Risk Assessment and Management in Cyber Security: From Analysis to Action
Risk assessment and management in cyber security is often treated as a scoring exercise: identify threats, assign severity ratings, generate reports, and move on. But knowing the risks is not the same as managing them. An organization can clearly see vulnerabilities, threats, and potential impact and still struggle to act if that assessment does not lead to decisions about what to fix first, what to accept, what to transfer, and where limited resources should go. Most organizations do not lack risk data. They have too much of it. The real challenge is deciding which risks matter most and what to do next.
In this article, we explain how effective cyber risk management moves beyond scoring and reporting into practical decision-making. We break down how organizations assess risk, prioritize what matters, choose appropriate responses, and turn findings into actions that reduce real business exposure.
Risk assessment is the process organizations use to identify, analyze, and evaluate cybersecurity risks that could affect systems, data, and operations. In practice, that means identifying critical assets that need protection, including systems, infrastructure, applications, and sensitive data. It means understanding realistic threats such as external attackers, insider risks, system failures, and supply chain compromise. It also requires identifying weaknesses that could be exploited and estimating likelihood and business impact.
The result is usually a risk register, scoring model, or prioritized list of exposures. That gives the organization a clearer picture of risk. Management starts when leaders decide how to respond.
Without structured assessment, security becomes reactive. Teams chase alerts, patch whatever appears urgent, and allocate effort based on noise rather than business priorities. Assessment provides the foundation for better decisions, but only if it leads somewhere useful.
Effective assessment helps organizations identify what matters most and separate realistic threats from theoretical ones. It helps teams prioritize remediation based on actual exposure rather than technical severity alone. It also makes it easier to explain risk to leadership in terms they can evaluate and act on. The value of assessment is not the report itself. It is whether the report leads to better decisions.
Many programs stop at analysis. They measure risk well but manage it poorly.
Assessment focuses on visibility and scoring. Teams identify assets, catalog threats, review controls, score likelihood and impact, and produce reports showing risk levels across the environment. The goal is to understand what risks exist and how serious they appear to be.
Action focuses on decisions and execution. What needs immediate remediation? What can be accepted for now given the current business context? Where should security budgets go first? What risks can be transferred through insurance or contractual terms, and what risks simply need to be monitored rather than changed right away?
Assessment answers what risks exist. Action answers what the organization will do about them and why.
The most effective programs connect the two. They use assessment to support decisions, not just to produce reports.
Routine cases are straightforward. A critical vulnerability exists on an exposed system. The risk is clear, the remediation is obvious, and action follows naturally. Assessment identifies it, management fixes it.
Harder cases involve trade-offs. A production system needs patching, but downtime would disrupt revenue. Multiple serious findings exist, but only some can be addressed this quarter. A vendor creates risk, but replacing that vendor would damage operations or delay critical projects. Controls are available, but the cost outweighs the likely impact.
At that point, risk management becomes less about calculation and more about judgment.
Leaders have to decide which risks genuinely threaten operations, which can be tolerated temporarily, which justify immediate investment, and which should be transferred or reduced later when resources allow. A scoring matrix can label a risk “high.” It cannot decide whether addressing it now is smarter than addressing something worse, or whether the business can live with that exposure for a limited period.
Effective cyber risk management usually moves through three connected stages.
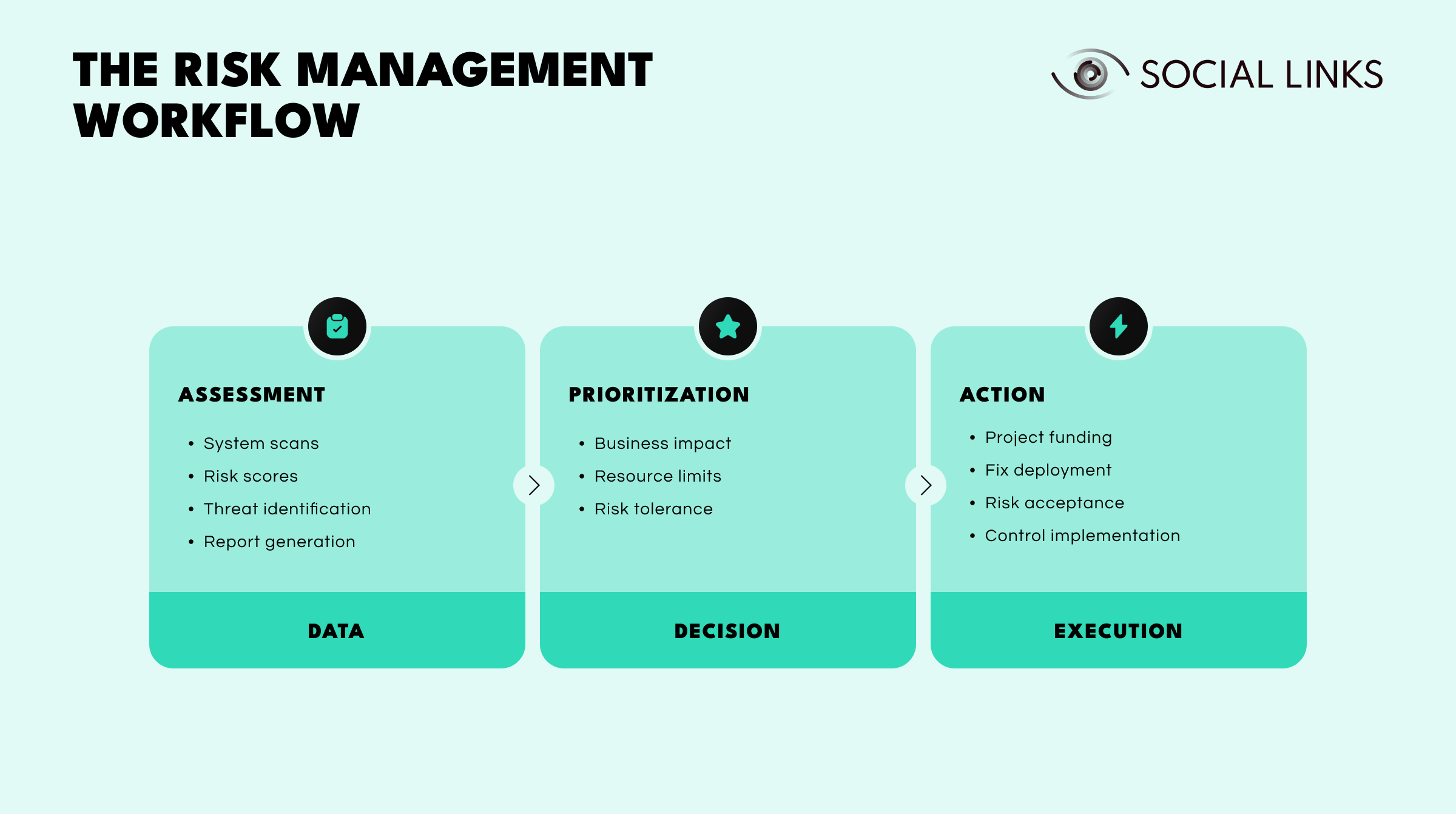
Assessment creates visibility. Teams gather data through system scans, threat identification, control reviews, and risk scoring. This stage produces the raw picture of exposure, but it does not yet tell the organization what to do first.
Prioritization turns visibility into decision-making. Risks are weighed against business impact, resource limits, and risk tolerance. This is the stage where organizations decide which issues require immediate remediation, which can be monitored, and which may need formal acceptance or transfer.
Action turns decisions into execution. That may mean funding security projects, deploying fixes, implementing new controls, or documenting risk acceptance where mitigation is not practical. This is the stage where risk management becomes operational rather than analytical.
In practice, each stage serves a different purpose: assessment gathers facts, prioritization sets direction, and action reduces exposure. If any stage breaks down, the organization may understand its risks without ever reducing them.
Organizations use different methods depending on what they need to decide.
Quantitative assessment uses financial or numerical estimates to model potential loss and justify security investments in business terms.
Qualitative assessment uses descriptive ratings such as low, medium, or high when precise quantification is difficult or unrealistic.
Scenario-based assessment tests specific threat events such as ransomware attacks, insider data theft, or supply chain compromise to understand how existing controls would respond.
Control-based assessment measures current safeguards against defined standards or frameworks to identify coverage gaps.
Each method has limits. Quantitative models can look precise while relying on uncertain assumptions. Qualitative ratings are easier to apply but introduce subjectivity. Scenario exercises can be valuable but take time and effort to run properly. Framework-based reviews align with standards but may miss risks that fall outside the checklist. Strong programs combine methods rather than relying on one.
Once risks are assessed and prioritized, organizations must decide how to respond. Risk mitigation strategies usually fall into a few categories.
Risk reduction lowers likelihood or impact through controls such as patching vulnerabilities, strengthening authentication, segmenting networks, or improving monitoring.
Risk transfer shifts financial or contractual exposure to other parties through cyber insurance, vendor contracts, or service agreements.
Risk avoidance removes activities or systems that create unacceptable exposure, such as retiring vulnerable legacy systems or discontinuing high-risk practices that cannot be adequately secured.
Risk acceptance means deliberately tolerating residual risk when impact is low, when mitigation costs exceed likely loss, or when other risks are more pressing.
The goal is not to eliminate all risk. It is to choose the response that makes the most sense for the business, its resources, and its risk tolerance.
Even mature programs struggle to convert assessment into action. Several recurring challenges explain why good assessment processes can still produce weak outcomes.
Too many risks, not enough resources. Vulnerability scans identify thousands of findings across the environment. Security teams cannot fix everything at once. Prioritization requires judgment about what actually matters, but scoring models do not always capture business context or operational constraints.
Technical severity is not business impact. A critical vulnerability in a test system is not the same as the same vulnerability in a production payment system. Assessment tools may score them identically, but the real-world implications are different.
Constant change. New vulnerabilities appear daily. Threat actors adapt. Systems and dependencies change. An assessment completed last quarter may already be outdated. Continuous assessment helps, but it also creates more data that needs to be turned into decisions.
Unclear ownership. Assessment identifies risks, but the decision-making authority is often less clear. Technical teams can recommend controls, but they cannot always make business trade-offs. Leadership may accept risks, but not always with full technical understanding. When no one clearly owns the decision, risks get assessed but not managed.
Process without judgment. Many organizations follow established frameworks such as NIST or ISO 27001 closely. That helps create structure, but frameworks do not make trade-offs for you. They guide process. They do not decide what matters most in your environment.
Effective programs move beyond scoring into governance and execution.
They define clear risk tolerance and acceptance criteria so teams know when to escalate decisions and when to handle issues within their authority. They prioritize based on business impact, not just technical ratings, so remediation efforts focus on what actually threatens operations.
Strong programs connect assessments to planning and budgeting so identified risks become funded security initiatives rather than findings that sit in reports. They assign clear ownership for decisions about mitigation, acceptance, or transfer, so accountability exists when risks materialize. They document accepted risk formally and review it regularly to make sure the underlying conditions have not changed.
They also treat risk assessment as continuous rather than occasional, recognizing that risks evolve as systems, threats, and priorities change. Most importantly, they communicate risk in business language leadership can understand and act on.
Risk assessment often requires context that exists outside internal systems, including threat actor behavior, infrastructure relationships, third-party legitimacy, and intelligence that helps distinguish theoretical risks from real ones.
Social Links helps security teams validate external threats by correlating internal indicators with infrastructure patterns visible through open source intelligence, assess vendor and partner exposure through digital footprint analysis and entity relationship mapping, investigate incidents to understand scope and attribution when risks materialize, and support threat hunting by identifying connections that internal tools miss.
This is particularly useful when organizations need to distinguish theoretical risk from real-world relevance, when third-party relationships require validation beyond vendor disclosures, and when incidents require understanding whether risks were isolated or part of coordinated campaigns. Social Links does not replace vulnerability scanners or risk scoring platforms. It extends risk assessment by adding external context that improves prioritization and decision-making.
Risk assessment is not the same as risk management. Assessment helps organizations understand where risk exists. Management is the process of deciding what to address now, what can wait, and what level of exposure is acceptable.
Organizations that focus only on assessment often end up with reports, registers, and open issues that never translate into action. Stronger programs use assessment as a decision tool. They weigh business impact, work within real constraints, and make deliberate trade-offs.
That is how analysis becomes action.
Risk assessment identifies assets, threats, vulnerabilities, likelihood, and impact so organizations can understand which cybersecurity risks create the greatest exposure to business operations.
Assessment identifies and evaluates risks based on defined criteria. Management decides whether to mitigate, accept, transfer, avoid, or monitor those risks based on business priorities, available resources, and organizational risk tolerance.
Assessment becomes action when findings lead to funded remediation plans, documented risk acceptance decisions, clear ownership and accountability, or prioritized resource allocation rather than just reports and scores.
Risk management is difficult because organizations face limited resources, constantly changing threats, conflicting priorities, and decisions that scoring systems and frameworks alone cannot resolve without human judgment about business trade-offs.
External intelligence helps validate threat relevance by distinguishing theoretical risks from real-world patterns, assess third-party exposure through entity and infrastructure analysis, identify adversary behaviors and relationships, and add context that internal scanning and monitoring tools cannot provide.
Want to see how external intelligence supports risk assessment? Book a personalized demo and discover how SL Crimewall helps security teams validate threats, assess third-party risk, investigate incidents, and add context to risk decisions through integrated OSINT workflows.