KYC and Due Diligence: Investigating Beyond Identity
The KYC process sits at the center of modern financial and compliance operations. Whether an organization is onboarding a customer, reviewing a partner, or looking into suspicious activity, KYC is meant to answer a basic question: who is this, and what kind of risk do they represent? The problem is that identity verification only gets you part of the way there. A passport can confirm a name, but it cannot tell you whether the person behind it is legitimate, whether the business is real, or whether the risk is hiding somewhere beneath the paperwork. That gap is where fraud, sanctions exposure, and compliance failures tend to appear.
In this article, we look at what KYC actually involves, where verification reaches its limits, how due diligence shifts into investigation, and how OSINT helps close the gap between confirming identity and understanding real risk.
KYC, or Know Your Customer, is the process organizations use to verify identity, assess risk, and meet regulatory requirements. It is a core part of anti-money laundering compliance, especially in financial services, fintech, and other regulated sectors.
At a basic level, KYC is trying to answer three things: who is this person or entity, are they really who they claim to be, and what level of risk do they represent?
In practice, that means more than checking a document. KYC usually combines identity verification, customer due diligence, risk assessment, ongoing monitoring, and, when necessary, investigation. The exact depth depends on the customer and the level of risk involved.
That is why KYC matters beyond compliance. Strong KYC helps prevent fraud, supports regulatory obligations, and gives organizations a better foundation for making risk decisions. Weak KYC leaves room for fraud, sanctions exposure, money laundering, and reputational damage.
Modern identity verification can confirm a remarkable amount of information in a very short time. Automated systems can validate documents, match biometric data, check databases, verify addresses, and screen against sanctions or watchlists.
That still does not mean verification tells the whole story.
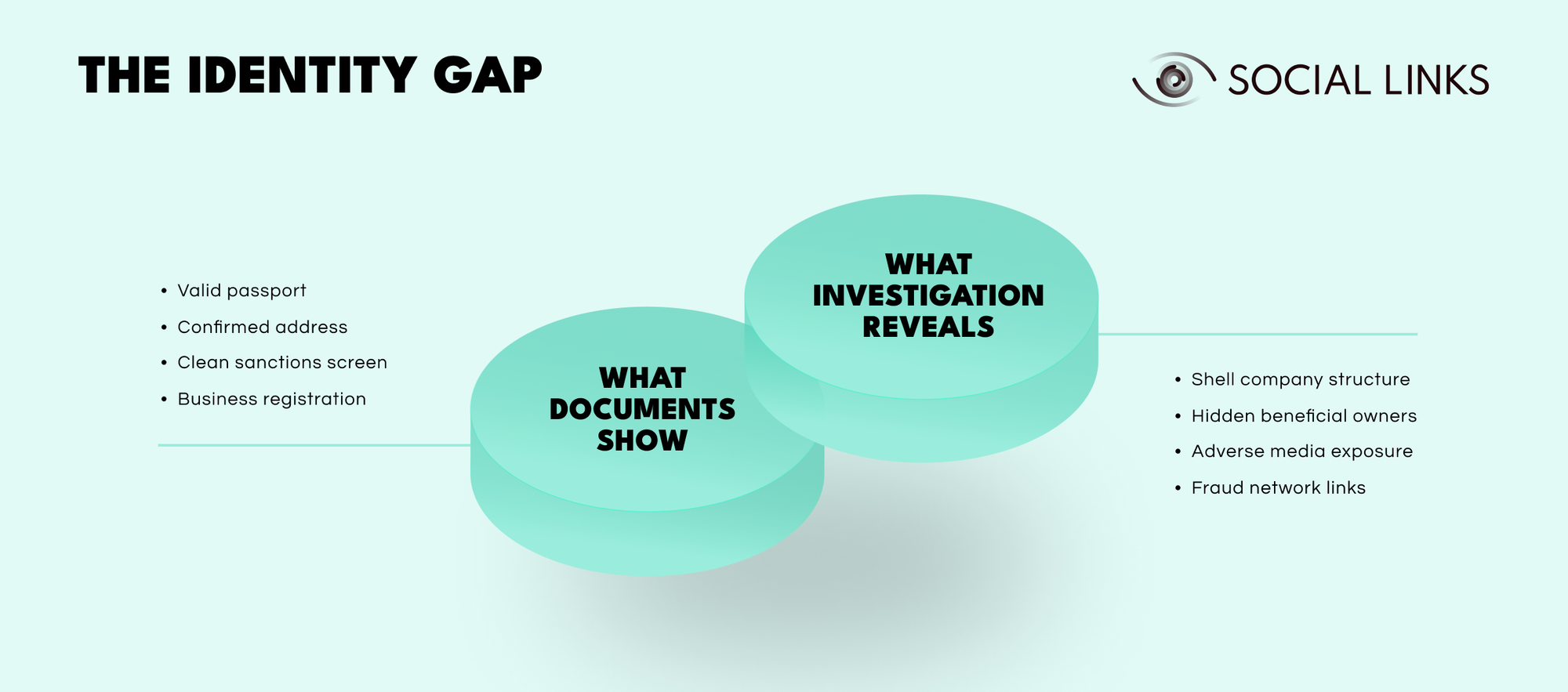
What documents show. Identity verification can confirm a valid passport, a verified address, clean sanctions screening, and proper business registration. These are important baselines. They establish legal identity and basic compliance standing.
What investigation reveals. Deeper analysis often uncovers what documents cannot show: shell company structures designed to obscure ownership, hidden beneficial owners operating behind nominees or layered entities, adverse media exposure that standard feeds missed, and fraud network links that connect seemingly clean identities to suspicious activity.
That is the identity gap. Documents confirm identity, but they do not explain context.
A verified identity confirms that someone is who they claim to be. It does not tell you why they want access to financial services, whether the business behind the documents is legitimate, what the source of funds really represents, who they may be connected to, or whether they present a broader financial crime risk.
The documents in the first layer may all be legitimate. The problems appear in the second layer, where investigation adds context that verification alone cannot provide. A passport may be genuine while the business behind it is not. An address may verify while the entity operating there is little more than a shell. A biometric match may confirm the person presenting the document, but it does not rule out fraudulent intent. A sanctions screen may come back clean while hidden relationships point in a very different direction.
This is where many KYC programs run into trouble. Automated verification is fast and scalable, but it stays close to surface identity. Investigation is slower, but it brings the context that determines actual risk. When organizations rely only on verification, that gap stays open.
KYC is not a single check. It is a workflow that starts at onboarding and continues throughout the customer relationship.
It usually begins with identity verification, where documents are validated, biometrics may be captured, and basic information is confirmed. From there, customer due diligence screens the individual or entity against sanctions lists, politically exposed persons databases, and adverse media sources while also assessing early risk factors such as jurisdiction, business type, and expected activity.
Risk assessment then determines how much monitoring or additional scrutiny is needed. In higher-risk cases, that may lead to enhanced due diligence, beneficial ownership checks, source-of-funds analysis, relationship mapping, or deeper background work.
Once onboarding is complete, the process does not stop. Ongoing monitoring tracks changes in activity, behavior, and profile. When alerts are triggered or inconsistencies start to appear, the process moves beyond verification and into investigation.
Each stage depends on the one before it. Weak verification undermines risk assessment. Weak due diligence misses red flags early. Weak monitoring allows risk to change without anyone noticing.
Not every KYC case needs the same level of depth. The difference between routine checks and deeper investigation depends on what risk signals appear and how serious they look.
Basic customer due diligence covers standard onboarding. Identity is verified, documents are reviewed, sanctions screening is completed, and basic risk factors are assessed. In straightforward, low-risk cases, that is often enough.
Enhanced due diligence comes into play when the picture becomes less clear. High-risk jurisdictions, politically exposed persons, complex ownership structures, unusual business models, or large transaction volumes all make the case harder to treat as routine. At that stage, teams need to look more closely at beneficial ownership, source of funds, relationship networks, adverse media, and whether the stated business activity holds up under scrutiny.
Investigation starts when the documents stop answering the important questions. A customer’s stated business does not match their transaction patterns. Ownership structures look more like concealment than normal corporate organization. Addresses lead to virtual offices or shell companies. Digital footprints suggest something very different from what was declared. Relationships connect to sanctioned entities, fraud networks, or suspicious counterparties.
At that point, the question is no longer whether the identity is valid. The real question becomes what is actually happening and what that means for the organization’s risk.
Identity documents are powerful tools, but they are still only one part of the picture.
They can confirm legal identity, establish nationality, provide proof of address, and support sanctions screening. That matters. But documents also have very clear limits.
A passport can confirm that someone holds a particular identity. It cannot tell you whether they are the only one using it, whether it was obtained in suspicious circumstances, what their real activities are, or who they may be acting for. A utility bill can confirm an address, but it cannot tell you whether anyone meaningfully operates there or whether the entity tied to that address is legitimate.
Business registration documents work the same way. They establish legal existence, but not operational reality. They do not necessarily reveal beneficial ownership when structures are layered. They do not prove that declared activities match real ones. They do not tell you whether the entity is functioning, dormant, deceptive, or simply a shell.
That is why document-based verification alone leaves organizations exposed. The documents may be genuine and still leave the real risk hidden.
Digital verification changed KYC by making identity checks faster, cheaper, and much easier to scale. Instead of relying on manual review and in-person checks, organizations can now use automated document recognition, biometric matching, database validation, and digital onboarding workflows.
That speed matters. Processes that once took days can now be completed in minutes.
At the same time, digital verification inherits the same basic limitation as manual verification. It is very good at confirming identity and much less useful when the real problem is understanding risk.
An automated system can verify a passport quickly. It cannot tell you whether the person’s stated business makes sense, whether transaction patterns fit the declared profile, or whether the surrounding relationships raise concerns. That still depends on investigation, correlation, and external context.
The stronger programs use digital verification for speed and scale, but they do not stop there. They pair it with investigative capacity for the cases that become more complex.
Modern KYC depends on several systems working together.
Document verification tools validate passports, national IDs, driver’s licenses, and similar credentials through image analysis, security feature checks, and database cross-referencing. Biometric systems compare faces, fingerprints, or voice patterns to confirm that the person presenting the identity is the rightful holder. Sanctions screening platforms check names and entities against government lists, watchlists, and politically exposed persons databases.
Risk scoring engines estimate fraud or financial crime risk based on factors such as jurisdiction, transaction behavior, business type, and historical patterns. Transaction monitoring systems track activity over time and flag unusual changes. Case management platforms support investigation workflows when due diligence or monitoring raises concerns.
These tools are important, but they only work well when the workflow around them makes sense. Technology produces signals. People still have to decide what those signals mean and whether they point to real risk.
KYC has gradually shifted from document-based verification toward more data-driven risk assessment. Organizations now look at transaction histories, behavioral indicators, entity relationships, and external intelligence to understand whether the profile on paper matches what is happening in reality.
That changes the nature of the work. Instead of only asking whether a passport is valid, teams start asking whether the customer’s behavior matches the profile they presented, whether transaction patterns make sense, and whether relationships or affiliations raise concerns that were not visible at onboarding.
That shift makes KYC more useful, but it also creates new dependencies. Data quality matters. Integration matters. Analytical capacity matters. If the data is fragmented, stale, or poorly connected, the conclusions will be weak. And even very good internal data still cannot fully explain what is happening outside the organization’s line of sight.
OSINT helps close the gap between verified identity and actual risk by adding outside context.
Internal systems can show a name, an address, a business description, declared transaction patterns, and submitted documents. OSINT helps test whether those things hold up in the real world.
It can expand adverse media screening beyond basic database results, surface legal proceedings or reputational issues that standard feeds missed, examine digital footprints to see whether business activity matches the claimed profile, and map relationships between individuals, entities, domains, and infrastructure that internal data never captures.
This becomes especially important in enhanced due diligence. A customer may pass document checks while public reporting points to fraud allegations, sanctions exposure, or links to financial crime. A company may look legitimate in registration records while its public footprint suggests it barely operates. An address may check out while investigation shows it is shared by dozens of shell entities.
OSINT does not replace verification. It extends KYC beyond documents and into the context that determines whether a person or entity actually carries the risk profile they appear to carry.
Even well-designed KYC programs run into the same problems repeatedly.
Data is fragmented across identity systems, transaction platforms, compliance databases, and external sources that do not fit together cleanly. Sanctions screening and name matching generate false positives that slow investigations and waste time. Fraud tactics keep changing, which means attackers adapt quickly and exploit gaps in verification with synthetic identities, stolen documents, and layered structures.
There is also constant pressure to move quickly. Organizations are expected to maintain compliance without creating unnecessary friction during onboarding. That gets harder when digital volumes rise faster than investigative teams can keep up.
At the center of all of this is the same core problem: automated systems are efficient at verifying identity, but much less effective at understanding what that identity actually represents without investigative context.
Improving KYC is less about adding more checks and more about connecting the right capabilities at the right time.
Strong programs maintain clear workflows that distinguish routine verification from enhanced due diligence and investigation. They tie identity verification directly to risk assessment instead of treating them as separate processes. They use risk-based approaches so that deeper analysis is applied where the signal justifies it, rather than slowing everything down with the same level of scrutiny.
They also combine internal transaction and behavioral data with outside intelligence, automate repetitive verification work so analysts can focus on more complex cases, and continuously adjust risk models, screening logic, and detection rules as threats and regulations change.
The goal is not rigidity. It is consistency at scale, with enough flexibility to investigate the cases that actually need depth.
Modern KYC often depends on context that internal systems cannot provide on their own, including public records, digital footprints, entity relationships, and adverse information that verification tools never see.
Social Links products help KYC teams analyze digital footprints, validate stated business activity, map relationships between individuals and entities, surface hidden connections that raise fraud or sanctions concerns, and expand adverse media screening with open-source evidence.
This is especially useful in enhanced due diligence, high-risk onboarding, and investigations where internal signals need to be tested against external reality. This helps teams move from routine verification to informed decisions when risk is less obvious.
The KYC process is moving beyond identity verification and toward risk understanding. Documents and automated checks are still essential, but they only answer part of the problem. Investigation is what explains what that identity really represents.
The most effective programs recognize the identity gap and build workflows that close it. They use verification for speed and scale, and they rely on investigation and intelligence when the case becomes more complex.
That is what turns KYC from a compliance checkbox into a real risk management capability.
KYC verifies customer identity, assesses risk, and supports anti-money laundering compliance. In practice, it combines document verification, sanctions screening, due diligence, and ongoing monitoring.
Enhanced due diligence begins when risk indicators appear, such as high-risk jurisdictions, complex ownership, politically exposed persons, or unusual business models. At that point, teams need deeper investigation into ownership, source of funds, and relationships.
Digital verification uses automated tools to validate documents, match biometric data, check databases, and screen against sanctions lists. It makes onboarding faster, but it does not resolve the deeper question of actual risk.
KYC is the broader framework for verifying identity, assessing customer risk, and maintaining compliance over time. Due diligence is the investigative layer within that framework, used to examine ownership, source of funds, business legitimacy, and other risk factors more closely.
OSINT adds outside context through adverse media, digital footprints, public records, and relationship mapping. It helps investigators test whether the stated identity and business profile match reality.
Want to see how external intelligence supports KYC investigations? Book a personalized demo and discover how SL Crimewall helps compliance teams validate identities, map entity relationships, conduct adverse media screening, and bridge the gap between verification and understanding through integrated OSINT workflows.