Top 10 OSINT Tools, Products, Solutions and Software for 2022


When OSINT began life in the 1940s, the ‘open data’ under scrutiny was limited to media such as newspapers and radio broadcasts. But in the advent of the internet – and social media in particular – the sheer variety and volume of information pouring into the public domain has been staggering.
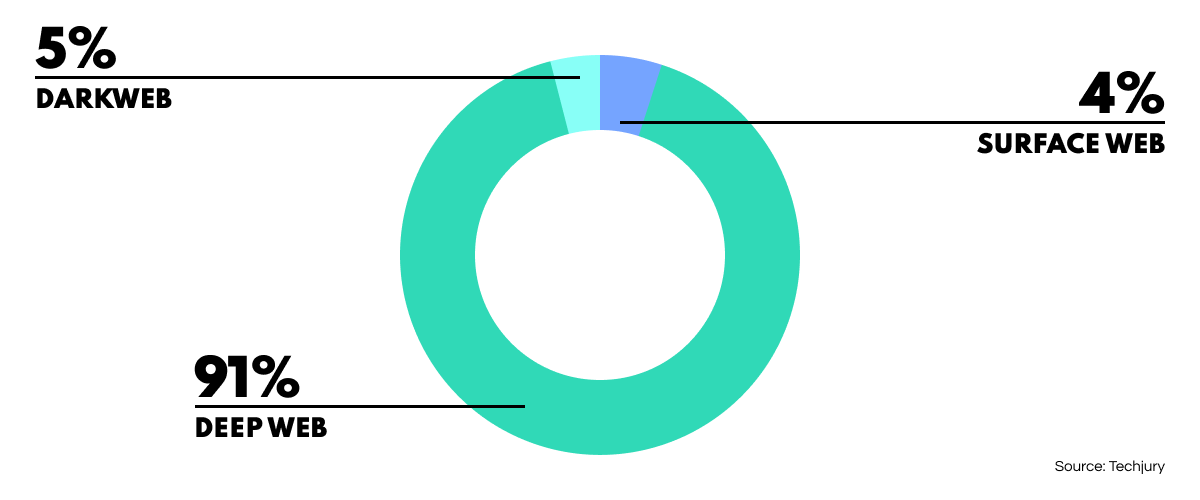
Yet, while the potential this offers for research and OSINT is vast, the process of extracting and analyzing such oceans of information has turned out to be a colossal task. Not to mention the fact that only 4% of the internet is actually indexed by Google; the rest can only be accessed through specialized systems.
With analysts needing software tools to facilitate their work, developers the world over have been clamoring to provide solutions for almost every OSINT application under the sun. This has created a booming industry traversing various spheres, but with so many options out there, it can be hard to know where to start looking for the OSINT solution that best suits your organization.
So, today we’re discussing why such tools are so useful, and giving you our pick of the top open-source intelligence tools on the market right now to help you navigate the field and choose the solution that best suits your OSINT needs.
The Necessity of OSINT Tools
The Advantages of Modern OSINT Tools
Top 10 OSINT Solutions in 2022
Broadly speaking, OSINT tools come in the form of software solutions that empower analysts to extract, correlate, visualize and analyze open data. They have the capability to accomplish a lot of the nitty-gritty legwork, so investigators, security analysts and other specialists can focus on the global goals of their work and not get bogged down in routine OSINT tasks.
While the practical utility and scope that open data offers the analyst is undeniable, the immense, diverse, and unverified nature of the raw material poses significant challenges to OSINT professionals. After all, information is being uploaded at a rate of knots. According to Statista, the global datasphere size has more than doubled since 2019, and is forecast to show a further 58% increase by 2024.
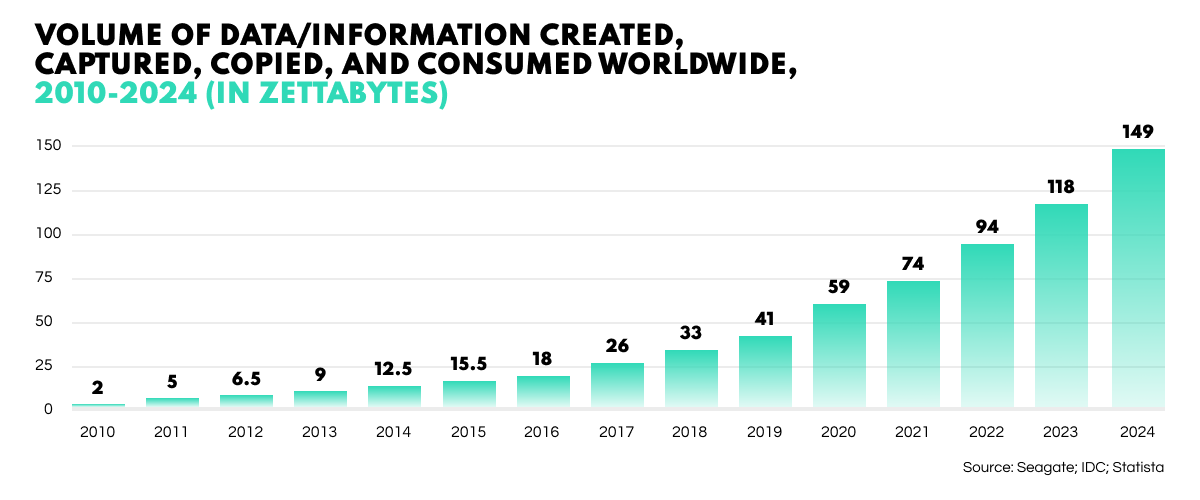
While such proliferation is inevitably useful to researchers, the fact remains that the more information there is, the harder it is to consolidate, map, visualize, and analyze. This is where OSINT tools come into play. By allowing the channeling and productive analysis of this information, open-source intelligence tools are empowering organizations to streamline processes, save resources and achieve unprecedented objectives.
OSINT tools offer multiple benefits that can revolutionize processes and totally transform the quality of investigation results. Here’s how.
When dealing with huge volumes of raw data, a major obstacle to deriving a clear picture is noise. Put simply, this refers to superfluous data which muddies or obscures the material you actually need. As a rule of thumb, the more clutter in your informational image, the less likely you are to gain the results you require.
By providing a vast array of parameters, OSINT tools give users advanced dynamic control over the way they extract information. This makes for a far clearer picture overall and can uncover details which may be an absolutely essential piece in the puzzle – a single link which clinches an entire investigation.
Even when search methods have been suitably refined via OSINT tools, the results will often still need to be vetted in some way. For example, you may have collected all images from a particular network, but now need to scour masses of visual material for evidence of a particular object such as a weapon. Carried out manually, such a process would be prohibitively time-consuming and laborious.
However, OSINT solution developers create dedicated machine learning algorithms for such purposes. These are particularly helpful when source material is not text-based but images, video, or music. In applying these AI models, the user merely sets the parameter and lets the algorithm do the heavy lifting, freeing up time and headspace for another task.
What assurances do you have that the data you have extracted is reliable? The digital realm is notoriously deceptive with a perpetual influx of misinformation, propaganda, false credentials, impersonated accounts, fake identities, misnomers and so on. And whatsmore, information has a remarkably short shelf-life. A connection or statistic that was true last week may be totally erroneous by now.
A huge benefit of OSINT tools is how they can facilitate data authenticity and provide accurate, up-to-date information. This is because OSINT solutions can draw from such a wide variety of sources in thoroughly cross-checking data. Whatsmore, such technologies can perpetually monitor the digital landscape to ensure the analyst stays cognizant of any changes that may have occurred.
OSINT boasts a significant range of different applications and can be used to achieve a number of goals. While many products overlap in their essential functionality, they also often vary in focus and design to suit different demands. The following list includes our personal pick of top osint tools, products and solutions available now.
Our top pick is a full-cycle, standalone OSINT platform—SL Crimewall. This is an all-in-one solution that simplifies the entire intelligence cycle, from data extraction through visualization and analysis to the final report. Offering a sleekly designed, user-friendly interface and a huge array of search methods developed from the ground up, SL Crimewall is an industry-leading solution in terms of capability and operability.
Product Features
An enterprise-grade on-premise OSINT solution with customization options, private data storage, and our widest range of search methods. Conceived for use by major intelligence organizations, this unique product provides a comprehensive suite of tools for all OSINT applications.

Product Features
A Java application that runs on Windows, Mac and Linux, Maltego is a graphical link analysis tool and open-source intelligence platform used to gather and connect information for investigative tasks. With its intuitive interface and extensive array of plug-ins, this OSINT visualization software helps businesses, LEAs and governmental bodies from around the globe to achieve their investigation goals.

Product Features
A cutting-edge program for conducting effective data analysis, this solution has gained huge traction across the OSINT sphere. i2 is open-source intelligence software that arms analysts with the data fusion and multi-dimensional options they need to create actionable intelligence in detecting, disrupting, and defeating sophisticated threats.

Product Features
A superb data visualization tool for professionals who want to automate open-source intelligence processes. The application is leveraged for many OSINT objectives including threat intelligence, asset discovery, attack surface monitoring and security assessment.

Product Features
The world's first search engine for internet-connected devices, Shodan allows users to discover a range of server types from power plants, mobile phones, refrigerators and Minecraft servers. The platform also enables you to monitor all connections you have to the online realm and receive real-time notifications when something unexpected shows up.

Product Features
A hugely effective time-saver, Hunchly is a program that automatically tracks the URLs, timestamps, and hashes connected to every web page you visit during an investigation. This saves you hours upon hours in documentation time so you have more time for performing investigative OSINT work.

Product Features
A user-friendly, intuitively designed OSINT platform for creating reliable digital footprints, Pipl cross-references and connects online data from countless independent sources to build digital identities with the highest degree of integrity.

Product Features
Operating for over a decade, this powerful OSINT solution collects, structures, and analyzes threat data from all over the internet, converting vast nebulous information into actionable insights. Extracting data from text, imagery, and technical sources, the Intelligence Graph uses machine learning to process and map links across billions of entities in real-time, helping analysts achieve their OSINT aims.

Product Features
A user-friendly but powerfully effective tool designed for the initial stages of a penetration test or red team engagement. Geared towards determining a company’s external threat landscape, this OSINT solution draws from multiple open sources to gather emails, names, subdomains, IPs and URLs to check a company’s IT perimeter for vulnerabilities.

Product Features
And that concludes our OSINT tool recommendations for 2022. Whether your specialist area is based in the public or private sector, we hope that these solutions give you some food for thought with regards to the huge potential OSINT tools can offer your organization.