Digital Forensics: Racing Against Evidence Decay
The hardest part of digital forensics is rarely collecting evidence. It is collecting it before it disappears. When a breach is detected, incident response teams move to contain threats by isolating systems, resetting credentials, and blocking malicious activity. At the same time, valuable forensic evidence vanishes—memory is lost when systems power down, logs are overwritten during recovery, and attack artifacts disappear when endpoints are reimaged. Organizations face a permanent tension: the fastest way to stop an attack is often the fastest way to destroy the evidence needed to understand it.
In this article, we examine why evidence disappears so quickly, how digital forensics and incident response work together under pressure, where investigations commonly fail, how OSINT adds outside context, and what forensic-ready organizations do differently to preserve critical evidence before incidents happen.
Most breaches are not discovered immediately. According to IBM’s 2025 report, it takes organizations an average of 241 days to identify and contain a breach—181 days to detect it, then another 60 days to stop it. By the time a formal investigation begins, the most useful evidence may already be gone.
Consider a typical scenario: a security team detects unusual data transfers from a file server at 2am on a Tuesday. By the time analysts triage the alert Wednesday morning, IT has already rebooted the server to "fix performance issues." The memory that would have shown which process was exfiltrating data is gone. The network packet captures that would have revealed the destination were overwritten overnight when storage limits were hit. The authentication logs that would have shown how the attacker gained access rotated out three weeks ago because retention was set to 30 days, but the initial compromise happened two months earlier.
The investigation can prove data left the server. It cannot prove how the attacker got in, what else they accessed, or whether they still have access elsewhere. The breach disclosure will state "an incident occurred," but the organization cannot confidently answer whether customer data was involved, when the exposure began, or if the threat is truly contained.
The average breach costs $4.44 million globally. In the United States, that figure reached $10.22 million in 2025—an all-time high driven largely by regulatory penalties tied to inadequate forensic findings. The cost is not just the breach itself. It is the breach you cannot explain because the evidence is gone.
Digital evidence degrades on predictable timelines, each type disappearing at different rates:
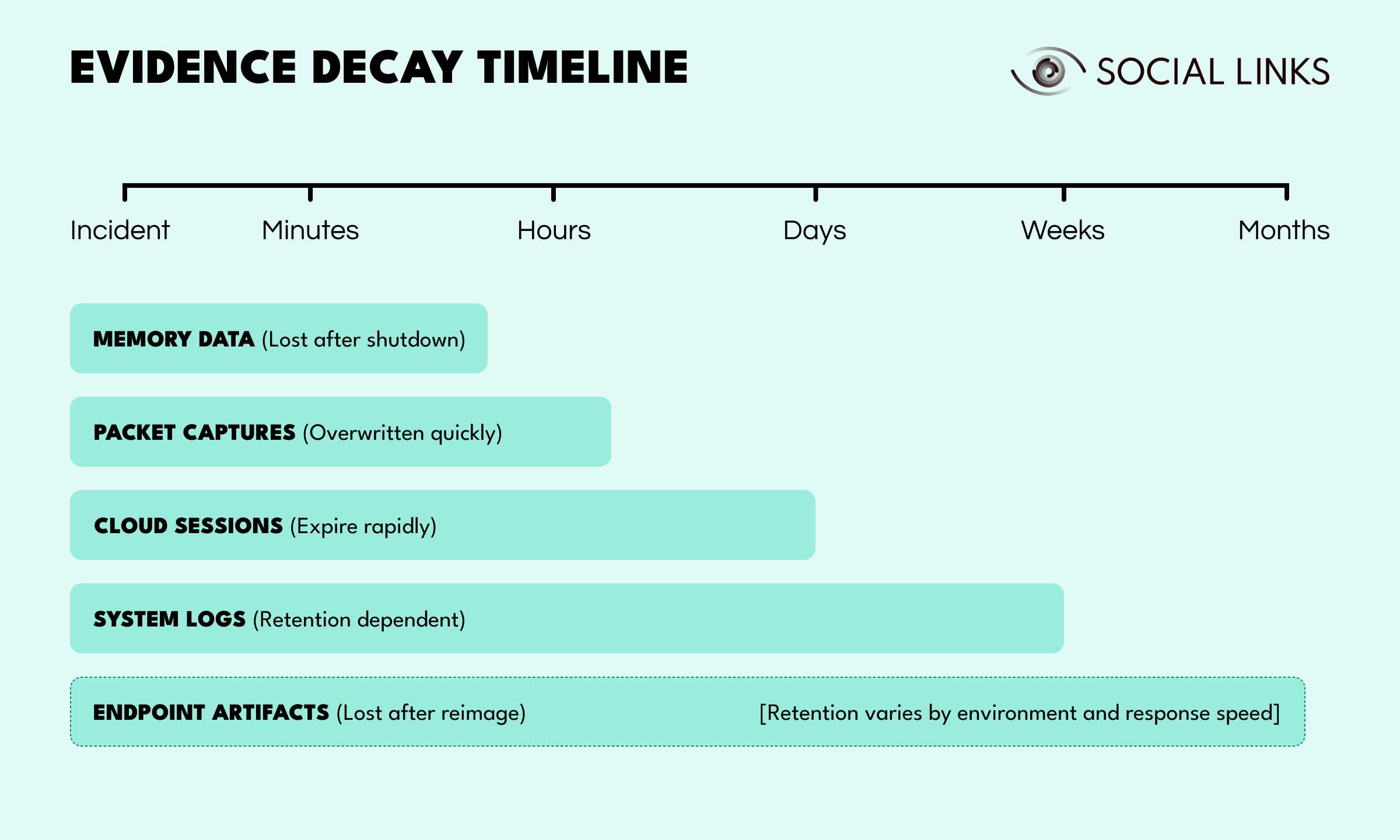
The challenge becomes much harder once evidence is spread across disconnected systems. Endpoint logs sit in one system, cloud access logs in another, network telemetry somewhere else, and mobile data behind separate tools or vendors. When evidence exists across systems that don't integrate, reconstruction becomes painstaking or impossible.
Incident response and digital forensics support the same mission, but they often operate under different priorities. This tension between speed and understanding sits at the center of modern incident response workflows.
Response teams focus on containment. When suspicious activity is detected, systems are isolated, credentials are reset, and malicious processes are stopped. Those are often the right decisions because they limit immediate damage.
Forensics teams focus on preservation and reconstruction. Memory may need to be captured before shutdown. Logs may need to be secured before accounts are reset. Network activity may need to be recorded before connections are blocked.
Only 30% of organizations regularly test their incident response plans. Even fewer have tested whether their response procedures preserve the evidence they will actually need. Most discover the conflict during a breach that requires both speed and thorough investigation—ransomware with disclosure requirements, insider theft with potential legal action, or supply chain compromise affecting customers.
Organizations with mature workflows do not treat containment and evidence preservation as competing choices. They build response procedures that preserve critical evidence first, then move quickly into containment. Organizations using AI and automation in security save an average of $1.9 million per breach, primarily by detecting incidents 51 days faster while maintaining evidence integrity.
Digital forensics spans multiple disciplines, each focused on different evidence sources with different volatility timelines.
Focuses on laptops, desktops, and servers to recover deleted files, review browser history, analyze USB usage, and reconstruct user activity. This evidence helps investigators understand what happened on individual systems.
Examines identity logs, SaaS activity, administrative changes, API actions, and data movement across cloud platforms. Cloud evidence is often distributed across providers with different retention policies.
Analyzes traffic patterns to identify suspicious communications, lateral movement, and potential data exfiltration. Network evidence is highly volatile, with packet captures often retained for only hours or days.
Investigates phones and tablets for messages, app activity, location records, authentication tokens, and user behavior. Mobile evidence often helps identify the initial compromise vector.
Captures volatile memory to identify malware, injected code, credentials, or attacker activity that may never touch disk. This is one of the most time-sensitive forms of forensic evidence.
Tracks how data was created, changed, moved, shared, or deleted. This is especially common in insider risk and intellectual property theft investigations.
Some of the hardest investigations involve people who already have authorized access. 83% of companies experienced at least one insider attack in 2024, making this one of the most common—and most challenging—investigation types organizations face.
External attackers often leave clearer indicators such as suspicious logins, exploit attempts, or known malware behavior. Insider activity is harder because legitimate access and malicious intent can look similar in logs. An employee downloading customer records may be performing normal duties or preparing theft. The technical evidence alone may not answer that question.
Investigators often need to combine access logs, file movement records, browser history, USB activity, communications data, and timelines with HR or policy context. Digital evidence can show what happened. Determining why it happened often requires broader investigation.
Third-party breaches create a related challenge. Vendors may have valid credentials and expected access, making malicious activity harder to distinguish from routine operations. 30% of all breaches in 2025 involved third parties—double the rate from just two years earlier. These investigations are complex because evidence is fragmented across organizational boundaries, and forensic authority does not extend beyond your own environment.
Internal evidence explains what happened inside the environment. OSINT helps explain what may be connected outside it.
A suspicious domain found in logs may connect to a broader phishing cluster. An email address may appear in prior breach data or fraud reports. An IP address may map to VPN infrastructure or known malicious hosting patterns.
This outside context is especially useful in:
OSINT is not a substitute for forensic evidence. Public information can be incomplete, manipulated, or outdated. Its value comes from enriching internal findings and helping investigators see patterns they would otherwise miss.
Investigations often fail because environments were designed for operations, not for investigation. Many organizations invest heavily in detection but less in evidence readiness.
Common gaps include:
These weaknesses may remain invisible until a serious incident requires legal scrutiny, regulatory disclosure, or executive-level certainty. By then, expired logs cannot be recovered retroactively. Even when evidence exists, 68% of cybercriminals now use encryption to hide their activity, making preserved data unreadable without proper decryption capabilities built into investigative workflows.
Forensic readiness means designing systems and processes so investigations remain possible when incidents occur. Organizations with mature forensic readiness reduce investigation costs, improve response quality, and handle regulatory or legal scrutiny with stronger evidence and clearer timelines.
Logging strategies should support reconstruction, not just alerting. If user activity cannot be reconstructed from available logs, additional session visibility may be necessary. If file access is not tracked, detailed audit trails become difficult to recover later.
Many breaches are discovered months after the initial compromise. In those environments, 30-day retention windows are often inadequate. Mature programs typically retain security-relevant logs far longer to support delayed investigations and timeline reconstruction.
Strong investigation programs establish evidence preservation procedures before incidents occur. Memory capture, device imaging, cloud log preservation, and evidence documentation workflows are usually predefined, with tooling already deployed and teams trained on collection procedures.
Collection authority and investigative scope are easier to manage when policies already define what can be collected, from whom, and under what conditions. Organizations that address these questions early avoid confusion during active investigations.
Digital investigations often involve security, IT, legal, HR, compliance, and leadership teams simultaneously. Mature organizations establish responsibilities and escalation paths before incidents force competing priorities into the open.
Tabletop exercises are most valuable when they test more than response speed alone. Strong programs also test whether retained evidence is sufficient to reconstruct attacker activity, establish timelines, and support decision-making under pressure.
Digital investigation is changing quickly. Cloud-native environments create shorter evidence windows. Containers terminate rapidly. Serverless workloads may leave minimal traces. Identity attacks increasingly target access tokens and SaaS platforms rather than traditional endpoints.
AI is changing both attack and defense. Attackers use automation for scale, while defenders use AI to triage evidence volumes, detect anomalies, and prioritize cases faster. At the same time, regulatory pressure is increasing. Notification windows are tightening, and expectations around evidence-backed reporting continue to rise.
The organizations that adapt early will investigate faster and decide with more confidence. Those that do not will keep discovering gaps during their worst moments.
Digital investigation and forensic computing is not mainly a tooling problem. It is a timing, evidence, and preparedness problem.
Organizations that preserve evidence early, investigate methodically, and enrich findings with outside intelligence are in a much stronger position to understand incidents and respond well. The strongest programs do not wait for a crisis to build capability. They prepare before they need it.
Digital forensics is the process of collecting, preserving, analyzing, and reporting electronic evidence from devices, networks, cloud systems, and user activity.
Incident response focuses on stopping threats and restoring operations quickly. Digital forensics focuses on understanding what happened, determining scope, preserving evidence, and supporting informed next steps.
Some evidence is volatile by nature. Memory is lost on shutdown, logs rotate, sessions expire, and systems may be rebuilt before collection begins.
Cloud evidence is distributed across providers, services, and logs with different retention rules. Access may depend on permissions, APIs, or configurations that are not ready during an incident.
OSINT helps investigators validate indicators, identify related infrastructure, map identities, detect fraud signals, and add context that internal systems alone may not show.
Want to see how open-source intelligence supports digital forensics and cyber investigations? Book a personalized demo and discover how SL Crimewall helps investigation teams correlate forensic evidence with OSINT, enrich breach investigations with outside context, and connect fragmented indicators across cloud, identity, social media, and infrastructure environments.