Recruitment on the darknet: tools for analyzing extremist profiles
A Case Study of How Social Networks Act as Recruitment Pools And What Tools Can Be Used to Counter Illicit Activity on The Internet
With Maltego and Social Links Pro's help, the Lowfare team conducted a study about recruiting processes in a number of international racial-extremist groups in the Darkweb. Members of this group are united by Ironmarch.org – an extremist social network.
A study of more than 1,207 regular users and 195,000 public posts was conducted, and 4,500 private conversations were analyzed using the Maltego and Social Links Pro to identify the sources and mechanisms of the organization's functioning. In the result of the study, it was found that approximately 15 percent of all private conversations between Iron March members starting at the end of 2015 related to recruitment, coordination, and philosophical discussions about extremism.
The Social Links team has prepared step by step guide on how this Darkweb investigation was conducted.
It is no secret that terrorist and extremist organizations use the internet and social networks to communicate and seek recruits. The instruments for identifying potential candidates with like-minded interests are available in simple search queries for communities in social networks, and the extremists get ready-made lists of members.
White extremism is becoming a severe threat to national security in the United States as the number of racially motivated attacks has been on the rise for years. The abundance of extremist content available on the internet and in specialized communities and forums on extremist topics serves as a breeding ground and magnet for potential criminals.
Using the data leaked from Iron March, open-source research, and the Maltego platform supplemented by the Social Links add-on, the study tried to answer the following questions:
Understanding how white supremacist and neo-Nazi networks operate and recruit is critical to mitigating this threat. One way to collect intelligence on these groups is to track their activity on certain public and restricted websites. The recent hack and data-dump of a white supremacist website provides a window into that kind of activity.
The research produced two conclusions. First, the networks and relationships developed on Iron March did not appear to be replicated on public social media platforms, suggesting that the platform was critical to connecting like-minded individuals and helping white supremacist and neo-Nazi groups recruit new members. Second, most Iron March users did not appear concerned about law enforcement surveillance on the site and did not take measures to hide their activity.
One of the most prominent channels for white supremacist activity was the Iron March website. The forum acted as a channel of communications for extremists and contained vast amounts of content. However, on November 6, 2019, the entire SQL database behind Ironmarch.org was posted on Internet Archives. The data released by an unknown individual includes private messages, user account information, and the site's forum posts. The data was then analyzed by investigative journalists and Bellingcat and acted as the basis for the given study.
Working with vast amounts of data requires preliminary preparations and careful analysis of the available datasets to ensure that the tools used will properly sift the information flows and provide accurate results.
The most significant and most challenging task in preparing for repeating the workflow process will be preparing the data. Only 1200 user Aliases were utilized for researching the entire leaked database. All entered in CSV (or Excel) format for import into Maltego Classic.
The function of Maltego called "Import a 3rd Party Table" was used for the import. The import setup procedure consists of 6 steps, of which 2-4 determine the resulting graph. Step 2 is selecting the file.
Step 3 is determining the nature of the relationship between the imported elements. In the given case, the Aliases list was imported with the "no links" option selected. The bottom prompt describes the logic with which the links are created under various options. That is why one should pay close attention to preparing the data before importing. The sense of the future visualization in Maltego should already be embedded in the structure of the data being used.
Step 4 is the direct import. At this stage, it is worth translating the data into the language of Entities used by Maltego. The nicknames of the users in social networks in the language of Maltego (and not only in Maltego) are called Aliases. That is why the "Alias" mapping option should be selected.
The perfect template of 1,200 Aliases is thus created on the graph and is ready for analysis.
The main task is to identify and link Facebook, Twitter, and Instagram profiles for the selected Aliases. It is necessary to choose the appropriate Search Methods (Transformations) in the Social Links Pro list.
In the case of Instagram and Twitter, there are two Transformations available from the Alias entity. The methods available are [Twitter] To User and [Instagram] To Profile, since these methods provide one-to-one correlation, in case such a profile exists. The other two ways search Aliases that are specifically defined and similar.
There is only one method available from Aliases on Facebook, and it leads directly to the user profile: [Facebook] Get Profile.
The decision was also made to divide the workflow into three:
Once the Aliases are imported, the three graphs are created, and the transformations are selected, it is possible to start the search by selecting all Entities and running needed modifications. The data collection process will take about 30 minutes.
Out of nearly 1,200 Aliases, it was possible to identify about 600 profiles on Twitter and Instagram and about 500 on Facebook as of May 2020. Aliases with no results were deleted from the graphs.
Selection of transformations for the analysis of links in social networks among the identified profiles. It is now necessary to attempt to establish connections among the profiles to get the same result as in the following paragraph of the article:
This close-knit network of users did not appear to exist on more public social media platforms. Using the research capabilities provided by Maltego and the Social Links add-on, we discovered 293 Facebook pages, 151 Twitter accounts, 357 possible Instagram accounts, and 102 VK accounts linked to various Iron March members. Neither the VK nor Instagram accounts identified followed each other or had any friends in common. Furthermore, only 25 Facebook accounts and 20 Twitter accounts linked to Iron March users were connected as "friends" or "followers" or had at least one mutual "friend" or "follower."
Achieving the same results, it is necessary to select needed transformations as the first step. For Instagram and Twitter, a similar set of two transformations will be used: User Followers and User Following. Both will be launched simultaneously on graphs with Twitter and Instagram accounts. Thus, it will be possible to get a complete picture of (1) subscribers, (2) subscriptions of the accounts under study, as well as (3) links between accounts.
For researching Facebook, four transformations will be used:
[Facebook] Followers
[Facebook] Users Followed
[Facebook F] Friends
[Facebook MF] Search Relations
The transformation under item d) will be useful for accounts that have a private list of friends. This transformation analyzes the activity on the user's page and the lists of all active users.
Another convenient feature of Maltego should also be mentioned. To not get confused in the results about which accounts were the source ones and which ones were obtained as a result of enrichment, it is possible to mark all the source accounts with colored tags. To do this, it is necessary to assemble the accounts in separate Collections, select the entire group of accounts and assign a color to this group, as shown in the screenshot. When analyzing the results, it will be possible to separate some accounts from others easily.
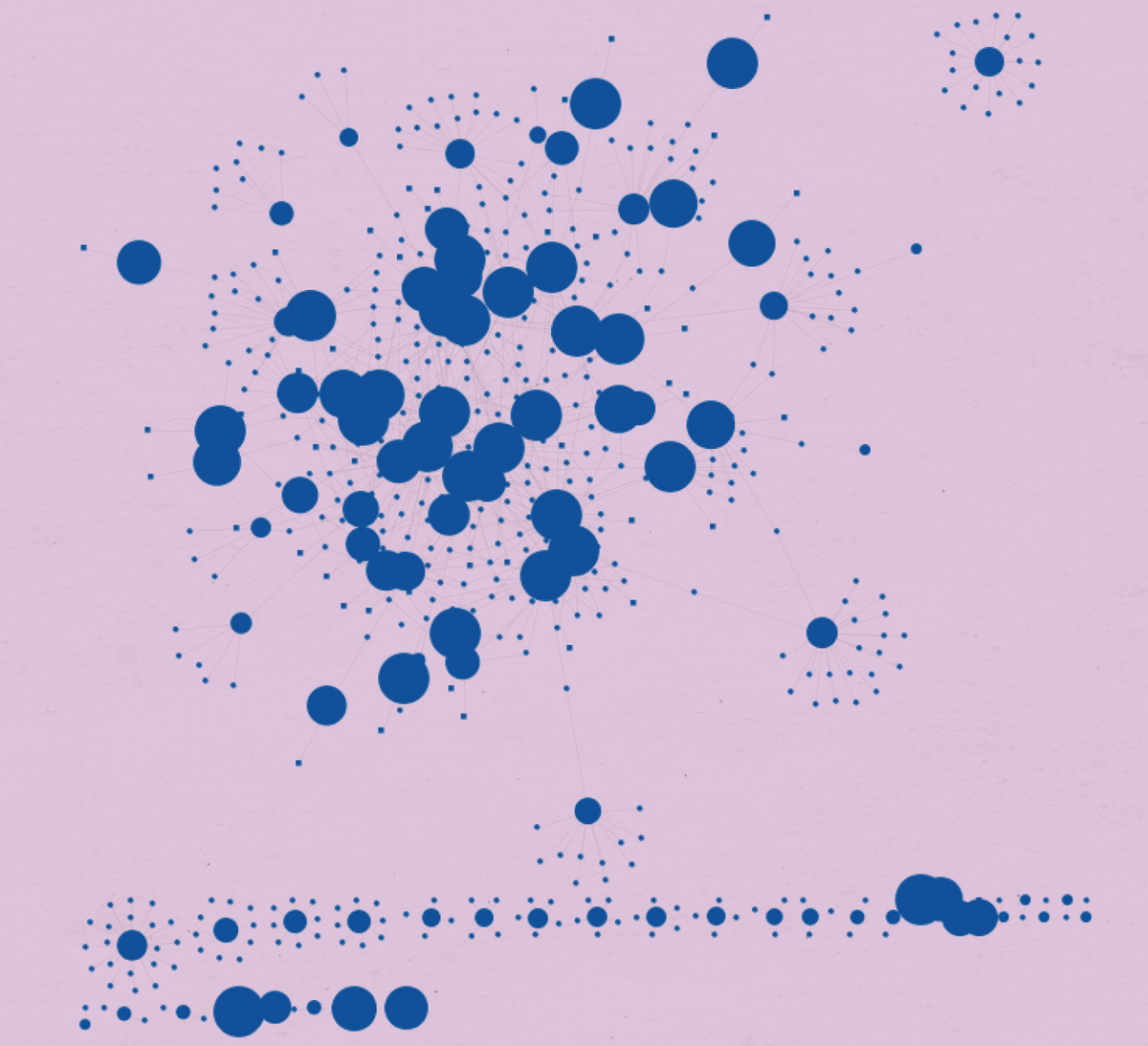
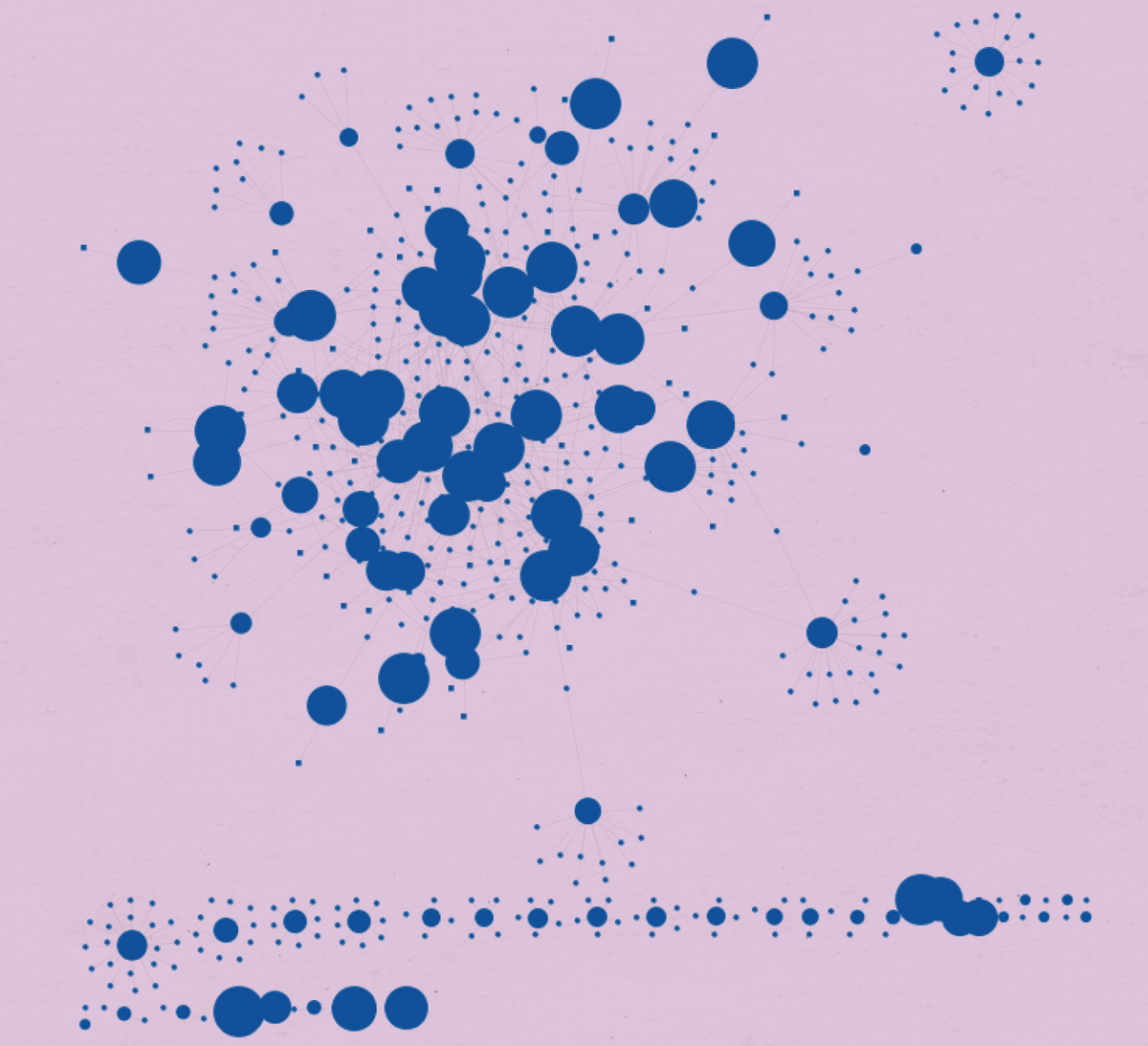
For visual analysis of the results, it is most convenient to switch to Layout mode "Organic." It is also possible to adjust the settings of the View for greater convenience. The larger the entity's size, the more links it has with other entities, which means that the more active the user will be included in this account group.
A method that Social Links Pro did not have at the time of the investigation made for Lawfare was used in this case, namely, a search on Facebook and Linked In via email. The main advantage of the given method is that it provides a 100% accurate link between the Profile and the email address to which the Profile is linked.
The transformation group in question is called "Lookup by..." For example, having entered an email out of the leaked database, we were able to identify more than 100 uniquely linked existing profiles in Linked In. If a transformation [LinkedIn] User Details are later made based on the obtained profiles, it is possible to get the workplaces and user locations from Linked In accounts. The results of such a process are invaluable to investigations.
In total, the process was carried out in 4.5 hours and was interrupted only by using the Social Links Pro daily limit of 3,000 transformations.
It is impossible to estimate the time it would have taken to investigate if it had been carried out using various tools with result transfers from one program to another. With Maltego Classic / XL + Social Links Pro, the work was carried out in a single working environment.
Conducting such analysis manually is merely impossible.
It is convenient to work with many entities in Maltego and conduct visual analysis, even when it comes to 10,000 + entities on a graph. There are many different ways of simplifying the investigation and not getting confused. The various Layouts and Views and the ability to mark or distinguish entities with colors make the process more convenient.
Jacques Singer-Emery is a recent graduate of Harvard Law School and previously spent four years in the New York Police Department (NYPD), first as a policy advisor to Police Commissioner Bratton and then as a Case Analyst for the NYPD Intelligence Bureau. He is the Editor-in-Chief of the National Security Law Journal and a researcher for Professor Philip Heymann and Professor Blum. Jacques graduated Magna Cum Laude from Princeton University in 2013.