Forensic Cyber Security: Investigating Distributed Breaches


Modern breach investigations rarely involve a single server in a locked room anymore. When Change Healthcare suffered a ransomware attack affecting more than 190 million people in 2024, investigators had to trace activity across cloud workloads, identity systems, third-party connections, and hybrid infrastructure spread across multiple environments. Stolen credentials instead of malware, SaaS platforms instead of local endpoints, temporary cloud infrastructure instead of persistent servers. Evidence fragmented, timelines disconnected, and investigators spending as much time finding evidence as analyzing it.
In this article, we examine how modern investigations actually work when infrastructure is distributed, why identity-centric attacks create different forensic challenges than traditional malware, and what changes when the evidence investigators need sits across systems with different owners, retention policies, and access controls.
Traditional digital forensics was built around a relatively simple assumption: evidence lives on systems the organization owns and can directly examine.
That assumption no longer holds in many environments.
A modern cyber security forensic investigation may require investigators to collect and correlate evidence from on-premises endpoints and servers, multiple cloud providers, SaaS platforms like Microsoft 365 or Slack, identity and authentication systems, third-party vendor infrastructure, and containers and orchestration platforms.
The problem is not just scale. It is fragmentation.
An attacker might compromise a Microsoft 365 account, pivot into a cloud workload, exfiltrate data through a storage bucket, and later move into a connected third-party environment. None of that evidence sits in one place. Investigators have to piece together logs from different systems, each using different retention policies, timestamp formats, and visibility models.
This becomes especially difficult in multi-cloud and hybrid environments, which roughly 87% of enterprises now use. Each cloud provider maintains separate logging systems, uses different API structures for evidence retrieval, and enforces different retention policies. What takes minutes to image from an on-premises server might take days to request, export, and correlate from multiple cloud platforms.
This is where many investigations start breaking down. Teams may have the technical skill to investigate the incident, but the evidence needed to understand the full scope was never centralized to begin with.
Cloud infrastructure changes some of the assumptions traditional forensic workflows relied on for years.
Ephemeral infrastructure. Many cloud workloads are temporary by design. Containers spin up and disappear within minutes. Auto-scaling environments terminate systems automatically. Serverless functions may only exist during execution. By the time investigators realize a compromise occurred, the affected infrastructure may already be gone. Traditional digital forensics assumes systems remain available long enough for imaging and analysis. Cloud environments often work the opposite way. Evidence disappears unless teams preserve it during the incident itself.
Limited direct access. Investigators cannot physically access cloud infrastructure the same way they can access on-premises hardware. Cloud providers control the underlying systems, which means investigators usually depend on whatever telemetry the provider exposes through APIs, logging services, or administrative tooling. Hypervisor access, raw storage visibility, or low-level network telemetry may not be available at all. That creates blind spots investigators simply have to work around.
Distributed ownership. Security teams manage endpoints. Cloud engineering teams manage infrastructure. SaaS administrators manage productivity platforms. Identity teams manage authentication systems. During a breach investigation, all of those teams may need to coordinate simultaneously. This becomes difficult quickly, especially when operational pressure pushes teams toward containment before evidence preservation is complete. Systems get rebuilt, credentials are reset, and cloud resources are terminated while investigators are still trying to understand what happened.
Misconfiguration and visibility gaps. Roughly 23% of cloud security breaches stem from misconfigurations, and approximately 82% are caused by human error rather than technical flaws. Investigators regularly discover that critical logs were never enabled, retention periods were too short, or telemetry was disabled to reduce storage costs. Nearly a third of cloud assets are neglected entirely, with outdated operating systems or no patches applied in over 180 days.
For years, cyber forensics focused heavily on malware analysis. That is still important, but many modern investigations revolve around identity instead.
Around 61% of breaches are now linked to compromised credentials or phishing, and identity-based techniques drove initial access in roughly 65% of incidents. Attackers increasingly rely on stolen credentials, session hijacking, MFA fatigue attacks, and token theft rather than traditional exploits.
When valid credentials are used, the forensic picture changes completely.
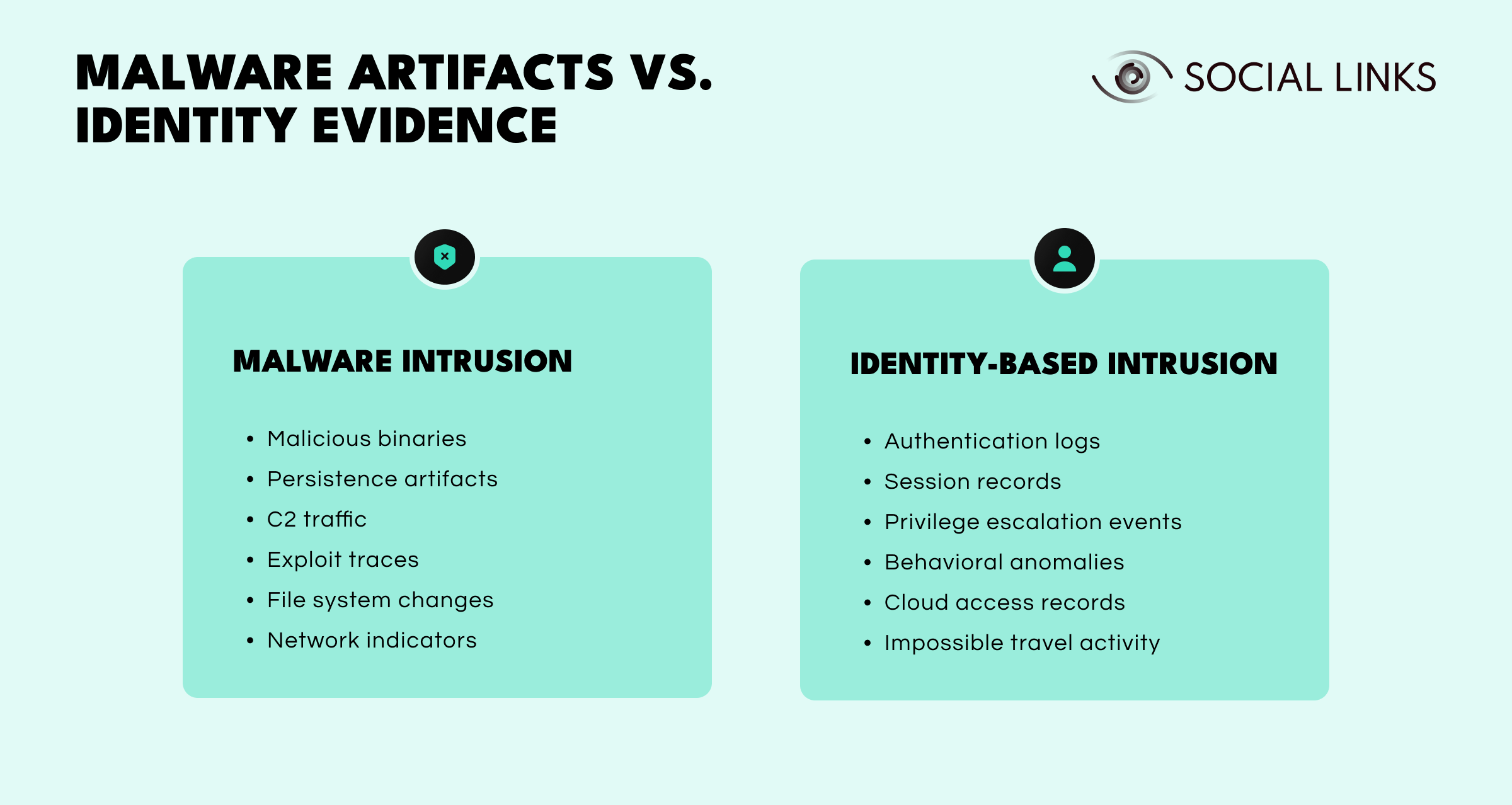
No malware to analyze. There may be no malicious executable, no persistence mechanism, no exploit artifact, and no suspicious binary to reverse-engineer. The evidence instead sits inside authentication logs, session activity, cloud access records, and behavioral anomalies such as impossible travel patterns, where the same account authenticates from geographically distant locations within timeframes that would be physically impossible. This makes investigations harder because malicious activity and normal user activity often generate the same types of events.
Longer dwell times. Credential-based compromises linger undetected for around 292 days on average, compared to roughly 200 days for other attack vectors. Attackers operating with legitimate access can move more quietly across environments, escalate privileges gradually, and blend into routine administrative activity. Investigators often discover these compromises months after the initial access occurred. By then, the attacker may have already moved across cloud environments, SaaS platforms, VPN infrastructure, and third-party systems.
Cross-environment movement. Identity systems connect modern infrastructure together. A compromised Microsoft 365 account may also provide access to federated cloud services, connected SaaS applications, internal VPN environments, and shared authentication providers. Investigators have to trace activity across every connected system while determining whether actions represent legitimate user behavior or attacker activity using stolen credentials. That is significantly harder than identifying malware on a single endpoint.
Roughly 30% of breaches now involve third parties, vendors, or supply chain partners, and these create a different kind of investigative challenge because critical evidence may sit entirely outside the affected organization's visibility.
The 2024 Snowflake breach highlighted this problem clearly. Organizations affected by the incident needed to determine what data attackers accessed, how credentials were compromised, whether credentials were reused elsewhere, and what other connected systems were affected. But much of the relevant forensic evidence existed within systems controlled by external providers. Investigators became dependent on vendors for infrastructure logs, investigative timelines, access records, and breach scope confirmation. That dependency creates delays and uncertainty.
When breaches involve multiple third parties, subcontractors, or interconnected SaaS environments, the complexity increases even further. Organizations may not have direct visibility into the full attack chain at all.
One of the hardest parts of distributed investigations is correlating activity across disconnected systems. Investigators may need to combine endpoint telemetry, cloud audit trails, SaaS activity logs, identity provider records, network traffic, and application-specific logging. Each source may store timestamps differently, retain logs for different periods, and record events with different levels of detail.
This creates timeline reconstruction problems quickly. Investigators often discover that logs expired before the investigation started, timestamps are inconsistent across systems, activity appears in one platform but not another, and retention policies vary significantly between environments.
Without a reliable timeline, even basic questions become difficult to answer: when did the attacker first gain access, how long were they active, what systems were affected first, and whether the incident was actually contained. This is why log analysis forensics and correlation work have become central to modern investigations.
Organizations that investigate distributed breaches successfully usually share several operational characteristics.
Centralized logging. Rather than relying entirely on platform-native logging, effective organizations centralize telemetry wherever possible. This helps investigators correlate events faster, normalize timestamps, maintain consistent retention, and reduce investigative blind spots. It does not eliminate fragmentation entirely, but it makes investigations significantly more manageable.
Clear preservation procedures. Strong organizations establish when evidence preservation overrides containment pressure, who has authority to freeze cloud resources, how evidence is exported and retained, and how security and infrastructure teams coordinate during active incidents. Many investigations fail because operational recovery begins before investigators finish collecting artifacts.
Identity visibility. Because identity-based attacks are so common, effective organizations maintain authentication telemetry, privilege escalation tracking, session visibility, and behavioral baselines across their environments. Without baseline identity data, distinguishing legitimate activity from attacker activity becomes extremely difficult.
Investigation playbooks. Mature teams build playbooks for common scenarios like cloud compromise, insider threat investigation, credential theft, and third-party breaches. Playbooks do not remove complexity, but they reduce investigative startup time when minutes matter.
Most distributed investigation failures follow predictable patterns.
Evidence expires before preservation. Teams discover an incident weeks after it occurred, only to find that critical cloud logs already rotated out of retention. Investigators are left reconstructing timelines with missing artifacts and partial visibility.
Containment happens too early. Systems are rebuilt or accounts reset before investigators finish collecting evidence. Operational recovery takes priority, and the artifacts needed to understand the full scope of the compromise are gone before anyone realizes they were needed.
Visibility is fragmented. Organizations have strong endpoint telemetry but weak SaaS visibility, or detailed cloud logs but incomplete identity records. Investigations proceed with partial evidence, making scope determination unreliable and containment decisions uncertain.
Third-party coordination breaks down. When providers or vendors are involved, organizations struggle to obtain timely forensic data or clear answers about what happened on the provider side. The investigation slows while evidence continues aging out of retention.
Strong investigations are built before the breach occurs. Organizations that wait until an incident happens to figure out which logs exist, how long evidence is retained, who has access to what systems, and how cloud evidence is preserved will always be reacting from a weaker position.
Forensic readiness in distributed environments means enabling logging across cloud, SaaS, identity, and endpoint systems, centralizing telemetry where possible, defining evidence preservation procedures, documenting investigative access paths, and training teams on cloud-specific forensic workflows.
This is not just a security operations problem anymore. It is an infrastructure and architecture problem. If visibility was never designed into the environment, investigations will struggle no matter how skilled the responders are.
Modern forensic cyber security has moved far beyond imaging disks and analyzing malware on isolated systems. Today's investigations span cloud environments, identity providers, SaaS platforms, third-party infrastructure, and hybrid networks. Evidence is fragmented, temporary, and often controlled by external providers.
Attackers increasingly rely on legitimate credentials instead of obvious malware, making identity analysis just as important as endpoint investigation. Organizations that treat forensic readiness as part of infrastructure design rather than just incident response are far better positioned to investigate breaches quickly and accurately.
Those that do not will continue facing the same problem during major incidents: incomplete evidence, unclear timelines, and persistent uncertainty about whether the breach was ever truly contained.
Forensic cyber security involves investigating cyber incidents by collecting, preserving, and analyzing evidence across endpoints, cloud environments, identity systems, and network infrastructure.
Cloud environments introduce temporary infrastructure, fragmented logging, limited direct access to systems, and inconsistent retention policies that make evidence collection more difficult.
Identity-centric investigation focuses on compromised credentials, authentication activity, privilege escalation, and session behavior rather than traditional malware analysis.
Without proper evidence preservation, critical forensic artifacts may disappear before investigators can analyze them, making it harder to determine breach scope and root cause.
Forensic readiness refers to preparing systems, logging, workflows, and teams before an incident occurs so investigations can happen quickly and effectively when a breach takes place.
Want to see how OSINT and investigative workflows support distributed breach investigations in practice? Book a personalized demo with one of our specialists and discover how SL Crimewall helps investigators correlate evidence across environments, trace identity-based attack paths, and build a complete picture of breach activity through integrated analytical workflows.