external context to internal signals. It helps analysts understand whether suspicious activity fits a wider pattern involving external identities, infrastructure, relationships, or known abuse indicators.
Useful open-source signals may include:
In practice, OSINT is especially useful when institutions need to understand who is behind an entity, whether multiple accounts may be linked, or whether an apparently isolated event is part of a broader pattern.
External analysis can also expose inconsistencies. A business account may claim one identity while public records, website infrastructure, and external references suggest another. A customer profile may appear normal internally but show wider risk signals when matched to outside data.
Practical anti-fraud workflows usually follow a recognizable pattern.
Monitoring and signal collection. The institution gathers signals from transactions, onboarding, authentication, device behavior, and account activity. This is where automated monitoring systems are most active.
Risk assessment. Rules, models, and scoring systems assess whether events appear normal, suspicious, or high risk. Outputs may include pass, challenge, step-up verification, hold, or escalation.
Investigation. Analysts review flagged cases using internal evidence and, where relevant, external intelligence. This is where programs move from automation into judgment.
Action. Organizations may decline transactions, freeze accounts, block devices, request verification, file internal alerts, or route cases into financial crime review.
Feedback and improvement. Strong programs treat every case as a learning opportunity. Confirmed incidents should refine rules, improve risk models, and strengthen future monitoring logic.
Even mature programs encounter recurring obstacles.
Automated systems can generate huge volumes of alerts. If thresholds are too sensitive, analysts drown in noise. If thresholds are too loose, important cases slip through.
Instant payments and real-time services leave little time for review. Institutions often have to decide before a human can intervene.
Fraudsters test systems, learn thresholds, rotate devices, use mule accounts, and exploit process gaps. The more predictable the defense, the easier it is to work around.
Every challenge step creates the risk of abandonment, complaint, or lost trust. Good controls must protect users without treating every unusual event as malicious.
Fraud signals often live in different systems. Identity, transactions, onboarding, device behavior, and external context may not sit in one place. That fragmentation slows investigations and weakens decisions.
The strongest programs usually share a few traits.
Building layered controls. Strong programs do not depend on one line of defense. They combine onboarding checks, authentication controls, behavioral monitoring, transaction review, and case investigation.
Using context, not just triggers. A single indicator can mislead. The strongest programs focus on combinations of risk signals rather than binary rules alone.
Keeping analysts in the loop. Automation is necessary, but not sufficient. High-value or ambiguous cases still need experienced review.
Learning from confirmed cases. Every confirmed incident should improve monitoring logic, scoring, workflows, and investigation priorities.
Fraud patterns rarely stay inside one system. A suspicious transaction in the payments queue may connect to account activity in onboarding logs, device patterns in authentication systems, and external entities visible only through public records. The challenge is that these signals live in different places, and correlating them quickly enough to stop coordinated schemes is hard.
Social Links helps investigators bridge that gap. Instead of treating each flagged transaction as an isolated event, analysts can connect internal alerts to outside context—business registrations, digital footprints, infrastructure signals, and relationship patterns. That correlation turns scattered signals into coherent fraud networks.
It matters most when institutions need to distinguish between one-off anomalies and organized schemes involving mule networks, coordinated onboarding abuse, or sophisticated identity manipulation.
Fraud prevention is no longer just a matter of blocking suspicious transactions. The harder problem is recognizing when isolated signals are part of a wider scheme and responding fast enough to stop losses before the pattern spreads.
That is why detection depth matters. Rule-based systems still have value, but institutions that combine behavioral analysis, risk scoring, network investigation, and external context are far better positioned to catch organized fraud, reduce false positives, and adapt as attackers change tactics.
Fraud prevention refers to the systems, controls, and investigative methods used to stop fraudulent activity targeting financial institutions and their customers. It includes monitoring, risk scoring, identity verification, and analyst review.
Programs combine transaction monitoring, behavioral analysis, and risk scoring to flag unusual patterns. Stronger programs also use network analysis to connect activity across accounts, devices, and external infrastructure.
Anti-fraud work focuses on preventing unauthorized or deceptive activity such as account takeover, identity theft, or payment scams. Anti-money laundering addresses suspicious financial behavior that may indicate laundering or other financial crime, though the two often overlap.
OSINT adds external context to internal alerts. It can reveal linked entities, suspicious infrastructure, public affiliations, and digital footprint inconsistencies that transaction data alone may not show.
Institutions should look for systems that combine real-time monitoring, behavioral analysis, risk scoring, and investigative tools. The strongest platforms support both automated detection and analyst-led investigation while keeping false positives manageable.
Want to see how intelligence platforms support fraud investigations? Book a personalized demo with one of our specialists and discover how SL Crimewall helps investigators connect suspicious activity, map linked entities, and identify organized fraud patterns through integrated analytical workflows.