OSINT in Military Operations: Supporting Modern Defense


Modern defense operations increasingly rely on information that exists outside traditional classified systems. Satellite imagery, social media activity, commercial flight data, shipping records, and publicly accessible reporting now contribute directly to military intelligence workflows. What was once considered supplementary intelligence has become a persistent source of operational visibility, supporting both strategic planning and real-time situational awareness across modern conflict environments.
In this article, we examine how open-source intelligence supports military operations and how defense organizations translate publicly available data into actionable insight. We explore the analytical layers that structure military OSINT, the role open sources play across strategic, operational, and tactical intelligence, and how these capabilities integrate into the broader defense intelligence cycle to strengthen situational awareness and operational decision-making.
Military OSINT is the systematic collection and analysis of publicly available information used to support defense intelligence and operational decision-making. The goal is not simply to gather data but to transform fragmented public signals into actionable intelligence that supports operational planning, threat assessment, and battlefield awareness.
Unlike classified intelligence gathered through covert means, open-source collection relies on legally accessible data sources such as:
Open sources rarely replace classified intelligence. Instead, they expand visibility, validate findings, and provide context in environments where traditional collection faces limitations.
Military OSINT functions most effectively when it operates across three complementary analytical layers. Each layer contributes a different form of visibility, and together they allow analysts to move from raw observation to meaningful intelligence. Monitoring identifies signals, verification establishes reliable facts, and pattern analysis places those events within a broader operational context.
Persistent monitoring provides continuous observation of publicly observable indicators across areas of interest. Open sources allow analysts to maintain a baseline view of activity even when other intelligence assets are unavailable or focused elsewhere.
Common monitoring signals include:
Continuous monitoring helps analysts detect unusual activity, emerging patterns, or sudden changes that warrant closer investigation. However, observation alone rarely explains intent. Monitoring reveals what is visible in the environment, but additional analysis is needed to determine why those developments matter.
When unusual activity or claims emerge, analysts move to event verification. This layer focuses on confirming whether reported incidents actually occurred and establishing reliable facts through multiple sources.
Verification often involves:
Open-source verification is especially important in environments where conflicting narratives, misinformation, or incomplete reporting circulate. By combining geolocation techniques, metadata analysis, and cross-source comparison, analysts can establish credible accounts of events. While verification strengthens confidence in reporting, it typically remains reactive—confirming what occurred rather than predicting future actions.
Pattern analysis builds on monitoring and verification by examining indicators across time, geography, and multiple data sources. Instead of focusing on individual incidents, analysts look for trends that reveal operational behavior.
This analysis may involve:
By correlating observations across multiple events, analysts can detect shifts in military posture, emerging operational priorities, or evolving campaign strategies. At this stage, OSINT moves beyond observation toward deeper interpretation. However, careful judgment remains essential. Adversaries may deliberately generate misleading signals, and correlations do not always reflect genuine operational intent.
Military OSINT becomes most valuable when these layers operate together.
Consider a typical workflow. Persistent monitoring identifies unusual activity at a military installation through commercial satellite imagery. Event verification cross-references the observation with social media posts, transportation data, and news reporting to confirm the movement. Pattern analysis then places that activity within a broader campaign context, comparing it to historical logistics patterns to determine whether the movement represents routine rotation or operational preparation.
No single layer answers every intelligence question. Monitoring provides the initial signal. Verification establishes facts. Pattern analysis generates meaning.
When these layers remain isolated—for example, when satellite analysts do not coordinate with social media monitoring teams or when tactical observations never inform strategic assessment—intelligence becomes fragmented rather than cumulative.
OSINT supports defense operations at multiple levels, each with distinct analytical requirements.
At the strategic level, open sources inform long-term planning and policy decisions:
Organizations such as the United Nations Institute for Training and Research and its UNOSAT program demonstrate how satellite imagery analysis supports both humanitarian and defense-related strategic assessments.
At the operational level, OSINT supports commanders responsible for planning and executing campaigns:
Commercial satellite providers increasingly publish imagery used to document troop deployments, infrastructure changes, and operational activity across conflict zones.
At the tactical level, open sources contribute directly to battlefield awareness:
Analysts combine social media posts, drone imagery, civilian video footage, and real-time data feeds to reconstruct tactical situations with increasing accuracy. Organizations such as Bellingcat have demonstrated how open-source verification techniques can reconstruct military events using publicly available information alone.
Open-source intelligence feeds directly into the broader defense intelligence cycle, where publicly available information is collected, analyzed, and translated into operational decisions. In military OSINT workflows, this process typically unfolds across several interconnected stages.
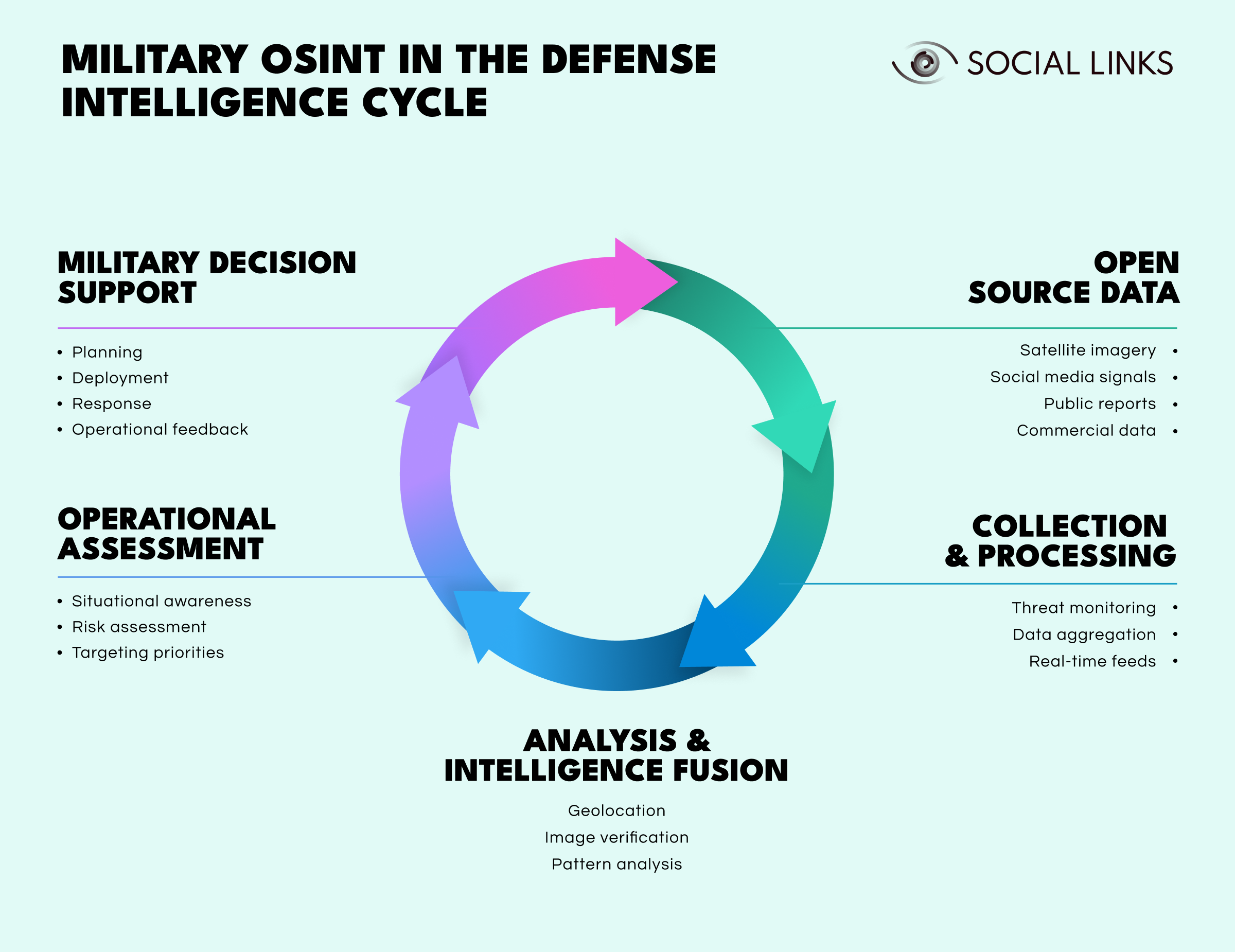
Open source data. Analysts gather publicly accessible information such as satellite imagery, social media signals, public reporting, and commercial datasets that reveal observable indicators of military activity.
Collection and processing. Analysts aggregate and monitor data through automated feeds and analytical tools to identify emerging patterns, anomalies, or unusual developments.
Analysis and intelligence fusion. Analysts verify events, geolocate imagery, and correlate multiple sources to transform fragmented observations into structured intelligence.
Operational assessment. Analysts evaluate intelligence within a broader operational context to assess risks, improve situational awareness, and identify potential targeting priorities.
Military decision support. Commanders use the resulting intelligence to guide planning, deployment decisions, and operational responses.
As operations unfold, new observations feed back into monitoring and analysis. The cycle repeats continuously, allowing intelligence teams to refine their understanding of adversary behavior and maintain persistent situational awareness.
Geospatial intelligence represents one of the most valuable components of open-source military analysis.
Commercial satellite imagery allows analysts to:
Geographic information systems and remote sensing platforms allow analysts to combine imagery with mapping data, producing layered intelligence models that support operational planning.
Public satellite programs such as the European Space Agency offer open datasets widely used in conflict mapping and environmental monitoring. The key advantage is persistence. Open satellite coverage allows monitoring even when classified collection assets are unavailable or focused on higher-priority targets.
Effective military OSINT depends less on individual tools and more on integrated analytical environments that connect data sources, processing capabilities, and human expertise.
Modern intelligence platforms typically combine:
These capabilities transform large volumes of open data into prioritized intelligence rather than overwhelming analysts with raw information.
For example, satellite imagery may reveal increased vehicle activity at a military base. Automated systems flag the change and correlate it with nearby social media posts mentioning unusual traffic. GIS tools map the activity against known logistics routes, while pattern analysis compares the observation to historical baselines. Analysts receive an alert with the relevant context already assembled, allowing them to focus on interpretation rather than manual data gathering.
Without integration, each data source remains isolated. When properly connected, disparate signals combine to reveal operational meaning.
Despite its advantages, military OSINT presents persistent challenges that require disciplined methodology and realistic expectations.
Public data frequently contains misinformation, outdated reporting, manipulation, and deliberate deception. Adversaries increasingly exploit open platforms to spread misleading narratives designed to distort intelligence analysis.
Verification therefore remains essential. Multiple independent sources, metadata examination, and geolocation techniques help confirm authenticity, although uncertainty can never be eliminated completely.
Modern conflicts generate enormous volumes of imagery, social media posts, and digital communications. Without effective filtering mechanisms, analysts can become overwhelmed by data rather than supported by it.
Risk-based triage, automated anomaly detection, and analyst-defined collection priorities help focus attention on operationally relevant information.
Military actors increasingly understand that their activities can be observed through open sources. They adapt accordingly, using camouflage, concealment, deception, and operational security measures specifically designed to frustrate open-source monitoring.
This creates an ongoing intelligence competition between observation and counter-observation.
Improper handling of open intelligence may expose analytical priorities, reveal collection methods, or inadvertently disclose sensitive operational information.
Responsible governance frameworks must balance intelligence sharing with operational security.
Several trends will shape the evolution of military OSINT in the coming years.
Maintaining analytical rigor will become increasingly important as data volumes grow and adversaries exploit open information environments.
Military OSINT has moved from a supplementary capability to a core component of modern defense intelligence. Publicly observable data now contributes directly to situational awareness, operational planning, and battlefield assessment.
The most effective programs combine persistent monitoring, rigorous verification, and long-term pattern analysis while integrating open sources into the broader intelligence cycle. As commercial data sources expand and conflicts become increasingly transparent, the ability to interpret publicly available information will remain a critical advantage for defense and intelligence organizations.
Military OSINT is the systematic analysis of publicly available information used to support defense intelligence and decision-making. It helps analysts monitor threats, verify events, and support operational planning using sources such as satellite imagery, social media, and open reporting.
Open-source intelligence relies on publicly accessible information, while classified intelligence often involves covert collection methods. OSINT complements classified sources by providing persistent, scalable visibility.
The three layers are persistent monitoring, event verification, and pattern analysis. Together they allow analysts to move from observation to verification and ultimately to strategic interpretation.
Yes. Open sources can improve tactical awareness by tracking movements, verifying incidents, and identifying emerging threats when properly verified and integrated into operational workflows.
Key challenges include misinformation, data overload, adversary deception, and operational security risks. Strong verification practices and disciplined analysis help address these challenges.
Want to see how unified intelligence platforms support military open-source intelligence and multi-source analysis? Book a personalized demo with one of our specialists and discover how SL Crimewall helps defense and intelligence organizations correlate geospatial data, verify information across sources, and support operational decision-making through structured analytical workflows.