Top OSINT Films and Series: Part 2


Remember our recent selection of OSINT films (in case you missed it, here it is)? Now it's time for the second part, where we’ll focus on fiction. Given that entertainment media continues to provide value for professionals working in the sphere, narrative developments can inspire viewers to think outside the box (and it’s quite fun too).
Word of warning, the movie industry takes liberties with how hacking, technology, and the Internet function. So consider these choices as enjoyable films that showcase elements of OSINT, although some of the picks go above and beyond and detail a complete investigation with remarkable accuracy. We have lots of options for you, from serious ones to more entertaining picks. Grab your popcorn and enjoy the show!

Let’s kick things off with one of the most realistic portrayals of cybersecurity in media. The series focuses on Elliot, a hacker and cyber-vigilante who grapples with personal issues. He gets recruited into a hacktivist organization that aims to help the general public by erasing all credit card debt from the databases of one of the largest companies in the world. However, the firm in question is the client of the corporation the protagonist works for.
The show is famous for embracing technical jargon, which only enhances the authenticity of the setting. The characters are experts in their field, and the way they look and talk reflects this. The plot showcases a lot of OSINT concepts that investigators and analysts encounter daily. So by that virtue alone, the series would be a clear recommendation for anyone interested in the field or those who want to see hackers in action.
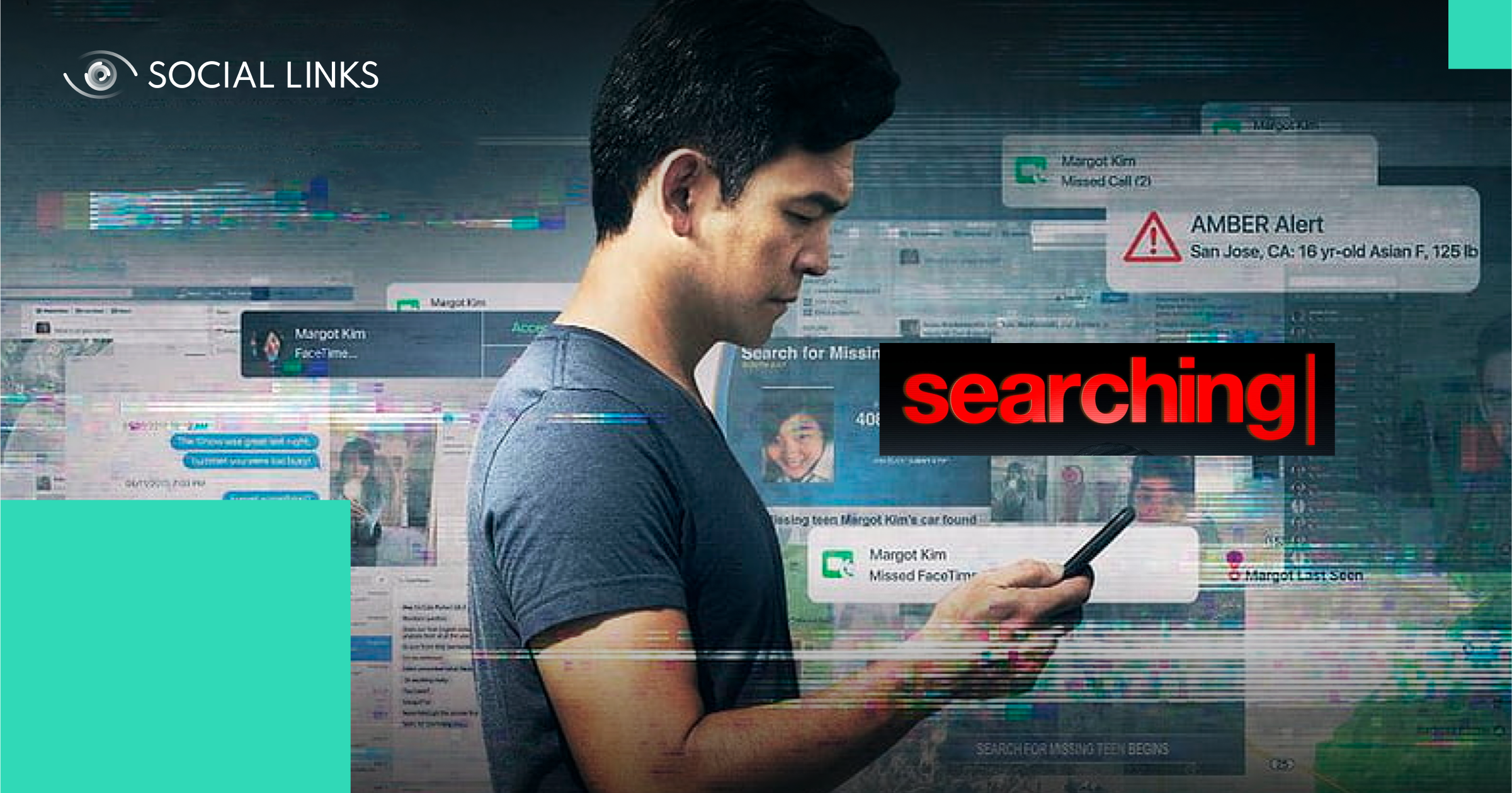
Second, on our list is a film demonstrating the extreme lengths a parent will go to find their missing child, all shown through a computer investigation. The plot revolves around a father’s search for his missing daughter, told from the perspective of the girl’s laptop screen. While the story is entirely fictional, the platforms, user interfaces, and brands are completely authentic. Furthermore, the social media experience depicted in the movie is entirely genuine.
The film successfully conveys investigators' various branching pathways during a criminal inquiry. Furthermore, the constrained point of view highlights how deeply specialists can delve into cases through online interactions and publicly available data sources. The feature works extremely well as an answer to anyone questioning the effectiveness of social media investigations.

Third, we have a series featuring an intelligence analyst who uncovers a conspiracy through a crossword puzzle. The show is a spy thriller without traditional spycraft, creating an unpredictable and dangerous world. The main character finds himself in a web of deception and murder, where everyone seems like a potential victim or killer. Moreover, the riddle at the heart of the series offers a refreshing take for fans of conspiracy fiction.
A word of warning, this show is slow-paced but provides many opportunities for viewers to experience an analyst's mindset. Sequences mirror online investigations, except they take place in the outside world. Masked individuals provide valuable information before disappearing into the shadows, and the atmosphere is distinctly urban and dangerous. However, the protagonist is resourceful and displays a clear OSINT mentality in his theories.

Our next pick is a comedy-thriller dealing with the online phenomenon Cicada 3301. In the early 2010s, unexplained puzzles would appear online with no directions whatsoever for several years. The event captivated the minds of cryptography enthusiasts, so it was only a matter of time before it became a movie plot. The film centers on Connor, who gets involved with the puzzles and finds himself sucked into a shadowy cyber-terrorist recruitment program.
The movie is not accurate when it comes to how hacking works, it’s the standard Hollywood “hacking is magic” take. However, the filmmakers did a great job of visualizing the characters' thinking patterns when dealing with the puzzles. This method helps in showcasing the connections the characters are making in their head, as it’s similar to having several tabs open in a browser and jumping between them.
Next, we have a movie about a hacker who turns himself in to aid law enforcement in bringing down a notorious cyber-criminal group. The rest of the film details the background and context for the main character’s actions, from forming a hacktivist organization to affecting the flow of the stock market through hacking. With increasingly elaborate plans, the film shows how malicious actors compete for infamy and the real-world consequences of their actions.
Who am I? presents a closer-to-reality look at how hacking works. The characters are competent at bypassing security measures with plausible methods. For example, when the protagonist acts like an IT technician and simply walks up to a laptop to gain access to the system. The plot depicts Dark Web hacker culture quite faithfully, and the use of jargon throughout makes sense within the context of the film.
Our next entry is a keenly self-aware show poking fun at the overly serious tone of true crime shows while keeping true to the heart of the genre. The series deals with a case of vandalism at a US high school, the punishment of the supposed perpetrator, and the investigation that unfolds to verify that fact. The format of the show is an amateur mockumentary, shot like a series of online videos for Vimeo.
The series reproduces the feeling that the “documentary crew” is part of the setting, interviewing people and trying to get to the heart of the truth. The exciting dynamic this creates involves the faculty becoming aware of the increased scrutiny the school is getting, sometimes to the point of unwanted attention. Such developments directly impact the way the show is shot, as at specific points, the act of filming resorts to hidden cameras as gathering footage becomes restricted.

An adaptation of the acclaimed Swedish book of the same name. The storyline centers around a journalist who enlists the help of a skilled hacker to unravel an old mystery. There are two versions of the movie, but here we'll focus on the American remake as it stands as a compelling standalone story, though the narrative remains consistent in both versions.
The plot delves into dark and intense territories, shedding light on cultural misogyny and the predatory actions of individuals in positions of power. Lisbeth's character takes center stage, leading us into the intriguing world of OSINT and cybersecurity. The movie beautifully showcases that sometimes, the truth lies in plain sight, waiting to be discovered through an inquisitive perspective that connects the dots.

For this pick, we have a compelling biographical retelling of the journey of Edward Snowden, a whistleblower and former intelligence consultant who revealed the NSA's mass surveillance program to the world in 2013. The movie skillfully navigates through the events leading up to Snowden's meeting with journalists, the profound impact of the information going public, and how his life was affected by the ordeal.
Edward’s act of whistleblowing marked a critical turning point in the realm of intelligence and data privacy. With the truth exposed, covert surveillance operations became a cause of concern for many individuals, sparking a global conversation on privacy rights and digital security. It prompted the general public to delve deeper into cybersecurity hygiene and the importance of understanding safety measures to safeguard their data and protect their digital presence.

Next, we have a movie about celebrity worship and how malicious actors can take advantage of such situations. The main character, Nick, runs a fansite dedicated to an actress and is informed that he won a contest to meet her. From this point on, it becomes a tale about a manhunt and blackmail. While the plot does take liberties with how technology works, the film is still an entertaining ride throughout.
The movie showcases an underground hacker group that takes cues from existing hacktivist organizations. While the movie doesn’t explicitly deal with open-source intelligence, elements that provide relevant insight are still explored throughout the storyline. Furthermore, the film's name is reflective of the aesthetic of the production, as the entire action takes place over a series of open windows on a laptop screen.

Last but not least, we have a film that is an unofficial sequel to Searching, which we introduced in the beginning. Plot-wise, the movies are very similar; both deal with missing people and the social media-driven investigation conducted by their relatives. However, the difference with this one is that the daughter is looking for her mother, who has gone missing in another country. Now, the issue of performing a global investigation becomes the center point.
This one extends on the groundwork laid by the original. Translation solutions and map software have become vital tools for research. However, a central point of the movie is that the main character is not a hacker. She makes logical, informed decisions and learns more about her mother’s circumstances. The film showcases the OSINT mindset at its strongest, and it’s a testament to the effectiveness of open-source intelligence.
And that’s a wrap on part two of our OSINT movies and series recommendations! We hope you’ll find something valuable in each of our picks, and we’re excited to see how movies will incorporate open-source intelligence into their plots in the future. Check our blog for more insights and updates to learn more about OSINT.