Tracing Exploitation: Investigating Human Trafficking Networks


Human trafficking rarely unfolds as a single isolated crime. In most cases, it is sustained by organized networks that recruit victims, control their movement, manage exploitation, and profit across multiple locations. Effective investigations therefore need to do more than respond to individual incidents. They need to identify how exploitation is organized, who enables it, and how the network can be disrupted without putting victims at greater risk.
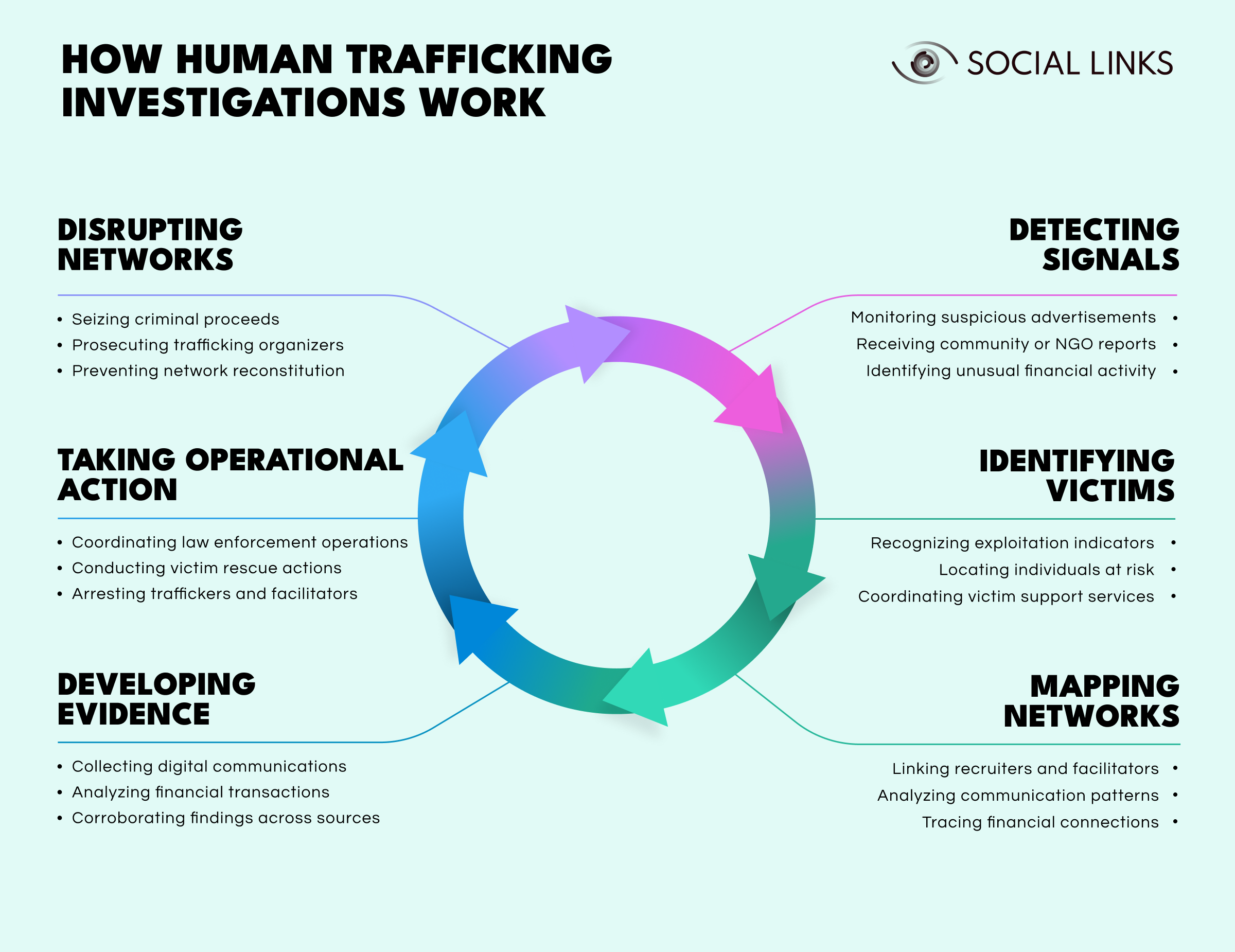
In this article, we examine how human trafficking investigations identify exploitation networks while protecting the people being exploited. We explore how investigators detect early warning signs, identify victims, build evidence through digital and financial analysis, and coordinate action against traffickers across jurisdictions.
Human trafficking involves recruiting, transporting, harboring, or obtaining individuals through force, fraud, or coercion for the purpose of exploitation. The internationally recognized legal definition comes from the United Nations Palermo Protocol, which established global standards for prevention, prosecution, and victim protection.
A key principle under this framework is that victim consent is irrelevant when coercion or deception is involved. A person cannot meaningfully consent to exploitation when threats, manipulation, abuse, or dependency remove their freedom of choice.
Anti-human trafficking refers to the broader response to this crime: the coordinated efforts of governments, law enforcement agencies, international organizations, and civil society to prevent trafficking, identify victims, and dismantle the networks behind exploitation.
Human trafficking appears in several forms, all involving severe exploitation.
Labor trafficking. Victims are forced to work under exploitative conditions in industries such as construction, agriculture, domestic labor, or manufacturing. Control methods often include withheld wages, confiscated documents, debt manipulation, and threats of violence.
Sex trafficking. Individuals are exploited through forced prostitution, escort services, or other forms of commercial sexual exploitation. Traffickers often rely on violence, psychological coercion, or substance dependency to maintain control.
Child trafficking. Children may be trafficked for labor exploitation, sexual abuse, forced begging, criminal activity, or illegal adoption schemes. Under international law, any commercial sexual exploitation of a minor constitutes trafficking, regardless of whether force or coercion is present.
These forms frequently overlap. The same network may operate across multiple forms of exploitation at once.
Responding to trafficking requires coordination across institutions.
Key actors include:
These partnerships matter because trafficking networks often operate across borders. Investigations, victim support, and enforcement action rarely succeed in isolation.
Trafficking networks usually function through distributed structures that separate leadership from direct exploitation. This reduces the exposure of senior organizers while allowing the operation to continue even if lower-level participants are identified or arrested.
Recruitment is often the first stage of trafficking activity. Traffickers commonly use:
Digital channels have made this easier. Online platforms allow traffickers to contact vulnerable individuals directly while disguising their real intentions.
Once victims are recruited, traffickers move them through networks designed to increase dependency and reduce the chance of escape.
Common control mechanisms include:
Many trafficking operations rely on movement between cities, regions, or countries. This not only supports the exploitation model but also makes detection and victim recovery more difficult.
Digital platforms now play a central role in trafficking operations beyond recruitment alone.
Traffickers use online environments to:
These platforms help traffickers operate more discreetly, but they also create digital traces that investigators can analyze.
Human trafficking investigations rarely begin with a complete picture of the network. More often, they start with fragments: a suspicious advertisement, a tip from an NGO, an unexplained financial pattern, or a victim account. From there, the investigation develops into a broader effort to identify victims, map the network, build evidence, and take coordinated action.
Investigations often begin with early warning signs of exploitation. These may include:
At this stage, investigators usually have only pieces of information. Those signals must be validated and connected before the broader structure becomes visible.
Once those signals are reviewed, investigators focus on identifying the people being exploited. This may involve recognizing repeated advertisements, individuals appearing in multiple locations under suspicious circumstances, or recruitment posts targeting vulnerable populations.
Victim identification often depends on close coordination with support organizations that can provide trauma-informed assistance, immediate protection, and safe next steps.
As more information comes in, investigators begin identifying how traffickers, facilitators, recruiters, and exploiters are connected. This may involve:
The goal is to move beyond isolated incidents and understand the wider exploitation network.
Strong trafficking cases rely on multiple forms of evidence. Investigators may collect:
Building evidence this way reduces reliance on victim testimony alone and strengthens the case against traffickers.
Once victims are identified and evidence is developed, law enforcement can begin coordinated action. This may involve victim rescue operations, arrests of traffickers and facilitators, and targeted interventions against locations or businesses tied to exploitation.
Timing matters here. Operational action must protect victims rather than place them at greater risk.
The final goal is not simply making arrests, but weakening the network’s ability to continue operating. That may involve:
Effective investigations do not stop at identifying exploitation. They aim to disrupt the systems that sustain it.
Victim welfare matters in any serious investigation, but in human trafficking cases it is inseparable from the investigative process itself. Investigators are often dealing with people who are still under coercive control, afraid of retaliation, distrustful of authorities, or dependent on the very people exploiting them. That reality affects how victims are identified, how evidence is collected, and how enforcement action is planned.
A victim-centered approach emphasizes:
These principles also shape the ethical responsibilities of the investigation itself. Victims must understand that they are not obligated to participate in criminal proceedings and that support services remain available regardless of their decision. Their identities should be protected in public records wherever possible to reduce stigmatization and retaliation. Investigators also need trauma-informed interviewing practices that minimize further harm, as well as a clear respect for victim autonomy throughout the case.
Victims may be reluctant or unable to cooperate because of trauma, threats against their families, immigration concerns, financial dependence, or manipulation by traffickers. Recognizing those conditions helps investigators build trust, protect victims from further harm, and continue developing evidence through financial records, digital traces, witness accounts, and other independent sources.
Ethical practices are not separate from effective investigations. In many cases, they strengthen prosecutions by building long-term trust and making victim participation safer and more sustainable.
Open-source intelligence helps investigators examine publicly available information that reveals trafficking activity. It complements traditional investigative methods by identifying patterns that traffickers leave visible online.
Social media monitoring can reveal indicators such as:
These signals often help identify networks before victims report exploitation directly.
Traffickers frequently reuse recruitment strategies across platforms. Investigators analyze patterns such as:
Recognizing these patterns helps distinguish organized recruitment activity from isolated cases.
Digital activity often leaves traces that can be correlated across platforms. Investigators may connect:
Linking these identifiers helps reveal relationships between individuals involved in trafficking operations.
Investigators rely on multiple information sources to analyze trafficking activity.
Social media data provides insight into recruitment patterns, advertising activity, and relationships between suspected traffickers.
Messaging platforms often coordinate logistics between participants. Even when content is encrypted, communication patterns and contact networks may still provide useful intelligence.
Public records may reveal infrastructure supporting trafficking operations.
Relevant sources include:
These records can expose connections between trafficking participants and the businesses or properties used to facilitate exploitation.
Despite growing awareness, trafficking investigations face several persistent challenges.
Victims are often isolated through coercion, manipulation, and threats. Trauma, fear of retaliation, and immigration concerns can prevent them from reporting exploitation or cooperating with authorities.
Many trafficking networks operate internationally. Differences in legal frameworks, evidence standards, and investigative authority can complicate enforcement action.
Traffickers increasingly rely on encrypted messaging and anonymization tools. Even when message content is inaccessible, investigators can still analyze metadata, financial activity, and digital footprints to understand network structures.
Technology helps investigators process large volumes of digital and financial data, identify patterns across cases, and connect signals that would otherwise remain isolated.
Advanced analytics systems help investigators identify trafficking indicators across large datasets, including online advertisements, recruitment messaging, financial activity, and communication records.
Network analysis tools visualize relationships between suspects, accounts, phone numbers, and financial transactions. These tools help identify coordinators, intermediaries, and operational structures within trafficking networks.
Specialized investigation platforms combine multiple data sources into unified analytical environments, allowing investigators to correlate digital signals and map relationships between suspects.
Because trafficking networks operate across jurisdictions, international cooperation is essential. Organizations such as INTERPOL, Europol, and UNODC facilitate intelligence sharing and coordinated investigations. These partnerships allow authorities to conduct joint operations, share intelligence, and prosecute traffickers operating across borders.
Without this cooperation, trafficking organizations can exploit jurisdictional gaps and shift operations to regions with weaker enforcement capacity.
Investigative approaches continue to evolve as traffickers adopt new technologies.
Several trends are shaping the future of this work:
These developments allow investigators to identify exploitation earlier and dismantle trafficking networks more effectively.
Effective human trafficking investigations require balancing victim protection with evidence development and network disruption.
Investigations that prioritize victim safety while building cases through digital intelligence, financial analysis, and network mapping produce stronger results for both survivors and law enforcement.
Successful responses depend on trauma-informed practices, international cooperation, and a sustained commitment to dismantling the systems that allow exploitation networks to operate.
Human trafficking involves recruiting, transporting, or harboring individuals through force, fraud, or coercion for exploitation. Investigations combine victim identification, network mapping, digital intelligence, and international cooperation to dismantle trafficking operations while protecting survivors.
Early indicators include suspicious online advertisements, reports from NGOs, tips from witnesses or victims, unusual financial patterns, and proactive law enforcement monitoring. These signals are validated and connected to identify broader networks.
Victim-centered investigations prioritize safety and wellbeing while building cases. They focus on trauma-informed practices, coordinated support services, and collecting evidence through multiple independent sources rather than relying solely on survivor testimony.
OSINT reveals patterns across social media, online marketplaces, and digital platforms. Investigators use it to identify recruitment activity, link digital identities, track communication patterns, and map relationships between suspected traffickers.
Trafficking networks operate across borders while law enforcement authority remains jurisdictional. International cooperation through organizations like INTERPOL and UNODC enables intelligence sharing, coordinated operations, and prosecution of cross-border networks.
Want to see how unified intelligence platforms support human trafficking investigations? Book a personalized demo with one of our specialists and discover how SL Crimewall helps law enforcement agencies identify exploitation networks, correlate digital evidence, track financial flows, and support victim-centered investigations through integrated analytical workflows.