Threat Intelligence Feeds: Extracting Intelligence from Indicators


Security teams face a choice when integrating external intelligence. They can consume feeds as simple blocklists and treat each indicator as an isolated fact, or they can use those feeds as starting points for understanding broader campaigns, infrastructure, and attacker behavior. That choice determines whether feeds reduce workload or just add noise.
In this article, we examine how security programs move from basic feed consumption to intelligence-led operations, why some teams get far more value from the same sources than others, and how integration depth affects detection quality. We also look at open source versus commercial options, which sources and platforms matter most, and where external intelligence fits into real security workflows.
Threat intelligence feeds are structured streams of security data that help teams identify known or suspected malicious infrastructure, artifacts, and behavior. In practice, they often include malicious IPs, suspicious domains, URLs, hashes, malware indicators, and other indicators of compromise (IOCs).
Some feeds are narrow and tactical. They focus on one type of observable, such as phishing URLs or botnet command-and-control servers. Others sit inside broader platforms that let analysts connect those observables to malware families, threat clusters, sightings, or incident context.
That difference matters. A list of suspicious IPs can support blocking. A platform that helps analysts connect those IPs to campaigns, malware, and prior sightings is much more useful for hunting, triage, and investigation.
External intelligence matters because most security teams are overwhelmed by alerts and short on context. A feed does not just tell you that something looks bad. A good one helps you understand whether an indicator is already known, how it has been seen elsewhere, and whether it deserves immediate action.
Used well, external intelligence supports:
It becomes especially useful when paired with SIEM, EDR, firewall, email, or TIP workflows. If an internal alert involves a known malicious domain or hash, the analyst starts with context instead of starting from zero.
Not all feeds are equally useful, though. The best ones are timely, relevant, structured, and maintainable. The worst ones just create more noise for already stretched teams.
The tradeoff between open source and commercial threat intelligence feeds is not simply free versus paid. It is about depth, validation, specialization, and operational fit.
Open source intelligence is strong when you need:
That is why open feeds are common in smaller SOCs, research teams, and mature enterprises that want to enrich internal telemetry without depending entirely on one vendor.
Commercial intelligence often provides:
For many teams, the practical answer is hybrid. Use open sources for broad enrichment and known bad infrastructure, then layer commercial intelligence where deeper validation or strategic context matters more.
Not all security teams use external intelligence the same way. Some treat feeds as simple blocklists. Others use them to enrich alerts. The strongest programs use them as investigative starting points that connect to broader threat activity.
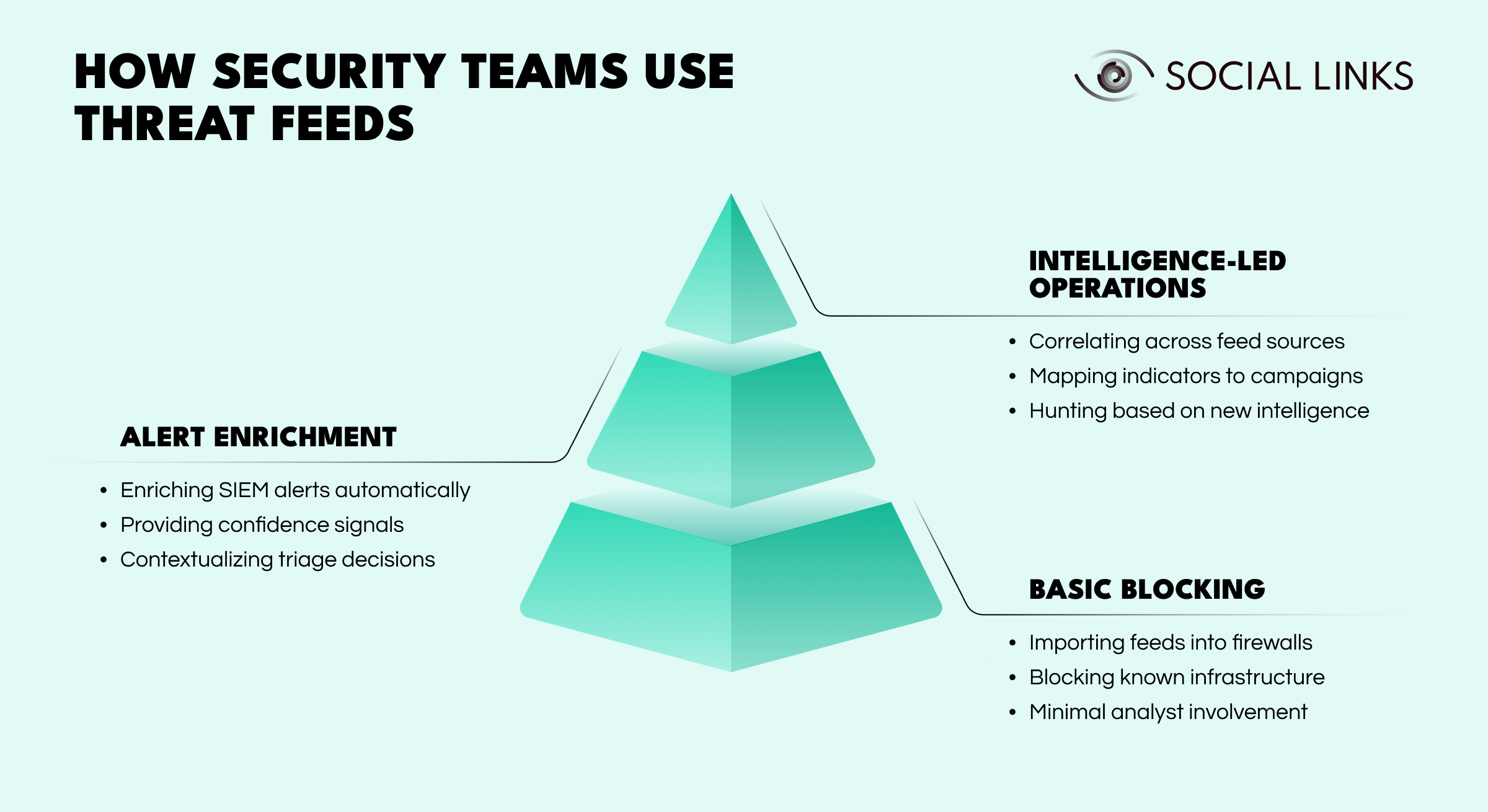
These differences matter because they shape what threats can be caught and how quickly teams can respond.
At the most basic level, teams consume feeds as static blocklists for perimeter defense.
This usually involves:
This works well for obvious threats and is easy to operationalize. But it also creates blind spots. If a feed lags behind a campaign or an actor rotates infrastructure quickly, the control becomes reactive by design.
As programs evolve, teams begin using feeds to add context to internal alerts rather than just blocking indicators at the edge.
This level often includes:
This is where external intelligence starts reducing analyst uncertainty. The team is no longer just asking whether an IP should be blocked. It is asking whether the alert is tied to known malicious activity and whether it deserves escalation.
The limitation is that enrichment still tends to focus on individual indicators. It improves triage, but it may not reveal how related indicators fit together or what campaign they belong to.
At the most advanced level, teams use feeds as entry points into broader analysis. The goal is no longer just to recognize a known bad indicator, but to understand the infrastructure, behavior, and campaign behind it.
This level often includes:
Instead of treating each indicator as the end of the story, analysts treat it as the beginning.
In practice, the difference shows up quickly. A feed can either block one bad IP or help uncover a whole campaign, and it is rarely the feed itself that determines which. Take a suspicious external IP seen in internal telemetry. At the most basic level, the IP appears in a blocklist feed, traffic is blocked automatically, and the event is logged. That may stop one connection attempt, but it also ends the investigation before it really begins.
A more mature program treats that same IP differently. Analysts query multiple sources, see that it is tied to a known campaign targeting their sector, pivot to related infrastructure, and discover additional domains already communicating with internal systems. Hunting reveals earlier reconnaissance activity. What started as one indicator becomes evidence of a wider intrusion path.
That is the real value of intelligence-led operations: they help teams move from consuming indicators to understanding the activity behind them.
There is no universal best list, because the right source depends on your use case. But a few stand out consistently.
abuse.ch remains one of the most useful names in open source threat intelligence, especially for malware infrastructure and related observables. Its value comes from being practical and actionable rather than overly broad.
Key resources include:
These are especially useful in hunting, enrichment, and malware-focused workflows.
AlienVault OTX remains one of the best-known community-driven sharing environments. It is useful for teams that want shared pulses, indicators, and collaborative enrichment without standing up a full intelligence program of their own. It is not always the cleanest source, but it is still widely used as a starting point for IOC validation and community visibility.
If you are choosing platforms rather than individual feeds, the short list usually starts with MISP and OpenCTI.
MISP is one of the most practical open source choices for collecting, storing, distributing, and sharing structured threat data.
Why teams like it:
For many teams, MISP is the most straightforward way to move from static indicators to collaborative intelligence operations.
OpenCTI is better suited to teams that need relationship-rich intelligence rather than just indicator management. It is designed to organize and visualize intelligence as a connected knowledge base.
Why teams use it:
If MISP is often strongest for structured sharing and IOC workflows, OpenCTI is often stronger for deeper relationship modeling and intelligence analysis.
The right source depends less on popularity and more on whether it fits your workflow.
Ask a few practical questions:
For example:
That is why “top feeds” is slightly misleading. A source can be excellent and still be the wrong fit for your environment.
Feeds are often used to flag known bad IPs, domains, URLs, or hashes in live telemetry. This is the easiest use case to operationalize and the most common place teams start.
In the SOC, external intelligence helps analysts triage alerts faster. If an indicator already appears in a trusted source, the analyst starts with a stronger basis for prioritization.
Hunting teams use external intelligence to search retrospectively across logs, network telemetry, and endpoint artifacts. Even if the original alert was missed, known observables can surface related activity.
During response, feeds help teams pivot from one confirmed artifact to related infrastructure, malware indicators, or prior sightings. That can speed up scoping, containment, and follow-on analysis.
Open feeds are useful, but they have clear limits.
The main limits are predictable:
Some open sources are great for enrichment but not reliable enough for automatic blocking. Others are useful only when paired with analyst review. That does not make them weak. It just means teams need to be realistic about what they are good for.
The biggest mistake is assuming that more feeds automatically mean better detection. Usually, it just means more triage unless the sources are curated, prioritized, and tied to a real workflow.
The best external intelligence sources are the ones your team can actually operationalize. In practice, that usually means a mix of tactical feeds, community-driven sharing, and platforms that add structure rather than just more indicators.
Programs that progress from basic blocking to alert enrichment to intelligence-led operations get more value from the same sources because they treat feeds as investigative starting points, not just lists to consume.
For most teams, open source intelligence is not a full replacement for commercial coverage. It is, however, an extremely valuable layer. MISP, OpenCTI, AlienVault OTX, and abuse.ch resources such as URLhaus, MalwareBazaar, and Feodo Tracker all play different roles in that ecosystem. Used well, they strengthen detection, support incident response, improve hunting, and give SOC teams better context for faster decisions.
Threat intelligence feeds are structured streams of security data that provide indicators of compromise such as malicious IPs, domains, URLs, hashes, and related context. Teams use them to improve detection, enrichment, hunting, and incident response.
Open source feeds can be very useful for SOC operations, especially for enrichment, hunting, and IOC validation. They are most effective when curated and combined with internal context rather than used as blind blocklists.
For most teams, the first platforms worth evaluating are MISP for sharing and IOC workflows, OpenCTI for graph-based context, and tactical sources like URLhaus or MalwareBazaar for malware-related observables.
Open source intelligence is often community-driven, flexible, and cost-effective, but it may require more validation and curation. Commercial sources usually provide stronger analyst support, confidence scoring, and industry-specific relevance.
Mature programs move from basic blocking to alert enrichment to intelligence-led operations. They treat feeds as investigative starting points that connect to campaigns, infrastructure, and attacker behavior rather than just lists of indicators.
Want to see how intelligence platforms help teams move beyond blocklists? Book a personalized demo with one of our specialists and discover how SL Crimewall helps security teams correlate external intelligence, enrich alerts, map related infrastructure, and support threat hunting through integrated analytical workflows.