Due Diligence: Closing the Verification Gap


Due diligence is often treated like a checklist. Verify identity, run sanctions checks, confirm registrations, and move on. That approach works for low-risk cases, but it starts breaking down when the real problems sit outside official records, including hidden ownership, indirect relationships, reputational issues, or operational risks that documents never fully capture. The consequences of getting this wrong show up repeatedly in M&A failures, third-party breaches, and regulatory enforcement actions.
In this article, we examine where standard verification starts to fall short, how investigators use open-source intelligence to add context, and what a practical due diligence process looks like when the goal is understanding risk rather than simply completing checks.
At its core, due diligence is about reducing uncertainty before making a decision.
Whether an organization is onboarding a customer, approving a vendor, evaluating a business partner, or preparing for an acquisition, the same questions tend to surface:
A proper due diligence process usually combines several layers of review, including document and identity verification, sanctions and watchlist checks, beneficial ownership analysis, reputational review, legal and financial assessment, and, in higher-risk cases, deeper investigative work.
The mistake is assuming these steps all accomplish the same thing. They do not.
Verification establishes a baseline. Investigation is what turns scattered information into an actual understanding of risk.
Most due diligence failures do not happen because nobody checked anything. They happen because the review was too narrow, too fragmented, or too focused on surface-level confirmation.
HP lost $8.8 billion after alleged accounting misrepresentations tied to its Autonomy acquisition came to light, a case that eventually resulted in a UK High Court ruling ordering Autonomy's founder to pay $945 million in damages. Bayer has paid more than $10 billion to settle Roundup litigation following the Monsanto acquisition, with approximately 67,000 lawsuits still pending as of 2025, after underestimating litigation exposure during due diligence. Both companies conducted extensive reviews before those deals closed. Both still missed major risks.
More than a third of modern breaches now involve vendors or partners. In many cases, those organizations passed onboarding checks without deeper scrutiny into their security posture, ownership structure, or indirect exposure.
Global money laundering flows are estimated between $800 billion and $2 trillion annually, and enforcement actions repeatedly point to gaps in AML and compliance reviews, especially when layered ownership structures or reputational warning signs were never investigated thoroughly.
The pattern is consistent: organizations often confirm what is easy to see while missing the risks sitting just outside the visible layer.
Verification matters, but it has limits.
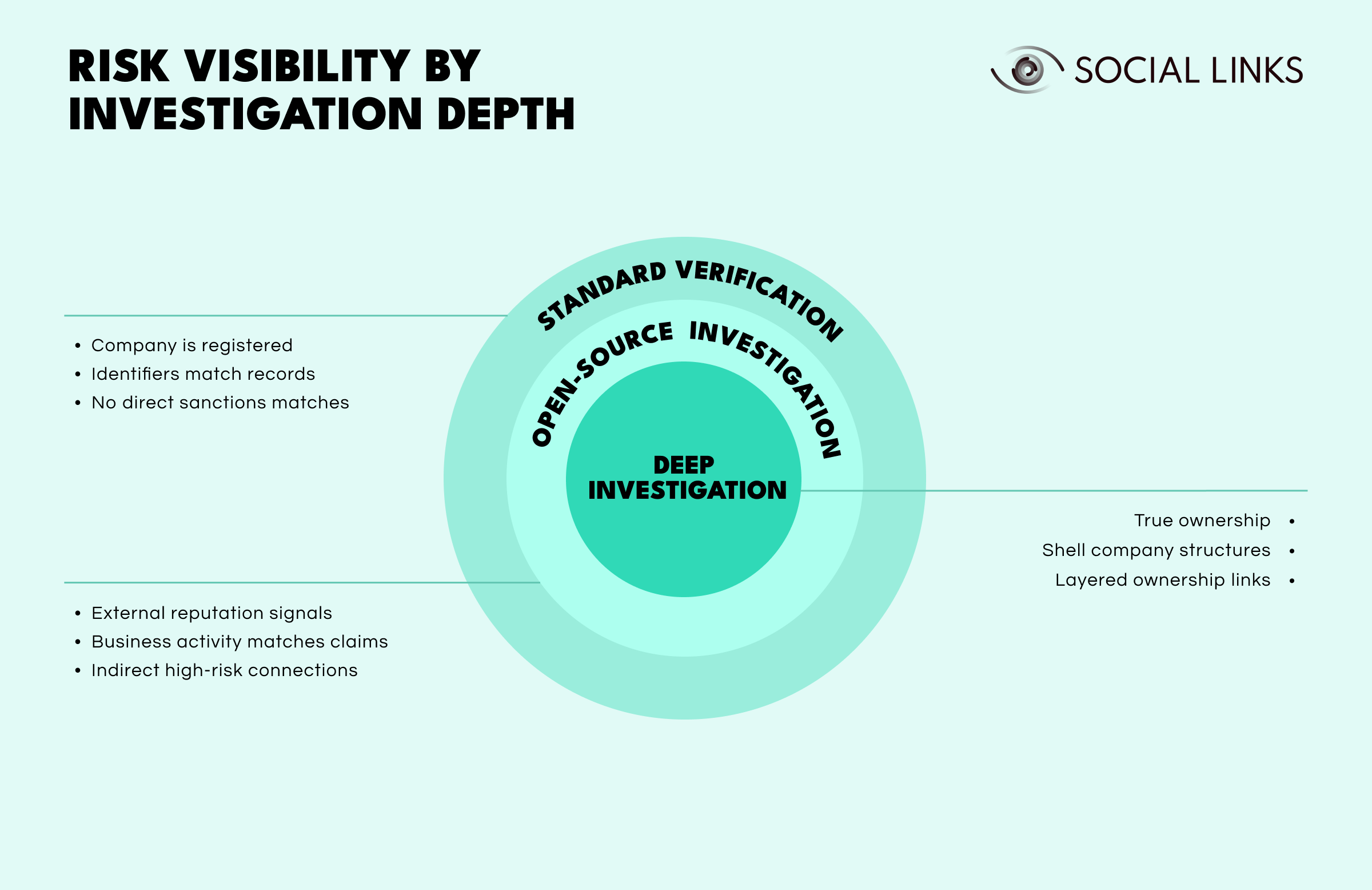
Standard verification confirms that an entity exists and matches its documentation. It checks whether a company is registered with the relevant authority, whether identifiers such as registration numbers, addresses, and directors align with official records, and whether the entity appears on direct sanctions lists.
These checks are fast, structured, and heavily automated. They are also the minimum threshold many organizations mistake for due diligence itself.
What standard verification does not answer is often more important.
Open-source investigation adds the next layer. Instead of checking only what has been declared, investigators look at whether those declarations hold up externally. That may involve:
Deep investigation goes further still. This is where investigators trace beneficial ownership through corporate registries, leaked datasets, and relationship mapping rather than relying on self-declared structures. It is where shell company networks become visible and layered ownership links are followed across multiple jurisdictions until the actual controlling party can be identified with confidence.
This progression matters because risk rarely sits at the surface. Verification is good at confirming what appears on paper. The harder part is understanding what sits underneath it. Organizations that stop at verification are not completing due diligence. They are completing the first step of it.
Internal systems show what has been declared. Open-source intelligence helps investigators determine whether those claims hold up in reality.
That additional context becomes especially valuable when:
Used properly, open-source intelligence helps investigators:
This kind of work depends heavily on validation. Public information can be incomplete, outdated, manipulated, or simply wrong. Good investigators cross-check sources carefully, resolve entities methodically, and avoid treating every negative mention as meaningful evidence.
Open-source intelligence does not replace verification. It helps explain the broader story behind it.
A practical due diligence process usually moves from simple verification into progressively deeper analysis.
Every investigation starts with understanding the decision being made, the entities involved, and the level of acceptable risk. Without proper scoping, investigations either miss important issues or waste time chasing irrelevant ones.
The first active stage focuses on core checks: identity verification, registration validation, and sanctions and compliance screening. The goal is to confirm that the entity is what it claims to be on paper.
Once the baseline is established, investigators gather information from internal systems, commercial databases, public records, and open-source intelligence sources. This is usually where the process starts moving beyond verification and into actual investigation.
This is the point where isolated facts start becoming meaningful. Investigators map ownership structures, resolve entities across multiple sources, identify indirect relationships, and examine potential shell company exposure. This stage often determines whether the review remains procedural or becomes genuinely investigative.
With findings in hand, the focus shifts from confirming entity validity to understanding what could go wrong if the relationship moves forward. That means evaluating:
Some cases require deeper review. Unclear ownership structures, adverse media findings, cross-border exposure, or inconsistencies between sources are all common triggers for enhanced due diligence.
The final stage is where a decision gets made: approve, reject, escalate further, or continue monitoring. Clear documentation matters, especially when regulatory or audit requirements become relevant later.
Most organizations still underestimate how far third-party risk extends. Direct vendors are visible and usually go through some form of onboarding review. The harder problem is what sits behind them: subcontractors, shared infrastructure providers, ownership relationships, and connected entities an organization may never knowingly work with directly.
Modern third-party reviews typically focus on:
But even strong onboarding checks only capture risk at a single point in time. Third-party breaches cost an average of $4.91 million to remediate, significantly more than internally originating incidents. The scale of the problem also keeps growing. Half of all organizations now work with more than 100 vendors, each representing a relationship that can change over time.
That is why more organizations are shifting away from one-time onboarding checks toward continuous monitoring. Risk does not stay static, and neither should the review process.
Some of the most important indicators sit outside structured databases.
Adverse media review surfaces what official records often do not. Fraud allegations, regulatory actions, corruption concerns, and repeated operational complaints frequently appear in public reporting long before they show up in formal enforcement databases. A thorough review looks beyond major English-language publications, since reputational risk often surfaces first in local reporting, regional regulatory announcements, industry-specific publications, and niche investigative reporting that automated feeds miss entirely.
Sanctions screening identifies direct exposure, but it is far less reliable at detecting indirect relationships. An entity may not appear on a watchlist while still being connected to sanctioned parties through intermediaries, layered ownership structures, or shared control. This is where screening alone creates a false sense of clearance.
Beneficial ownership analysis remains one of the hardest parts of modern due diligence. Layered entities, nominee directors, and cross-border structures make it difficult to identify who actually controls an organization. Many programs still treat ownership verification as a checkbox exercise. In practice, this is often where the most significant exposure is hiding.
Most due diligence failures follow familiar patterns, and most of them are structural rather than accidental.
Over-reliance on documents creates the illusion of thoroughness without providing much real understanding. Fragmented information across systems means investigators are rarely working from a complete picture. Ownership complexity gets underestimated because layered structures take time and skill to unravel, and both are usually limited under deadline pressure.
Investigative findings also tend to stay isolated inside separate teams instead of contributing to a shared understanding of risk. Compliance, legal, procurement, and investigative teams may all hold pieces of the picture without fully connecting them together.
Time pressure makes this worse. The stages that require the most judgment are often the first ones compressed when decisions need to happen quickly.
These weaknesses usually exist long before problems become public. Organizations often recognize the gaps only after a failure makes them impossible to ignore.
Due diligence is not just a verification exercise. It is an attempt to understand risk before decisions become expensive.
Verification confirms whether records line up. Investigation helps explain whether the broader story makes sense. Organizations that rely entirely on structured checks usually discover problems after the fact. Those that combine verification with investigation, contextual analysis, and open-source intelligence are far more likely to identify issues early, before those risks turn into financial, legal, or reputational damage.
A due diligence process typically includes identity verification, sanctions checks, ownership analysis, financial and legal review, and risk assessment. Higher-risk cases may require enhanced investigation and deeper review.
Investigators use public information to validate claims, uncover hidden relationships, identify reputational concerns, and detect risks that structured databases may miss.
Corporate due diligence focuses on acquisitions, investments, and strategic transactions. Third-party due diligence focuses on vendors, suppliers, intermediaries, and business partners.
Enhanced due diligence is usually triggered when risk indicators appear, such as unclear ownership structures, sanctions exposure, adverse media findings, or cross-border complexity.
Beneficial ownership analysis helps identify who actually controls an entity. Without it, organizations risk exposure to hidden ownership structures, shell companies, and indirect sanctions risk.
Want to see how OSINT closes the verification gap in practice? Book a personalized demo with one of our specialists and discover how SL Crimewall helps investigators verify identities, map ownership structures, and uncover hidden risks through connected investigative and OSINT workflows.